Authorization method, apparatus, apparatus and medium for digital assets
A technology of digital assets and permissions, applied in electrical components, transmission systems, program/content distribution protection, etc., can solve the problem of difficulty in ensuring the reliability and correctness of digital assets, and reduce the difficulty of copyright protection, ensure reliability and correctness. sexual effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
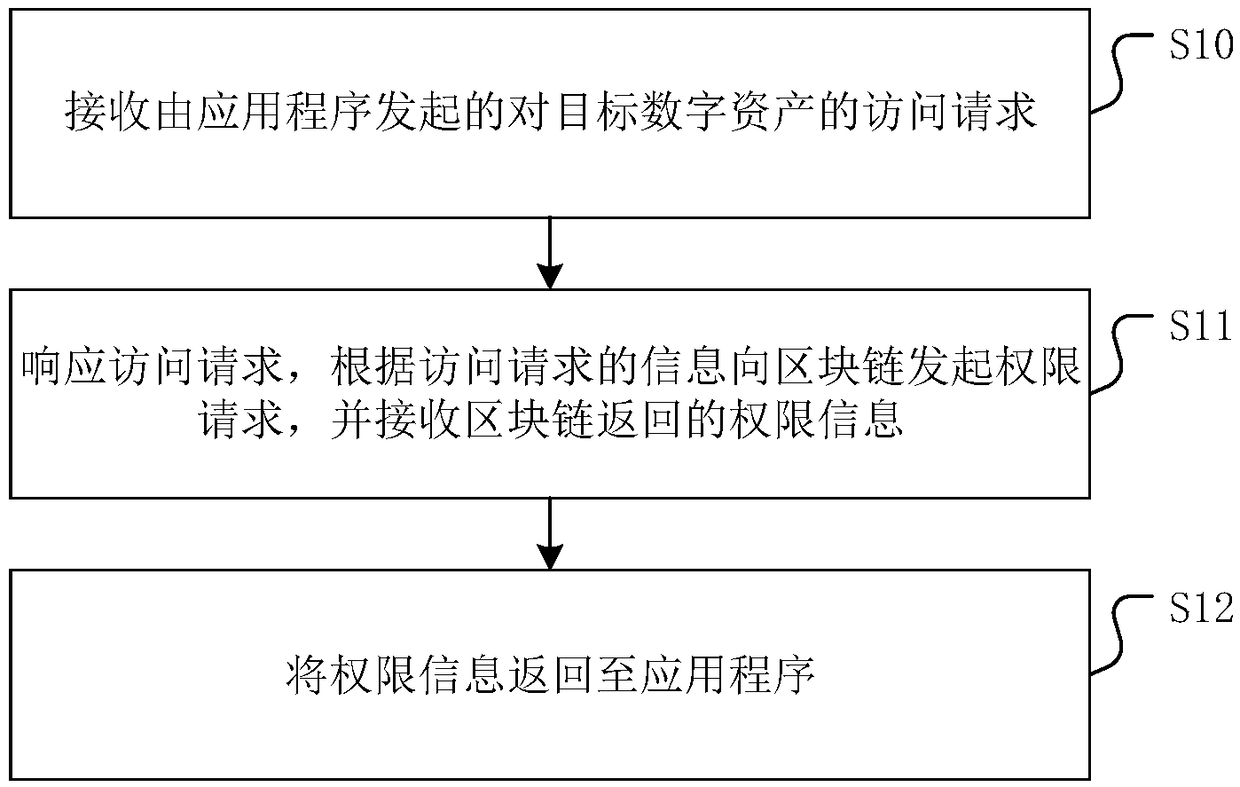
[0039] figure 1 It is a flowchart of a digital asset authorization method provided by an embodiment of the present invention. Please refer to figure 1 , the specific steps of the digital asset authorization method include:
[0040] Step S10: Receive an access request initiated by an application program to a target digital asset.
[0041] Among them, the application is pre-logged in as a user.
[0042] It should be noted that since there are generally no differences in the applications themselves provided by enterprises to users, the applications themselves only provide users with a way to obtain digital assets, and the difference is often the user identity used to log in to the application. Different users There are differences in the digital asset usage permissions of identities. For example, in the current video-type application, users can access specific video content through payment methods, that is, the user identity of paid users has the right to obtain specific vide...
Embodiment 2
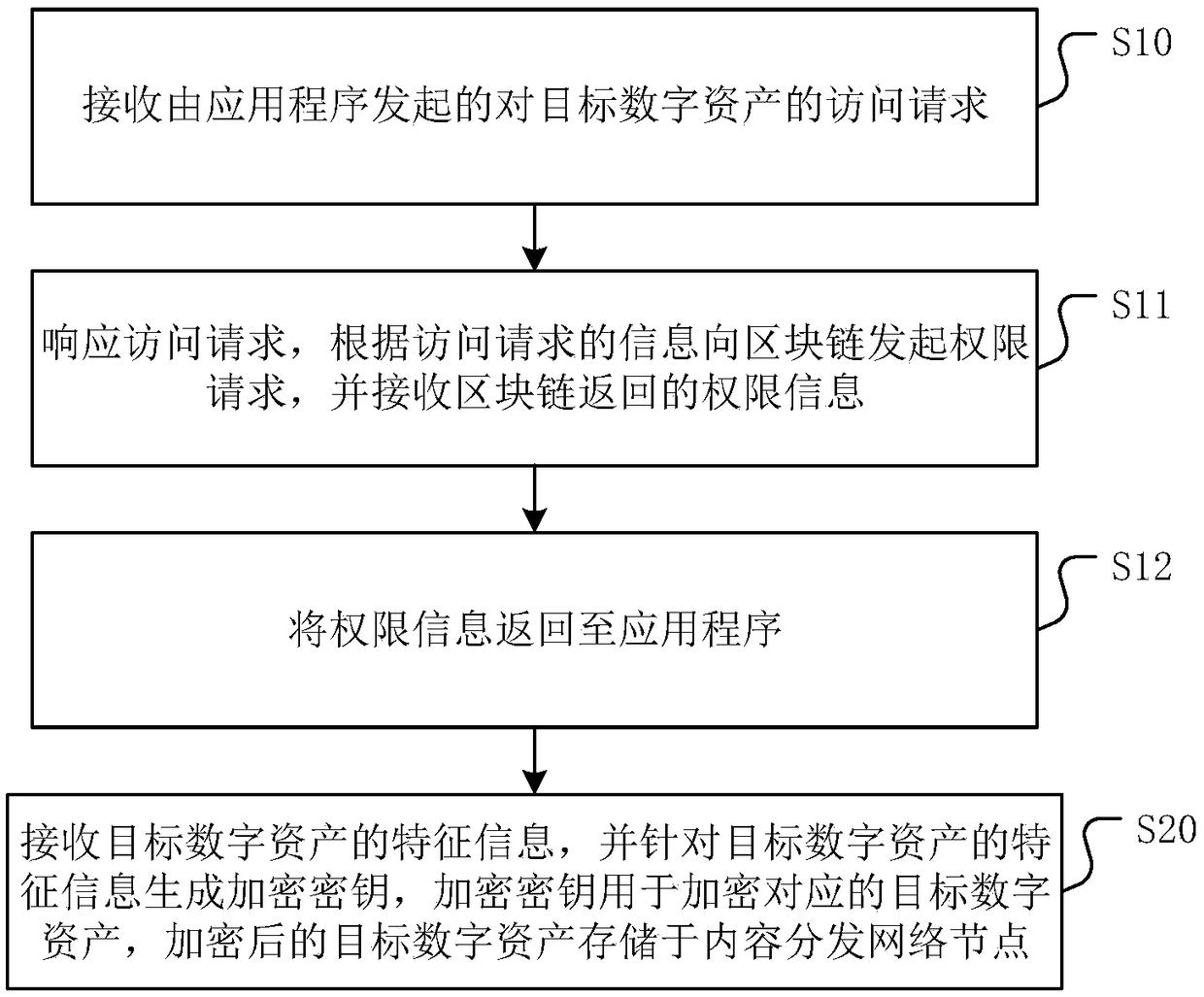
[0050] On the basis of the above embodiments, the present invention also provides the following series of preferred implementation manners.
[0051] As a preferred implementation manner, the access request includes at least characteristic information of the target digital asset and identity information of the user identity.
[0052] It should be noted that the feature information is generated by feature extraction of digital asset data, and the feature information corresponding to different available digital assets is not the same. Since the data volume of characteristic information is often much smaller than the data volume of the digital asset itself, it can be more efficient to transmit as a request. Each characteristic information is generated by feature extraction of the corresponding digital asset, and there will be no duplication among the characteristic information, so the characteristic information can be used as CID (Content ID) in this embodiment to uniquely represe...
Embodiment 3
[0083] The embodiment of the digital asset authorization method has been described in detail above, and the present invention also provides a digital asset authorization device corresponding to the method. Since the embodiment of the device part corresponds to the embodiment of the method part, Therefore, for the embodiment of the device part, please refer to the description of the embodiment of the method part, and details will not be repeated here.
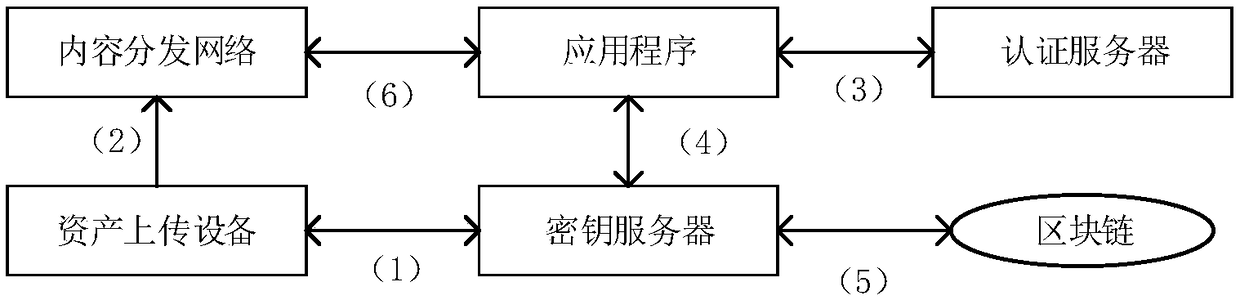
[0084] Figure 4 A structural diagram of a device for authorizing digital assets provided by an embodiment of the present invention. The digital asset authorization device provided by the embodiment of the present invention includes:
[0085] The request obtaining module 10 is configured to receive an access request to a target digital asset initiated by an application program, wherein the application program logs in as a user in advance.
[0086] The request response module 11 is used to respond to the access request, initiat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com