High-security IP secure communication method based on true random stream XOR encryption
A secret communication, true random technology, applied in key distribution, can solve the problems of network equipment security loopholes, implanted monitoring Trojans, easy access to IP subnets, etc. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0014] The present invention relates to the following special terms:
[0015] Encrypted state masking data block: After the entire plaintext IP message (including the IP header) is encrypted, a data block with the same length as the plaintext IP message is formed.
[0016] True randomized data block: A data block formed after performing an XOR encryption operation with a quantum true random number.
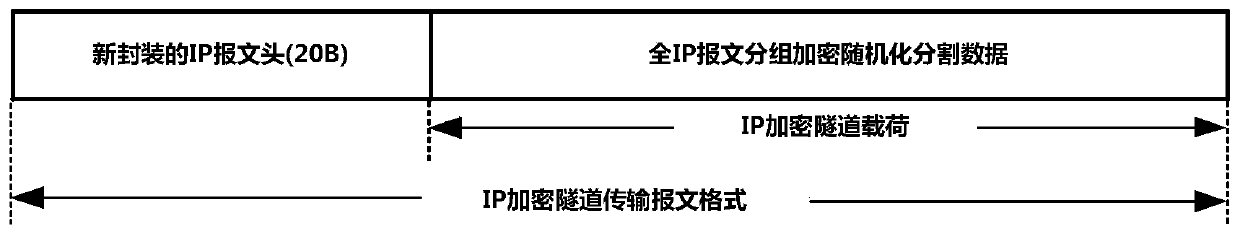
[0017] Ciphertext payload data: the data formed by dividing the true randomized data block into parity bytes, and encapsulating the standard IP protocol header to form an IP encrypted message.
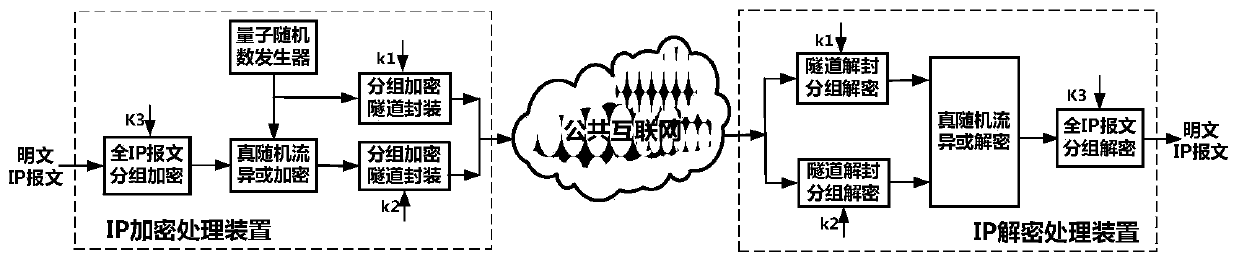
[0018] The present invention proposes a high-safety secret communication method that jointly adopts a triple protection mechanism of group encryption with hidden IP message data format, true random stream XOR encryption and link transmission group encryption. This highly secure IP confidential communication method is based on true random stream XOR encryption technology, and uses all-IP f...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More