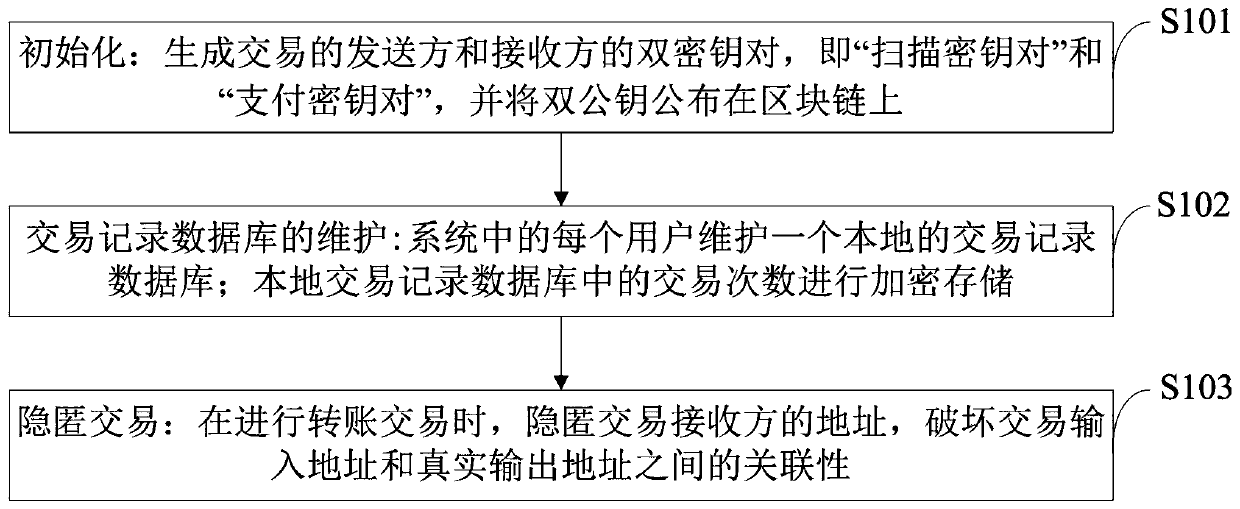
Method for implementing blockchain dual-key hidden address protocol without temporary key leakage
A technology of temporary keys and implementation methods, which is applied in the direction of instruments, payment systems, data processing applications, etc., can solve the problems of user privacy security threats, loss of private information, unrecognizable hidden transactions and hidden transactions, etc., to solve privacy security issues Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0063] In order to make the object, technical solution and advantages of the present invention more clear, the present invention will be further described in detail below in conjunction with the examples. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0064] Aiming at the problems existing in the prior art, the present invention provides a method for implementing a blockchain dual-key hidden address protocol without temporary key leakage. The present invention will be described in detail below in conjunction with the accompanying drawings.
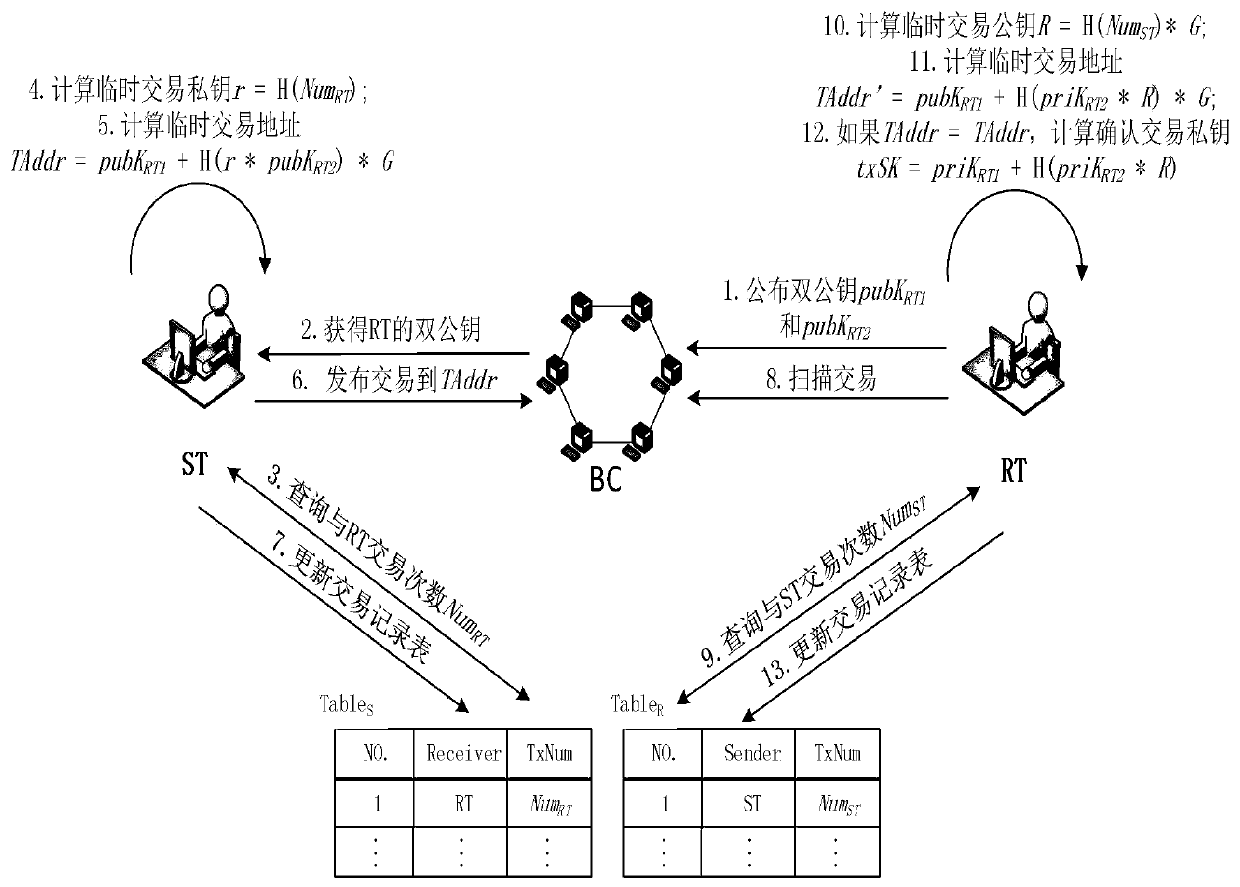
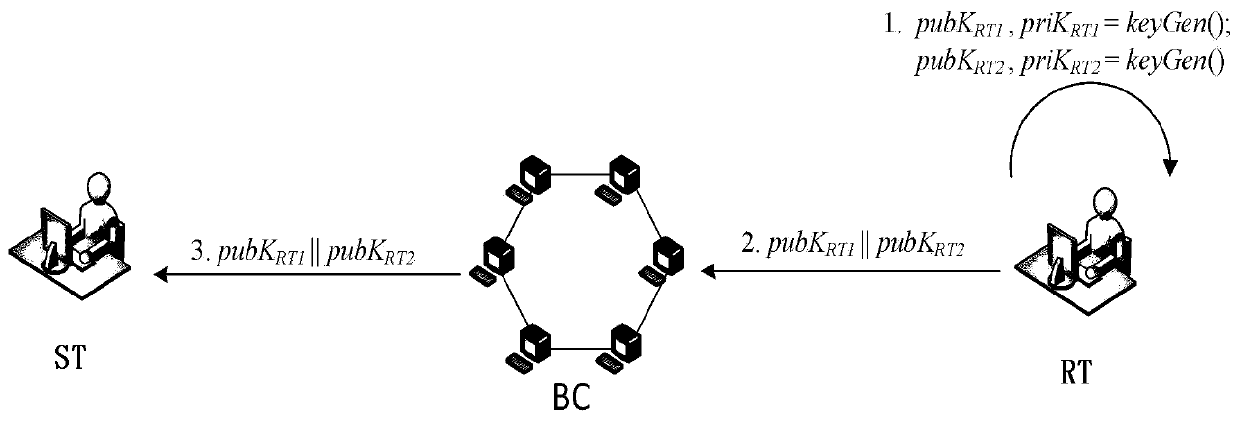
[0065] The present invention is achieved in this way, the system architecture diagram of PDKSAP is as follows figure 2 As shown, the entities involved are the sender, receiver and blockchain of the transaction, where ST means the sender of the transaction, RT means the receiver of the transaction, and BC means the blockchain.
[00...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More