Distributed target location estimation method against suspicious data
A target location, distributed technology, used in the field of communication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] The present invention will be described in further detail below with reference to the accompanying drawings and examples.
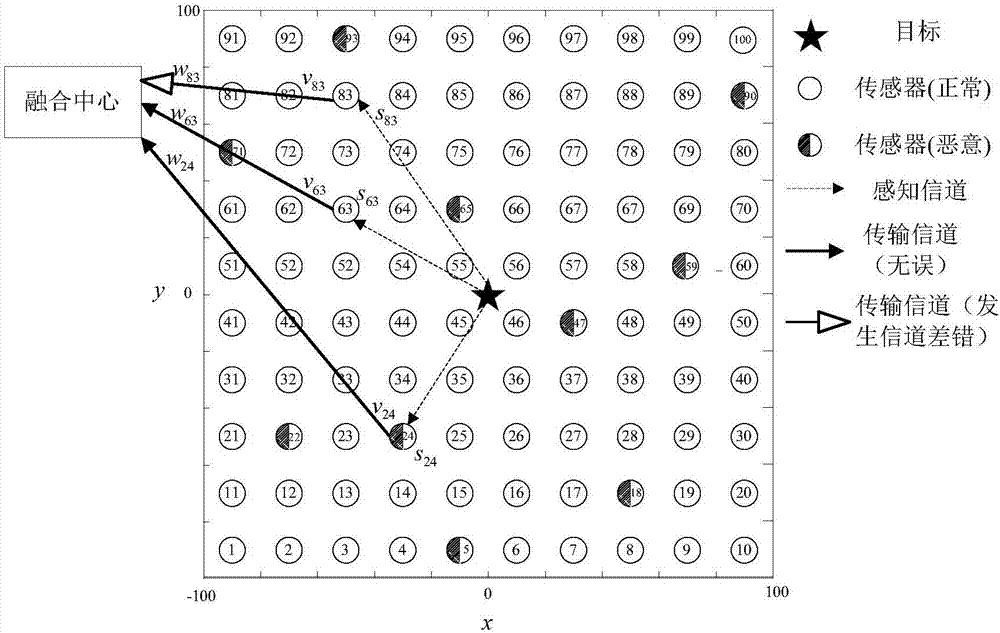
[0041] This example works in a wireless sensor network, such as figure 1 As shown, N sensors are deployed (in this example, the area where sensors are deployed is a square area of 200×200, N=100, and N is usually used to make the sensors densely distributed in the area), of which k are malicious sensors (in this example k=10). target such as figure 1 Shown by the five-pointed star.
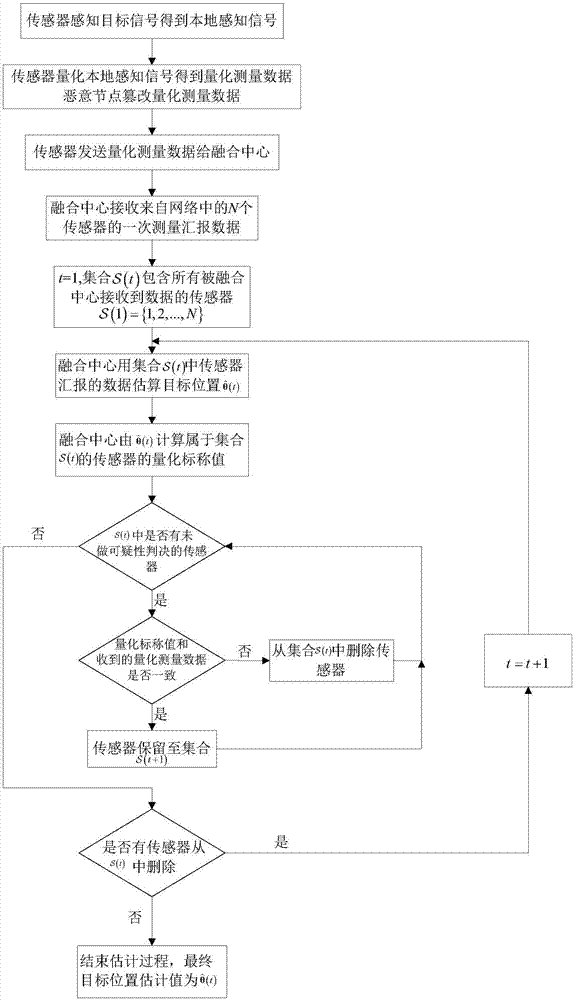
[0042] Such as figure 2 As shown, this example is implemented through the following steps:
[0043] Step 1. The sensor perceives the target signal, quantifies the perceived target signal, and then sends the processed data to the fusion center; the specific process is as follows:
[0044] (1) The sensor perceives the target signal to obtain the local perception signal:
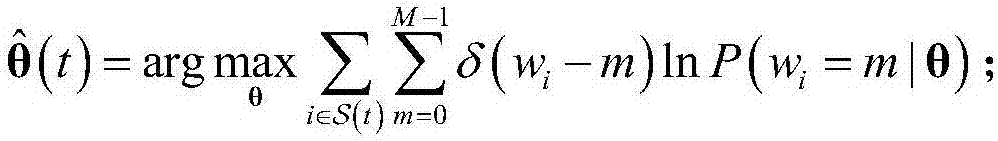
[0045] Such as figure 1 As shown, N sensors perceive the target signal to obtain the local...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More