Stand-alone software verification method
A software verification, stand-alone technology, applied in computer security devices, program/content distribution protection, instruments, etc., can solve the problems of multiple registrations, cannot guarantee unique installation, affect the interests of developers, etc., to achieve the effect of protecting interests
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0014] The present invention will be further described in detail below in conjunction with the drawings and specific embodiments.
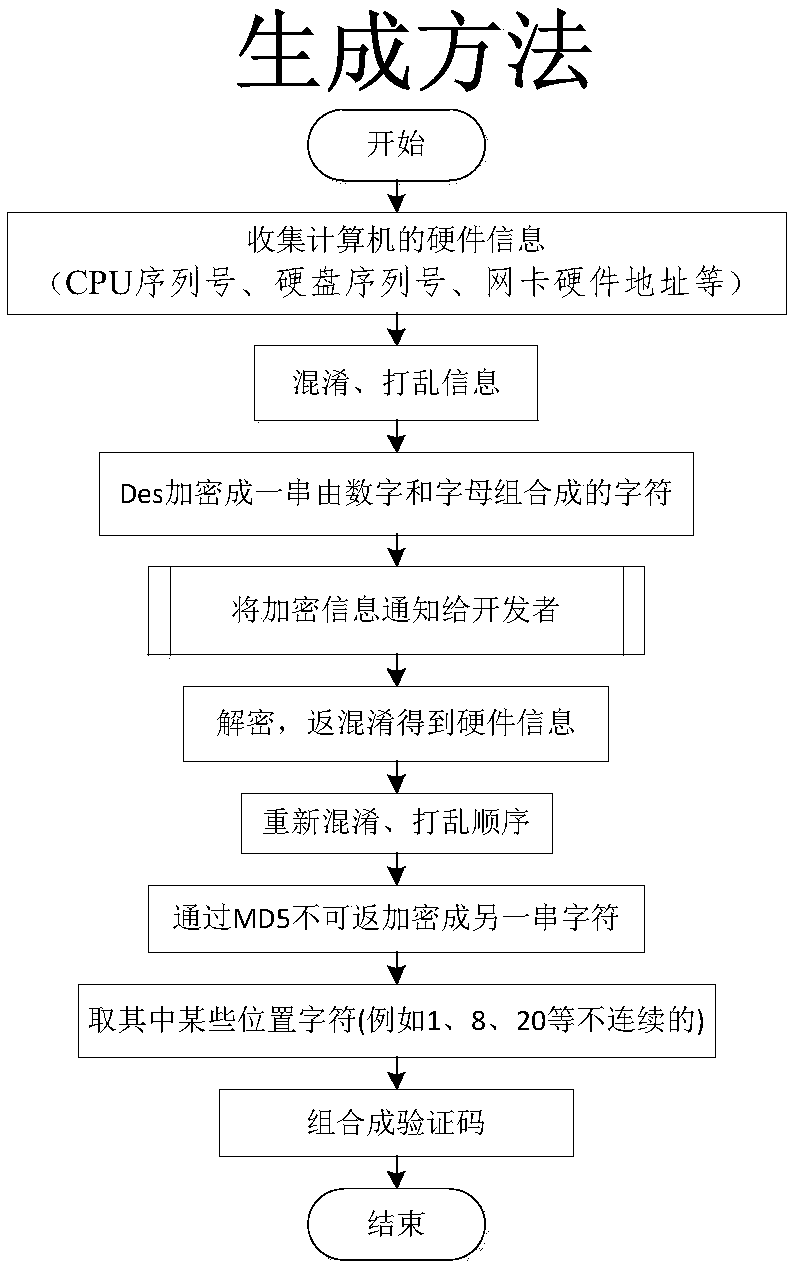
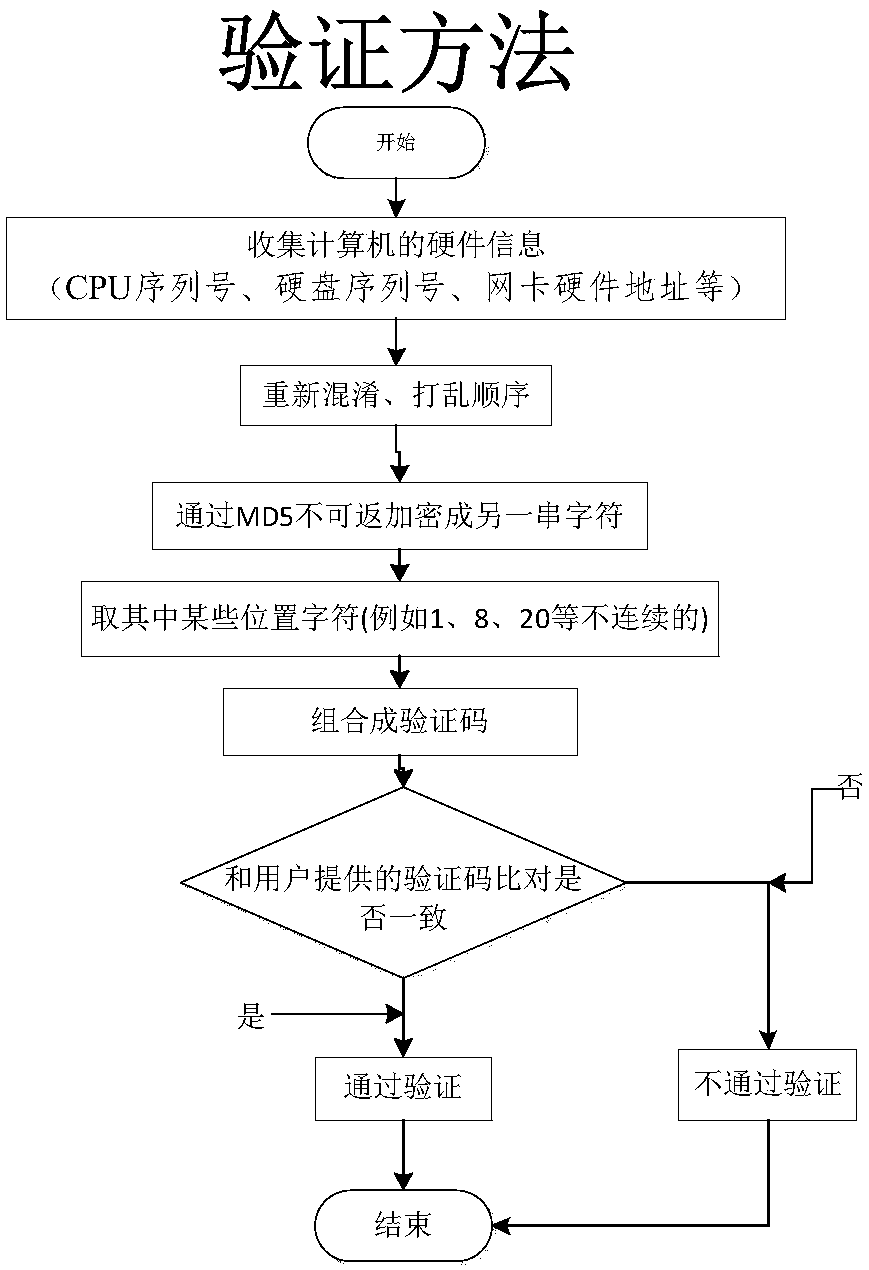
[0015] Such as figure 1 , figure 2 Shown are the verification code generation method and verification method of the stand-alone software verification method of the embodiment of the present invention.
[0016] First of all, the generation method, as the name suggests, is a method of generating a serial number based on hardware information. The collected hardware information can be easily obtained through the existing technology. The order of obfuscation depends on the person using this method, which is equivalent to a first-level password. The DES encryption method will add a password again, which is equivalent to secondary encryption. The final MD5 encryption method is currently a very reliable encryption method, which is equivalent to three-level encryption. Therefore, the generated serial number is almost impossible to be cracked without knowin...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More