A Compressed Audio Adaptive Steganography Method and System Based on Equal Length Entropy Codeword Replacement
A self-adaptive, codeword technology, applied in the field of information hiding, can solve the problems of low capacity and poor security, achieve the effect of high embedding rate, high security, and improve anti-steganalysis ability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The compressed audio adaptive steganography method based on equal-length entropy codeword replacement of the present invention includes information embedding and information extraction, and the specific implementation is described in detail as follows.
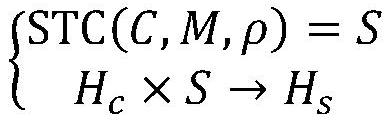
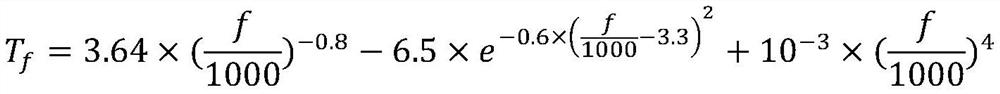
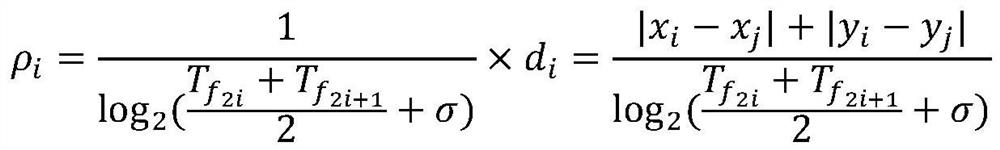
[0035] figure 1 It is the realization flow chart of the information steganography method of the present invention, figure 2 It is the module composition and working flow chart of the steganography system corresponding to the method. It can be mainly divided into six modules: codeword-binary mapping module, distortion function module, scrambling module, STC encoding module, inverse scrambling module and binary-codeword mapping module. First, the original Huffman code stream H c After the codeword-binary mapping module, it will be converted into a carrier bit string C. Second, the distortion function module calculates the modification cost ρ of each embeddable position according to the psychoacoustic model and the coe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More