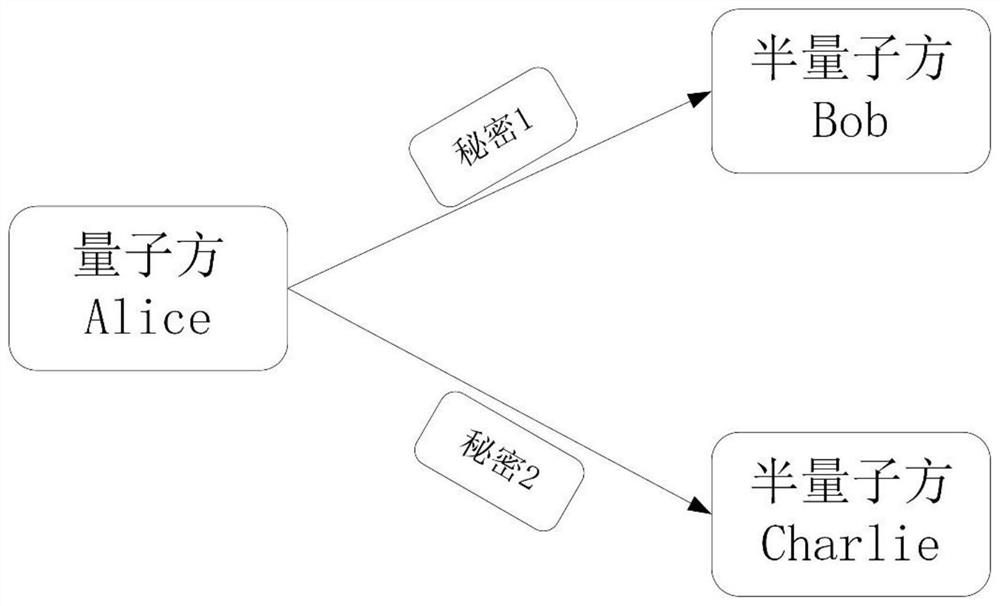
Semi-quantum secret sharing method with limited quantum resources
A quantum secret and resource-constrained technology, applied in the field of semi-quantum secret sharing, can solve problems such as threats to people's privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] 1. Preparation stage:
[0022] (1a) Alice randomly generates a string of binary numbers S, performs a specific operation on S and the secret string K that she wants to share (for example, XORing the two strings), and obtains a string R;
[0023] (1b) Alice prepares 2N |+> states, and sends N to Bob and the other N to Charlie.
[0024] 2. Sharing stage:
[0025] (2a) After receiving the |+> state sent by Alice, Bob randomly chooses to execute the REFLECT operation or the SIFT operation. Charlie's operation is similar to Bob;
[0026] (2b) After receiving the qubits sent back by Bob and Charlie, Alice randomly chooses to use the X base or the Z base for measurement, and records the measurement results and the measurement base used for the corresponding position;
[0027] (2c) After Alice has measured all 2N qubits, she discloses the measurement basis used by each qubit in sequence. Bob and Charlie disclose what they do to each qubit.
[0028] 3. Detection stage:
[...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More