Data transmission method and apparatus, and fire fighting system
A data transmission method and data technology, applied in transmission systems and key distribution, can solve problems such as security accidents and a large number of low-power IoT terminals, and achieve the effect of improving data security and ensuring credibility and authority.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
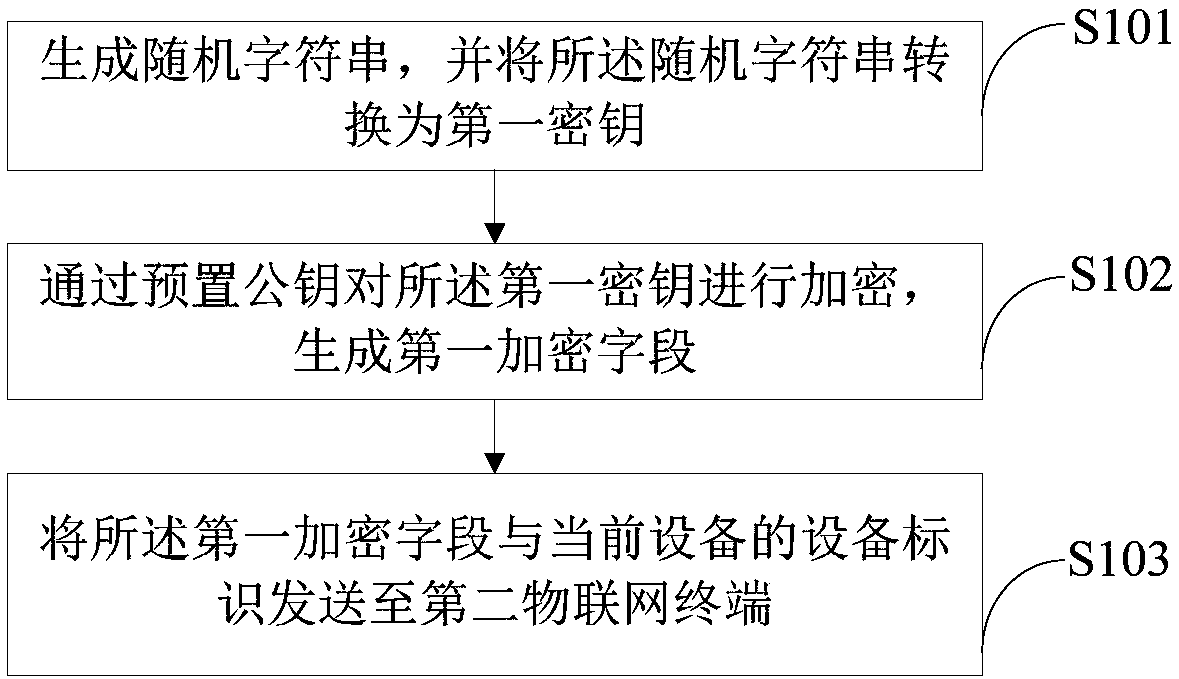
[0057] like figure 1 As shown, this embodiment provides a data transmission method, which can be applied to, for example, IoT terminals that include IoT detectors, low-power wireless communication modules, MCU modules, or other IoT terminals suitable for wireless IoT, or such as Wireless fire alarm controller, wireless IoT platform and other IoT terminals. The data transmission method provided in this embodiment includes:
[0058]S101. Generate a random character string, and convert the random character string into a first key.
[0059] In a specific application, the first IoT terminal generates a random string before data transmission, and converts the random string into an AES key, and uses the AES key as the key for subsequent encryption and decryption. When the random string is generated, The random string will not change during this data transmission. It should be noted that the user can set according to the actual situation, set each data transmission to generate a ne...
Embodiment 2
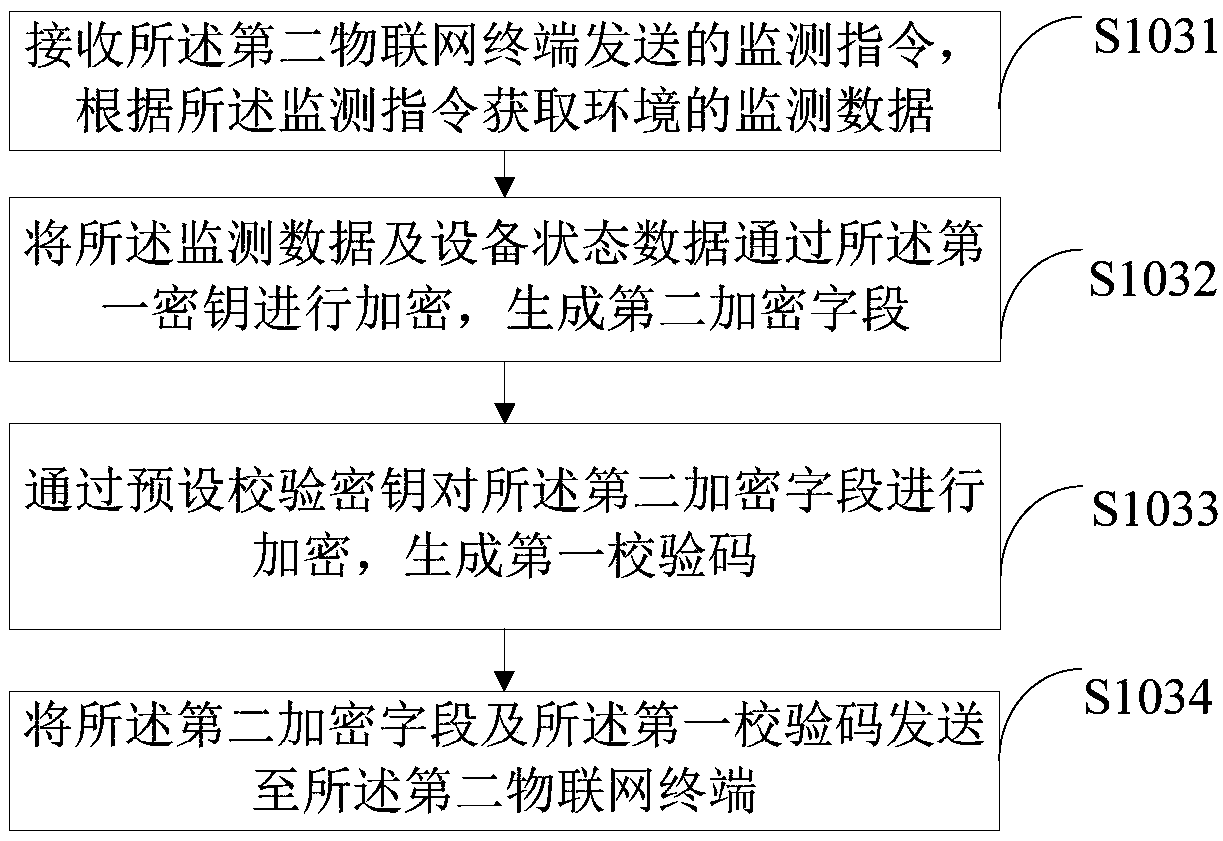
[0066] like figure 2 As shown, this embodiment is a further description of the method steps in the first embodiment. In this embodiment, after step S103, include:
[0067] S1031. Receive a monitoring instruction sent by the second IoT terminal, and acquire environmental monitoring data according to the monitoring instruction.
[0068] In a specific application, the first IoT terminal receives the monitoring instruction sent by the second IoT terminal, that is, obtains the monitoring data of the environment according to the monitoring instruction, wherein the monitoring instruction refers to controlling the first IoT terminal to monitor the first IoT terminal Instructions for monitoring the surrounding environment; monitoring data include but are not limited to smoke concentration, ambient temperature, sound and light values or other environmental monitoring data obtained by smoke sensors or other sensors.
[0069] S1032. Encrypt the monitoring data and device status data ...
Embodiment 3
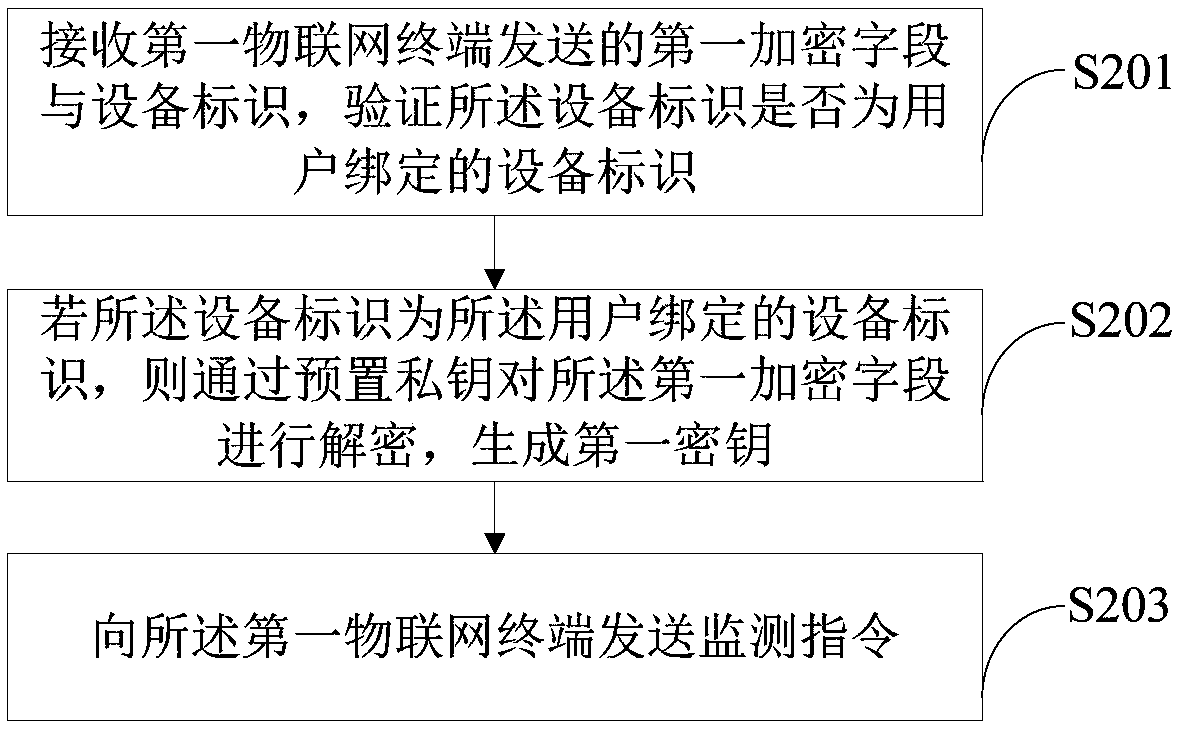
[0086] like image 3 As shown, this embodiment provides a data transmission method, which can be applied to IoT detectors, low-power wireless communication modules, MCU modules or other IoT terminals suitable for wireless IoT, or wireless fire alarms Alarm controller, wireless IoT platform and other IoT terminals. The data transmission method provided in this embodiment includes:
[0087] S201. Receive a first encrypted field and a device identifier sent by a first Internet of Things terminal, and verify whether the device identifier is a device identifier bound by a user.
[0088] In a specific application, when the second IoT terminal receives the first encrypted field and the device identifier sent by the first IoT terminal, it should verify whether the device identifier is the device identifier bound to the network access user, if the device identifier is the device identifier, it is determined that the first IoT terminal is a correct interactive IoT terminal for the cur...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap