Security configuration checking system
A technology of security configuration and system service, applied in the field of security configuration verification system, can solve problems such as lack of verification system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] The present invention will be further described below in conjunction with accompanying drawing:
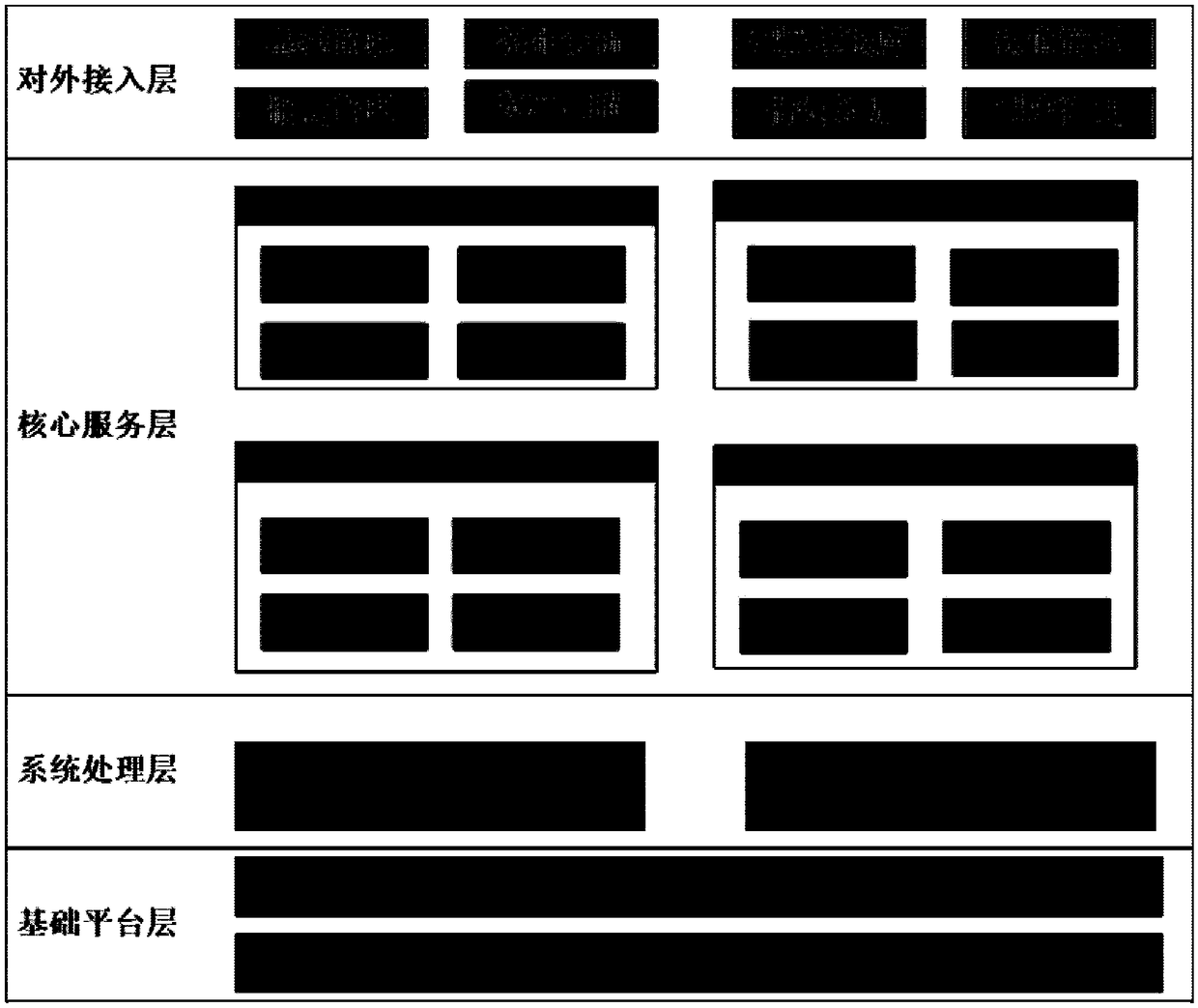
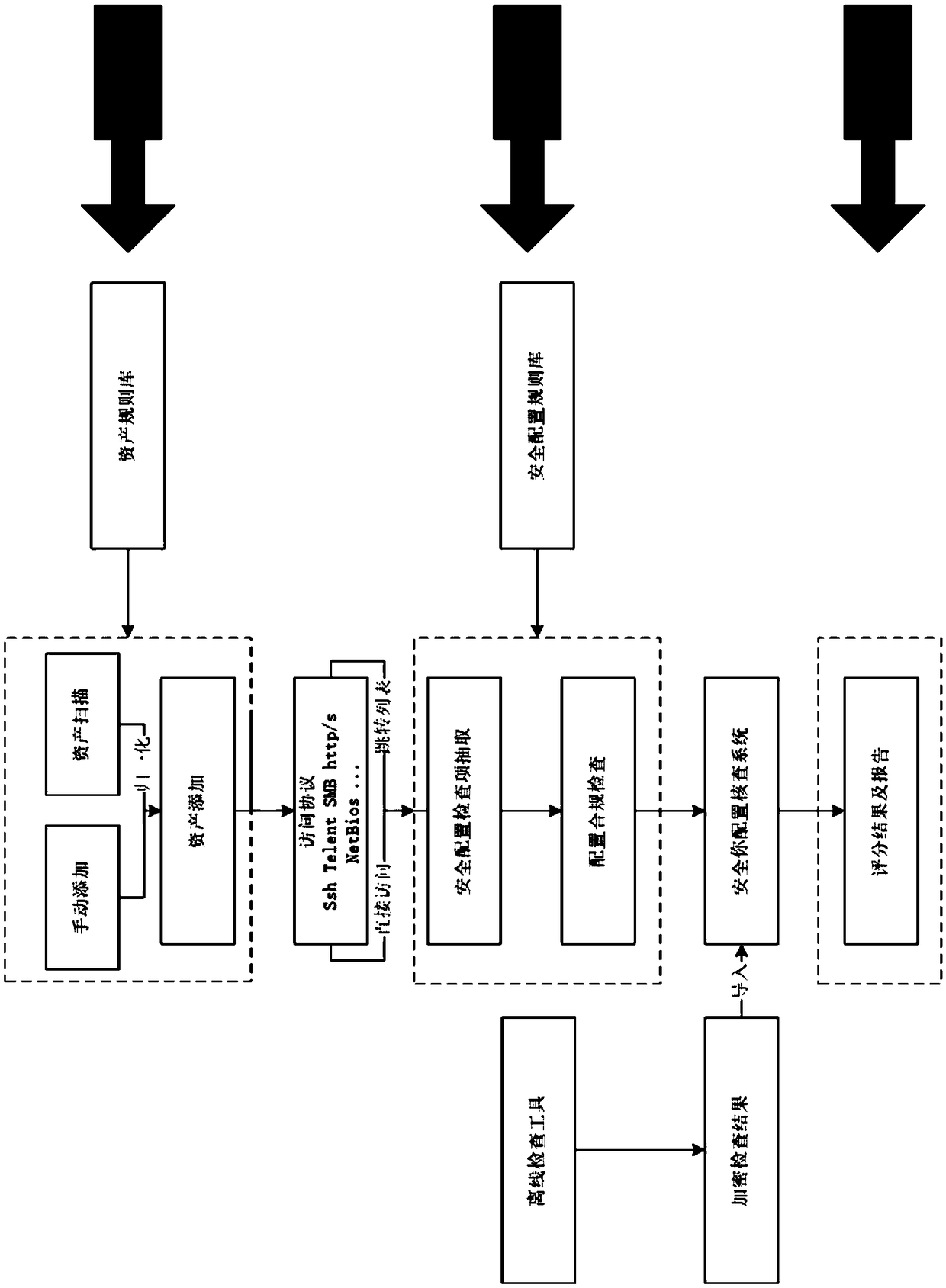
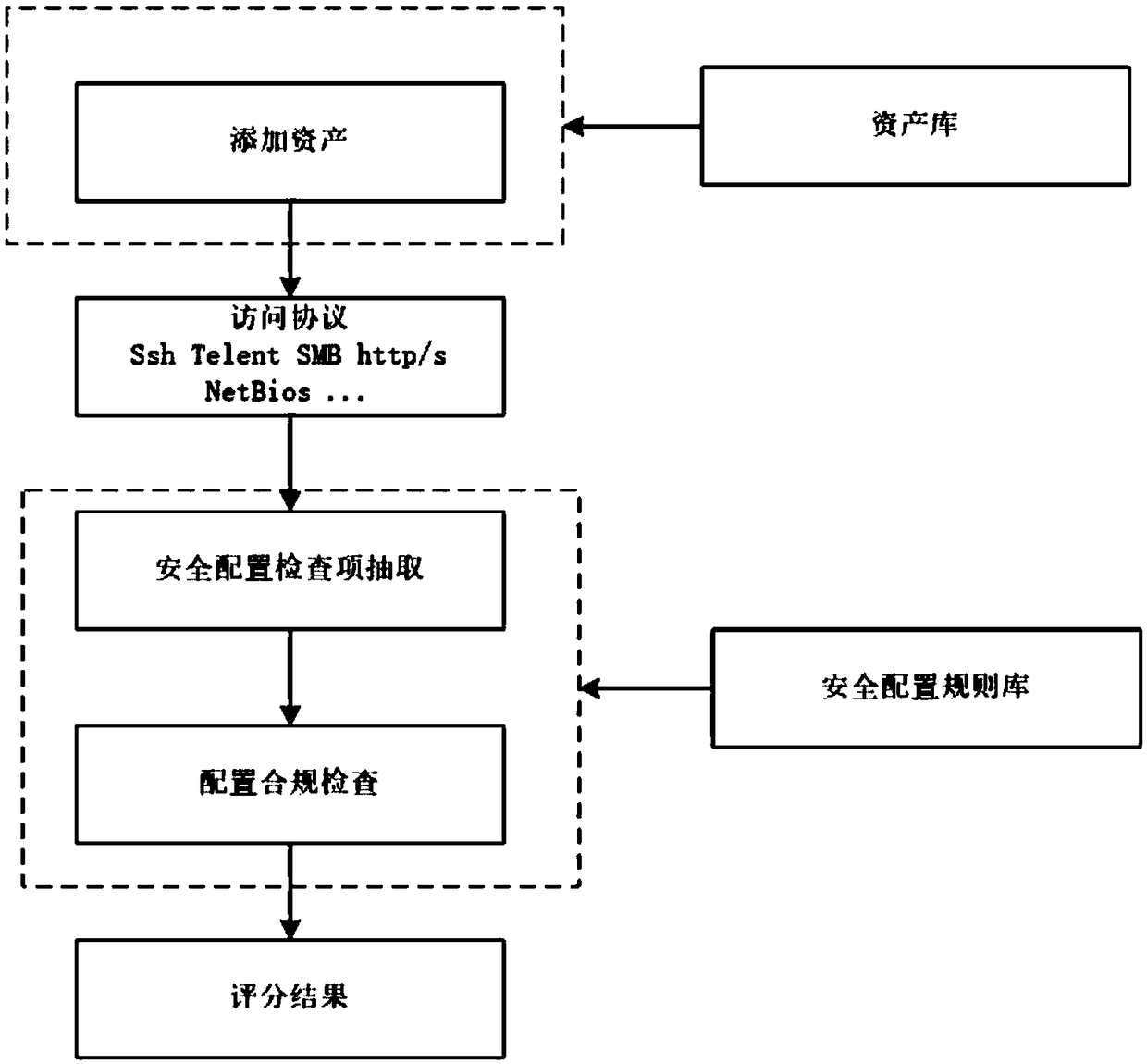
[0033] like figure 1 and figure 2 Shown: A security configuration verification system including
[0034] Basic platform, including basic software platform and hardware basic platform;
[0035] System processing layer, including data processing and system services;
[0036] Core service layer, including security configuration verification engine, report statistical analysis engine, asset scanning engine and network topology analysis engine;
[0037] The external access layer is used to display the system functions and third-party call interfaces. The function display includes security configuration inspection, asset scanning, configuration template library, report management and user management function display, and provides third-party interface calls based on webservice.
[0038] like figure 1 As shown, the system processing layer includes data processing and system ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More