Intrusion response strategy generation method and device
A strategy and meta-policy technology, applied in the field of information security, can solve problems such as the inability to effectively guarantee response utility, and achieve the effect of ensuring accuracy and high response utility.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
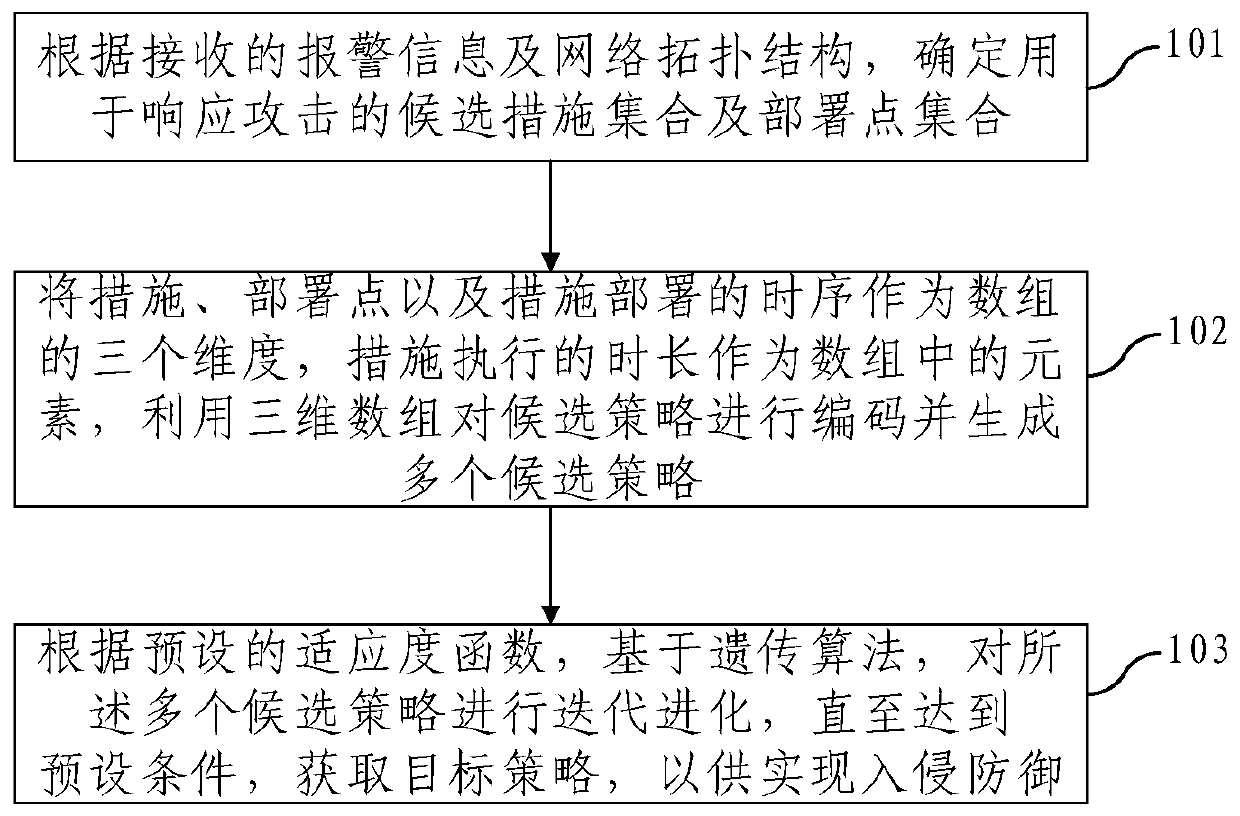
[0017] In order to make the objectives, technical solutions, and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be described clearly and completely in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments It is a part of the embodiments of the present invention, not all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative work shall fall within the protection scope of the present invention.
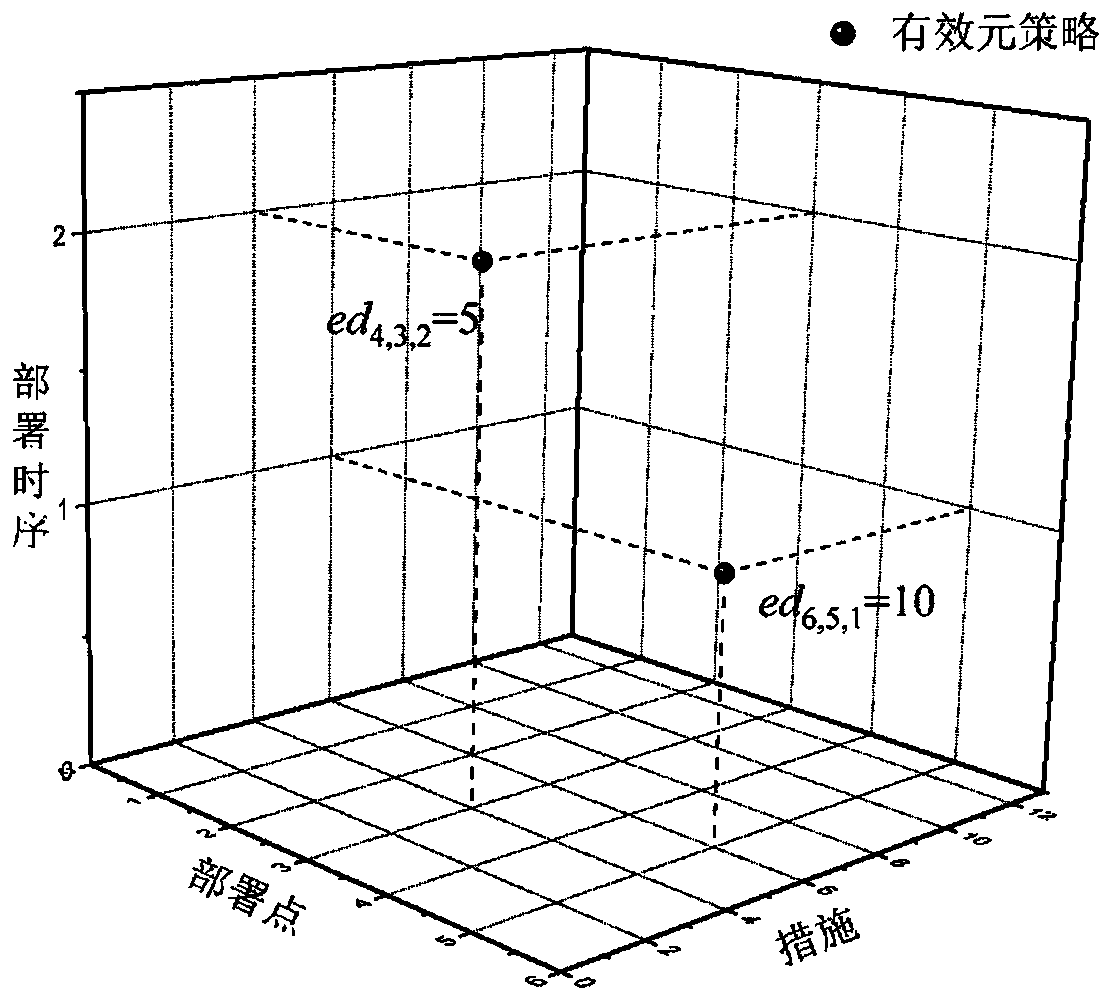
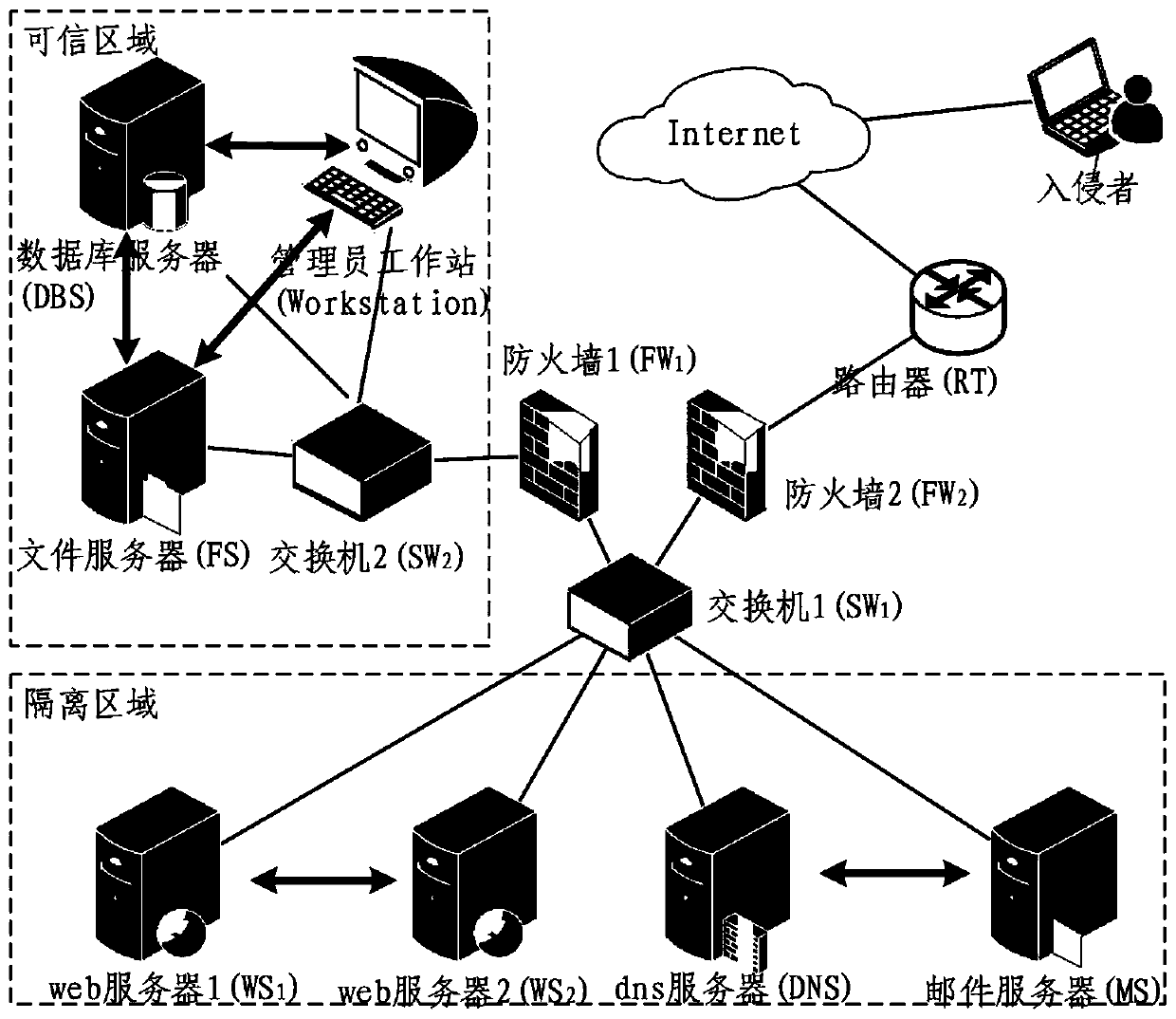
[0018] The existing response strategy generation scheme mainly solves the two problems of the selection of measures in the intrusion response and the selection of the deployment points of measures. However, in practice, in order to resist the attack as accurately as possible, the generated response strategy also needs to solve the fol...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More