Method, device and server for processing identity secret key
A technology of a processing device and a processing method, which is applied in the computer field, can solve problems such as the inability to guarantee the security of the identity key and the complexity of the system, and achieve the effect of ensuring security and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
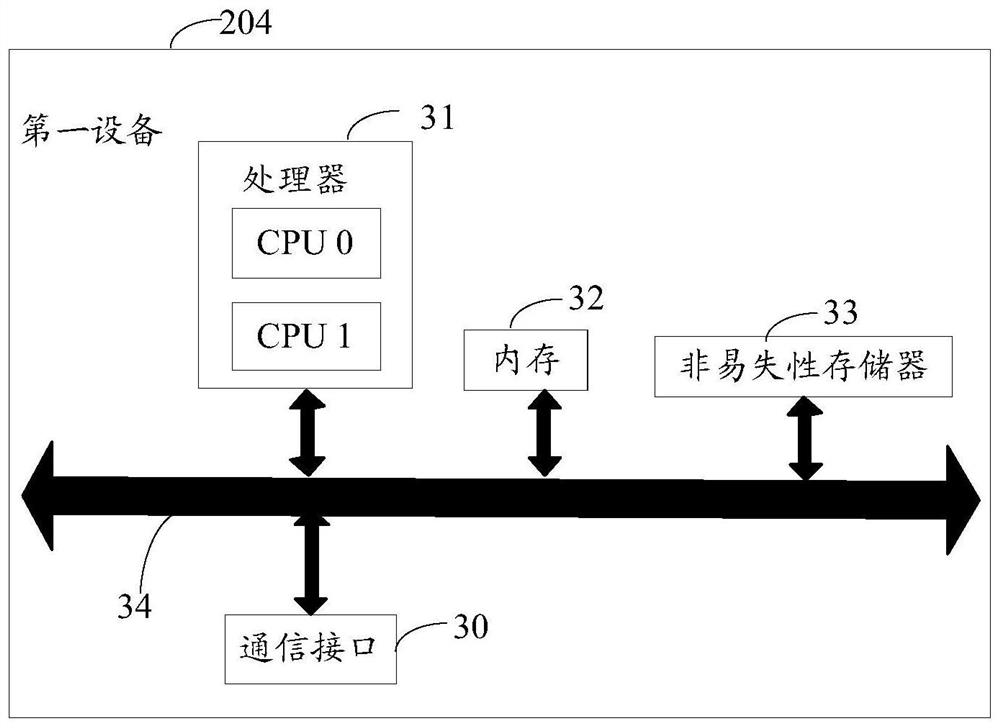
[0030] The following describes in detail the processing method of the identity key provided by the embodiment of the present application with reference to the accompanying drawings.
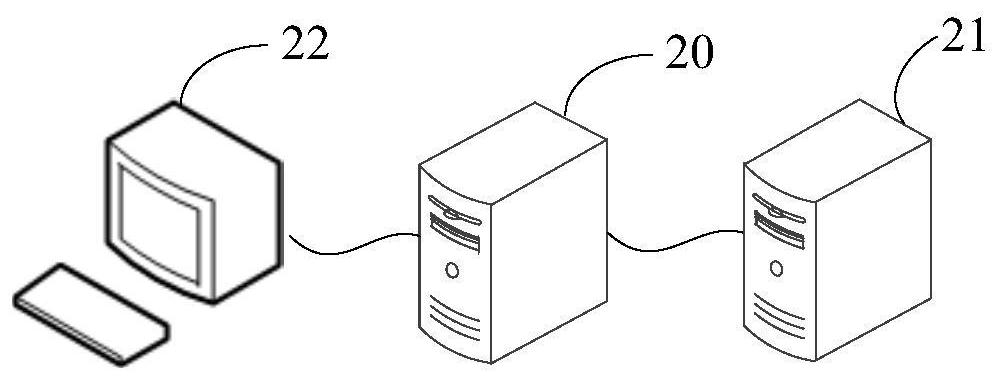
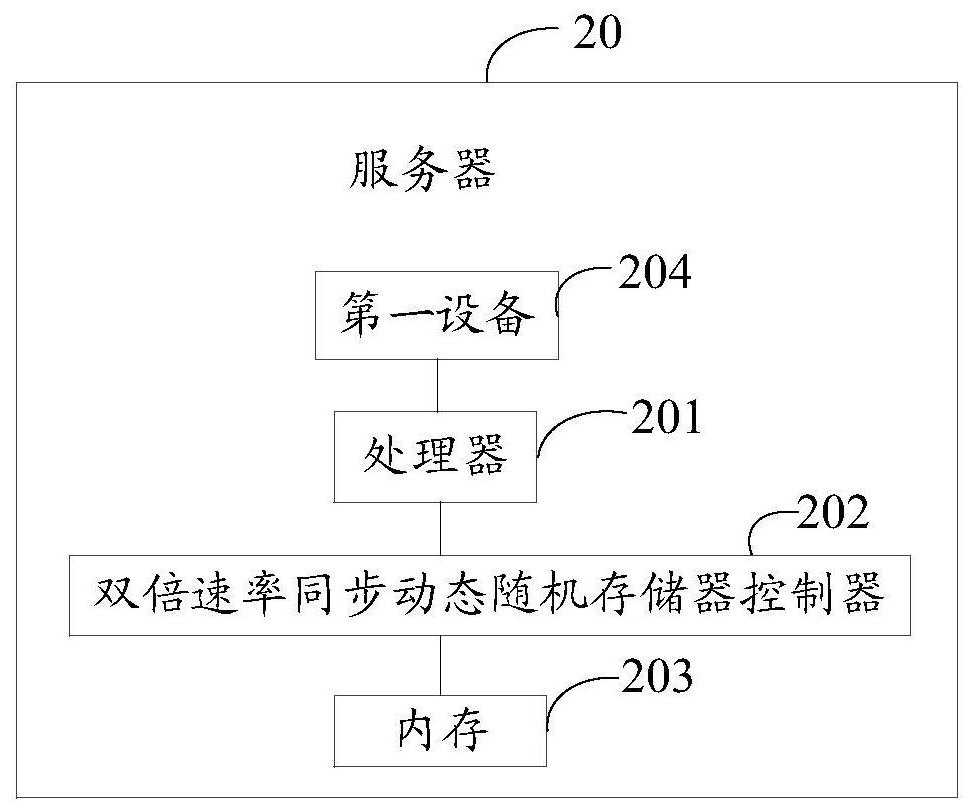
[0031] figure 1 It is a schematic structural diagram of a communication system to which the identity key processing method provided in the embodiment of the present application is applicable. As shown in the figure, the communication system includes a server 20 , an identity management server 21 and a terminal 22 . Wherein, the combination of the server 20 and the identity management server 21 may also be called a cloud platform. The user remotely logs into the cloud platform through the terminal 22, and after the user's identity is authenticated, the function of the virtual machine on the server 20 can be used.
[0032]The terminal 22 may be a computer, such as a desktop computer, a notebook computer, a tablet computer, etc., or may only include a user interaction and operation interface (such...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More