SM2 dot multiplication configuration preventing side-channel attack
A channel attack and dot multiplication technology, which is applied in the application field of cryptography technology, can solve problems such as loss of practical significance and successful attack on cryptographic chips, and achieve high scalability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0055] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
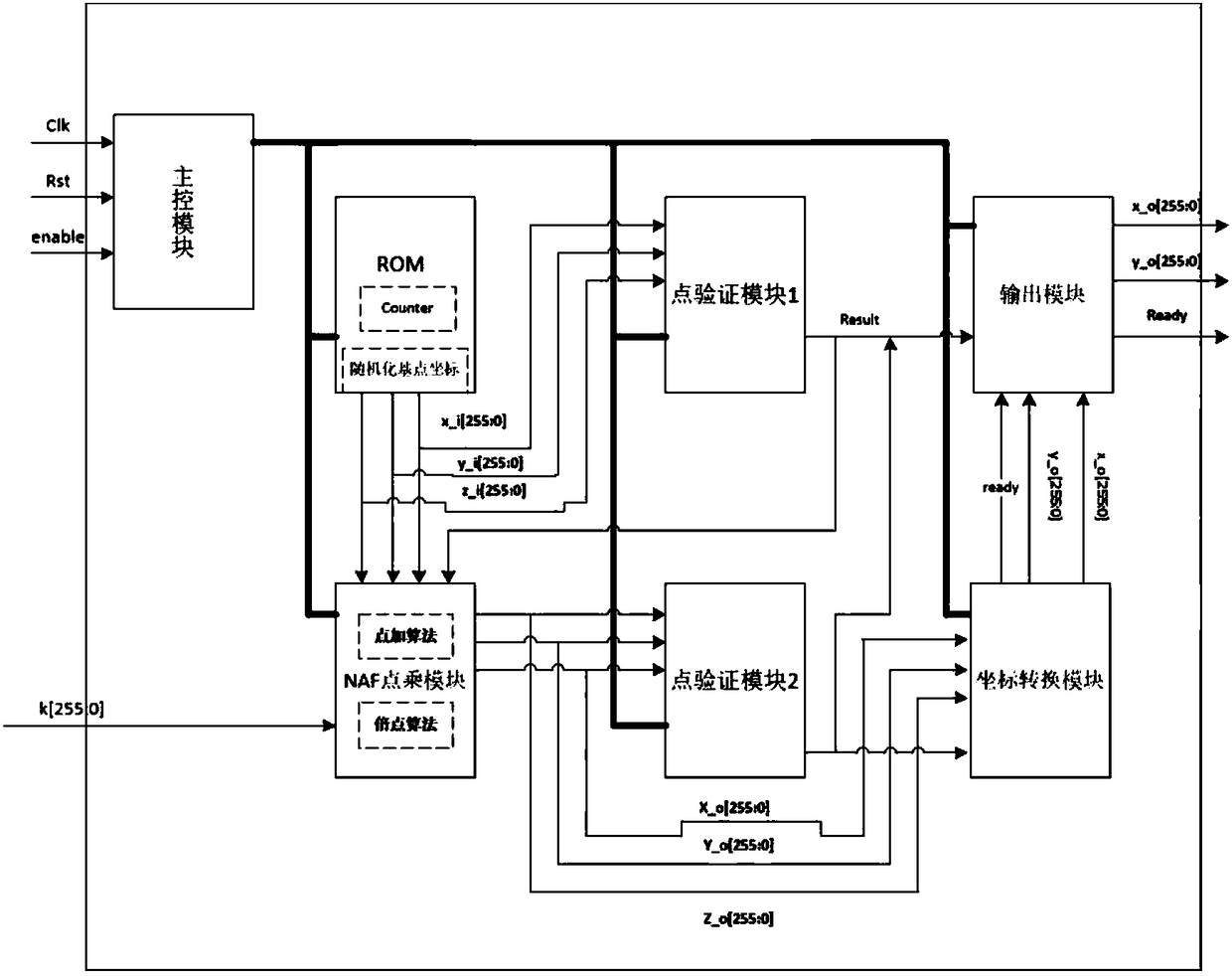
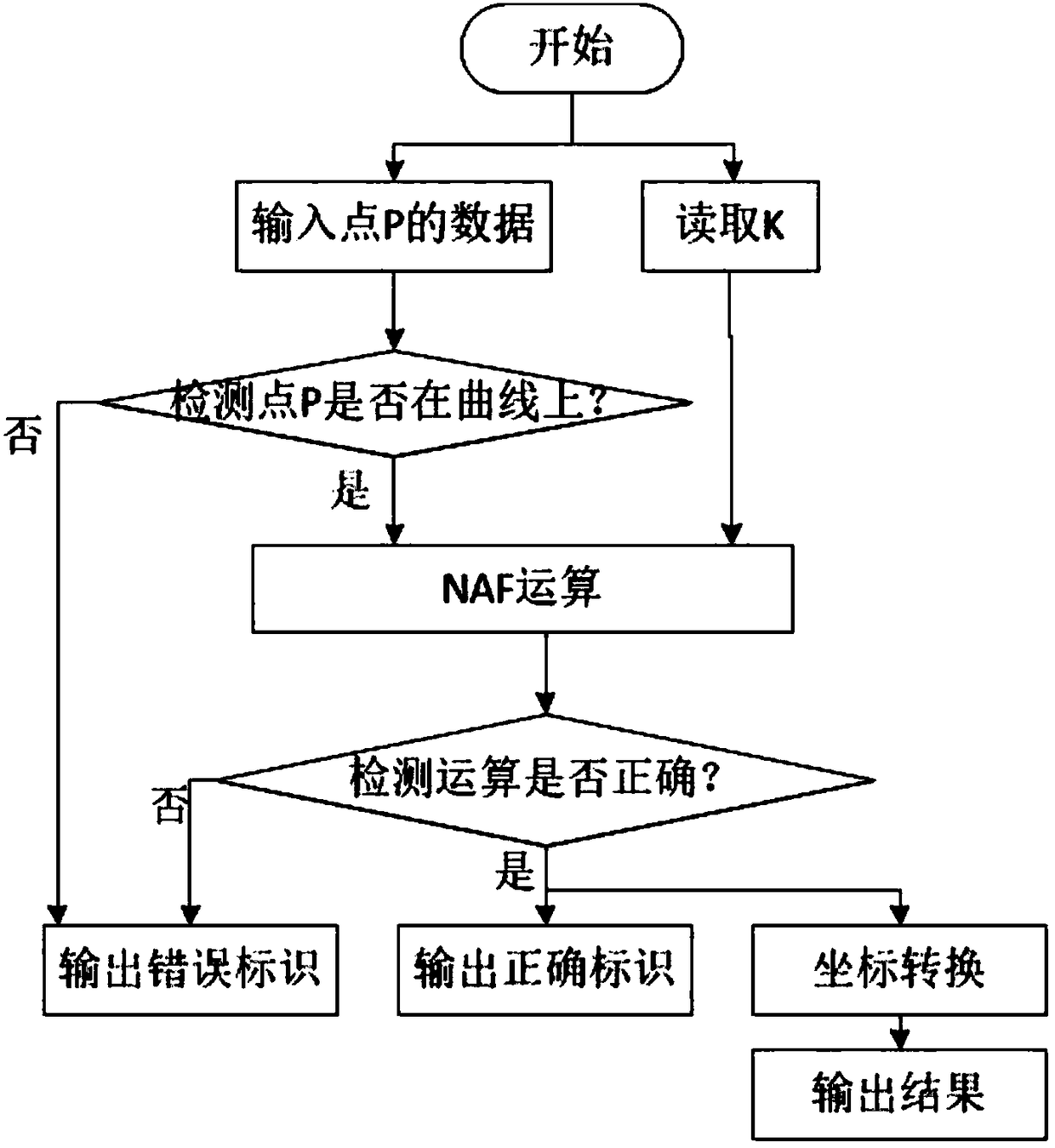
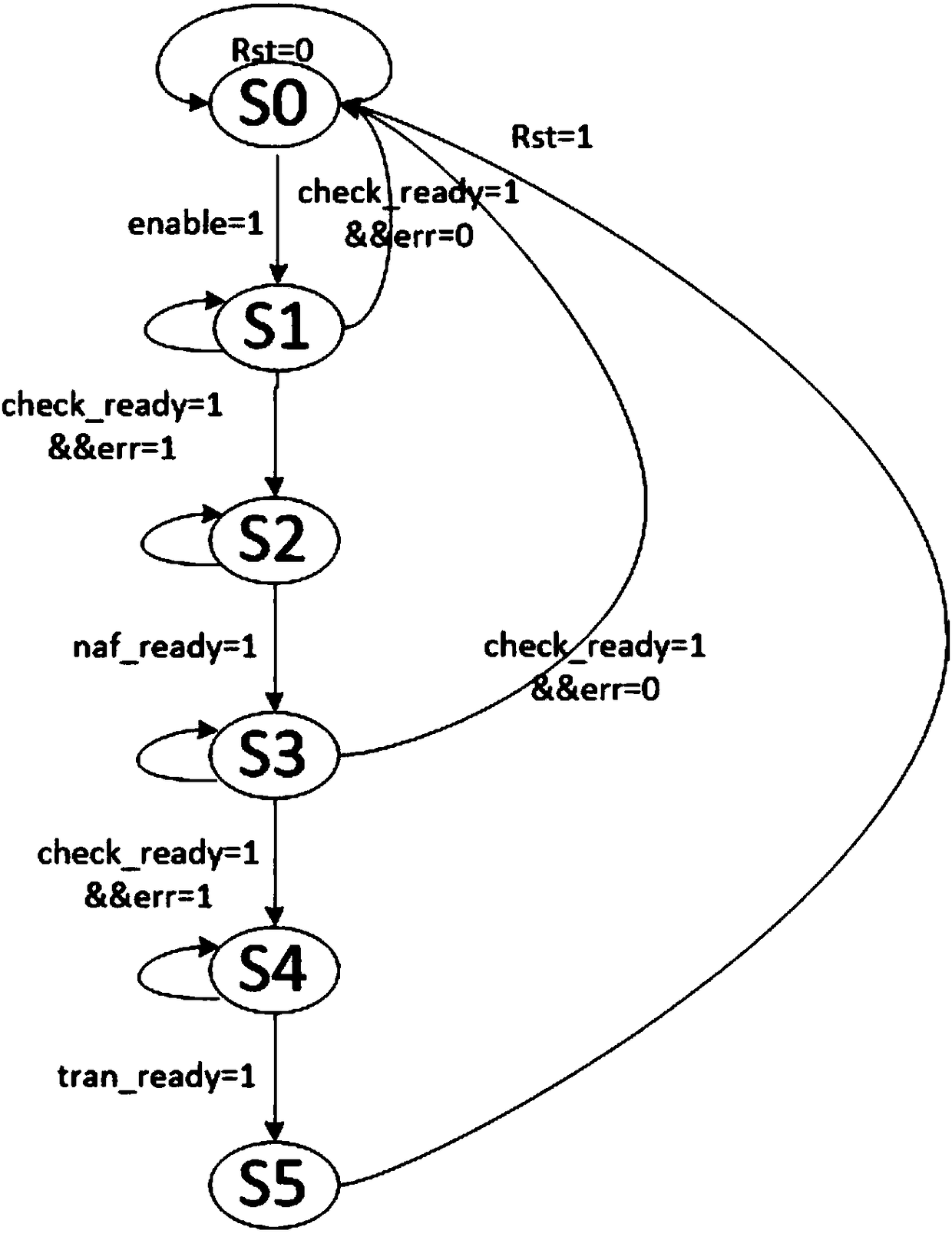
[0056] The embodiment of the present invention takes the comprehensive anti-side channel attack of the SM2 algorithm as the starting point, and adopts a set of defense against simple power analysis (Simple Power Analysis, SPA), differential power analysis (Differential Power Analysis, DPA), fault analysis attack (Fault Analysis Attack, FAA) including a series of measures, and algorithm optimization and circuit design for point product calculation fr...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More