A method and system for SSH secret key management
A secret key and management center technology, applied in transmission systems, digital transmission systems, and key distribution, can solve problems such as inability to effectively replace secret keys in a timely manner, and inability to effectively prevent "man-in-the-middle" attacks, and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] In order to make the object, technical solution and advantages of the present invention clearer, the embodiments of the present invention will be further described in detail below in conjunction with specific embodiments and with reference to the accompanying drawings.
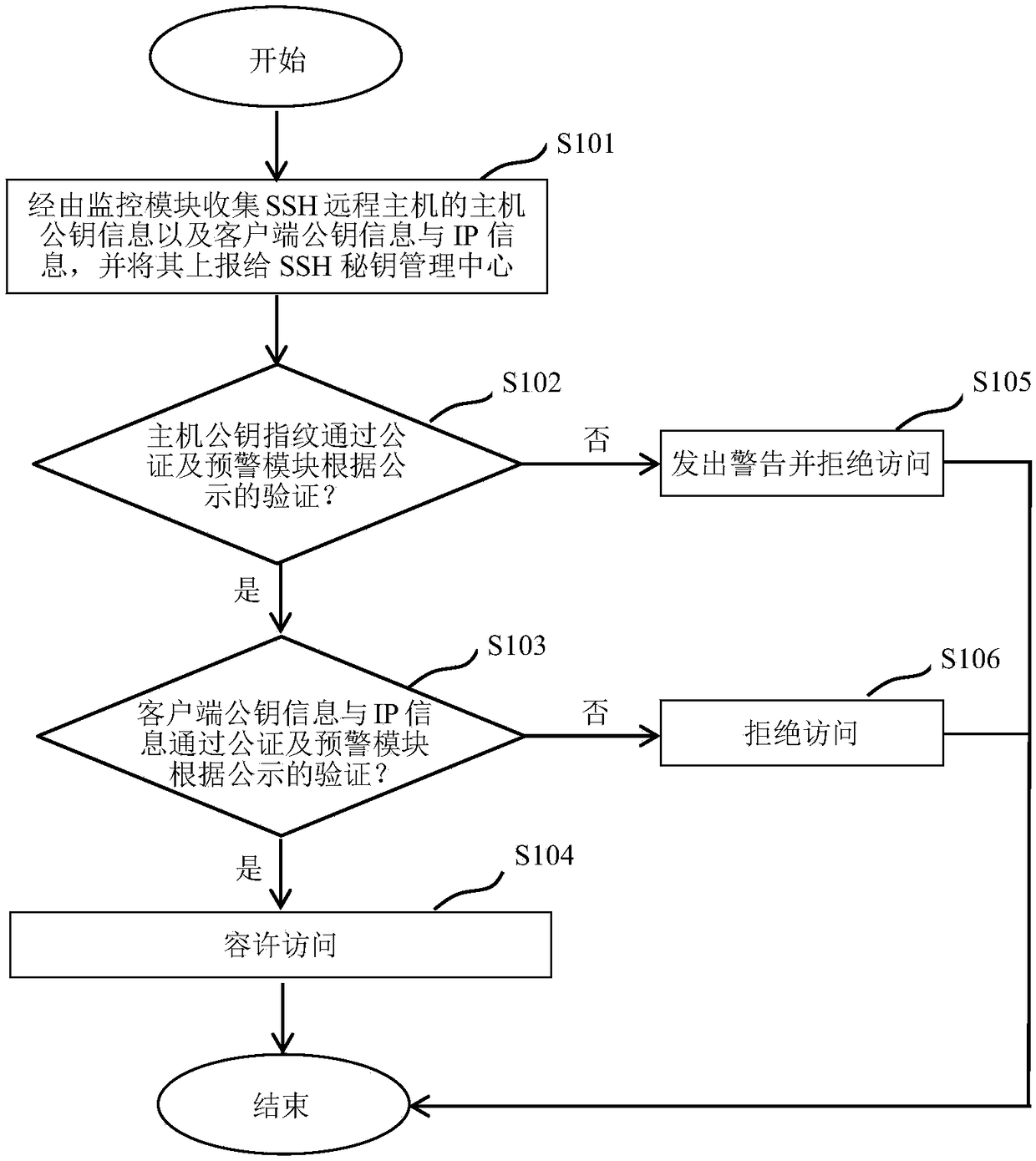
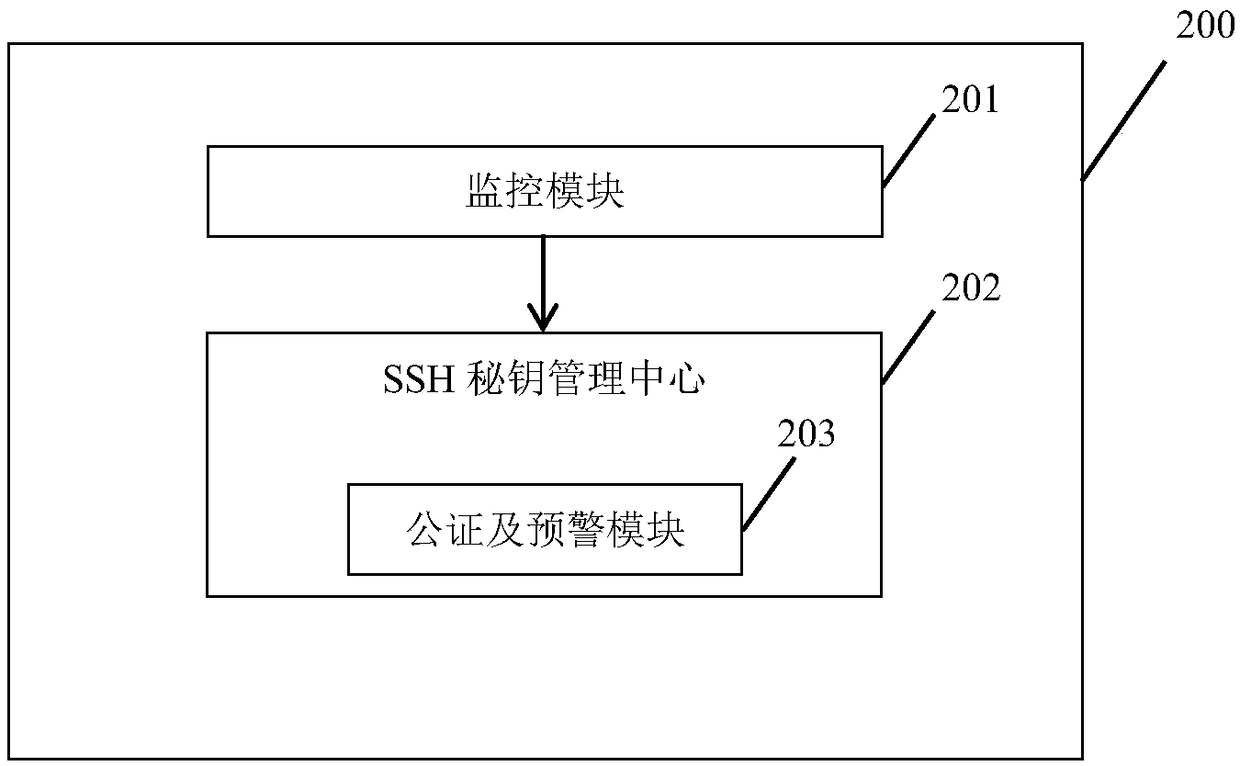
[0028] Based on the above purpose, the first aspect of the embodiments of the present invention proposes an embodiment of a method for managing SSH keys. figure 1 Shown is a schematic flow chart of the method.
[0029] Such as figure 1 As shown in , the method generally includes the following steps:
[0030] First, in step S101, the host public key information of the SSH remote host and the client public key information and IP information uploaded to the SSH remote host are collected via the monitoring module of the SSH remote host, and reported to the SSH key management center for further processing. Publicity, and then proceed to step S102.
[0031] In step S102, the notarization and early warning ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More