Security detection method and apparatus for application program
An application program and security detection technology, applied in computer security devices, instruments, digital data authentication, etc., can solve problems such as potential safety hazards, slow hardening time, and inflexible selection of hardening schemes, and achieve the effect of ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0040] In the following description, for purposes of illustration rather than limitation, specific details such as specific system architectures, interfaces, and techniques are set forth in order to provide a thorough understanding of the present invention. It will be apparent, however, to one skilled in the art that the invention may be practiced in other embodiments without these specific details. In other instances, detailed descriptions of well-known devices, circuits, and methods are omitted so as not to obscure the description of the present invention with unnecessary detail.
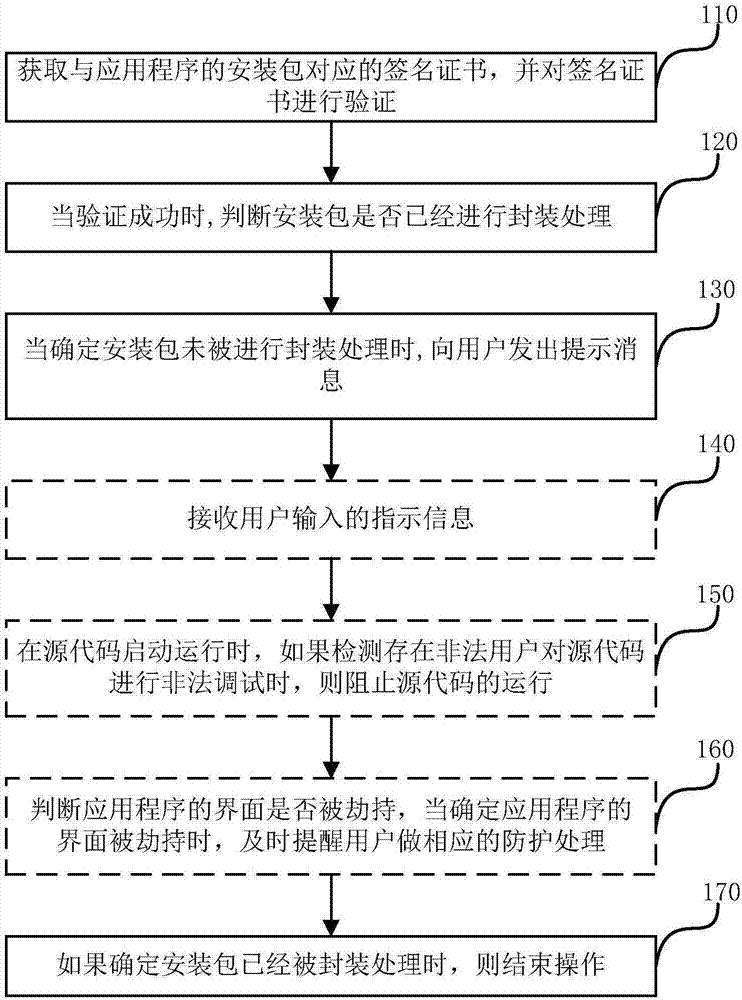
[0041] figure 1 It is a schematic flowchart of a method for performing security detection on an application program provided by an embodiment of the present invention. Specific as figure 1 As shown, the method includes:
[0042] Step 110, obtain the signature certificate corresponding to the installation package of the application program, and verify the signature certificate.
[0043] Specifi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More