System login protection method and device based on TPM chip
A chip and device technology, applied in the field of system login protection based on TPM chips, can solve the problems of hidden dangers in HMAC message authentication, and achieve the effects of increasing competitiveness, preventing dictionary attacks, and high security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] In order to make the object, technical solution and advantages of the present invention clearer, the embodiments of the present invention will be further described in detail below in conjunction with specific embodiments and with reference to the accompanying drawings.
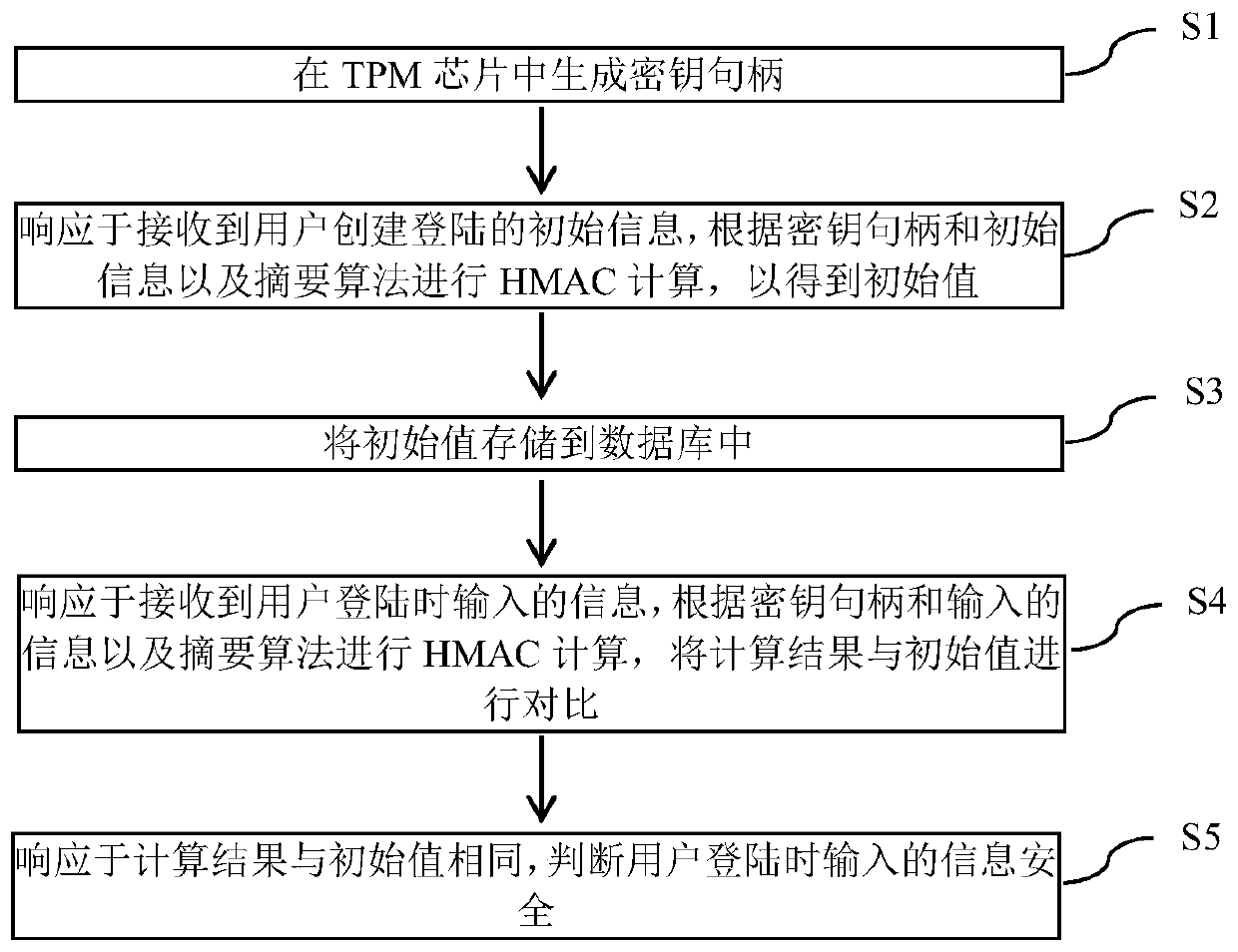
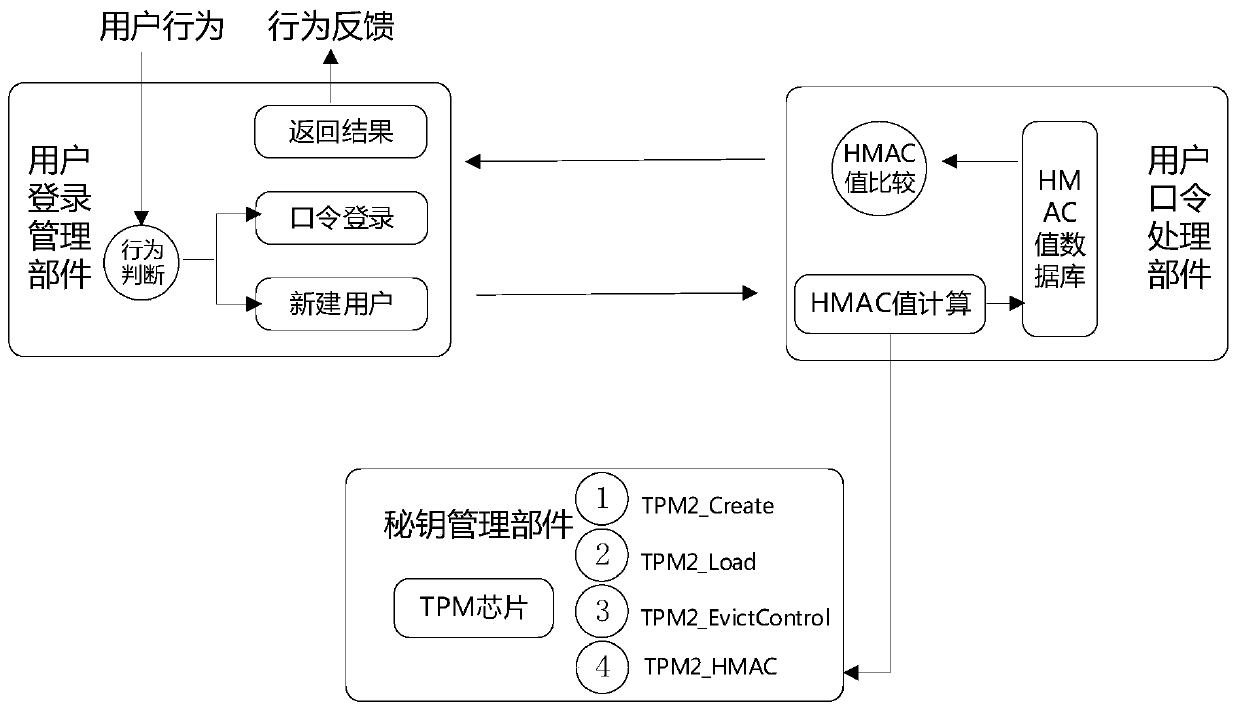
[0038] Based on the above purpose, the first aspect of the embodiments of the present invention proposes an embodiment of a system login protection method based on a TPM chip. figure 1 Shown is a schematic flow chart of the method.
[0039] Such as figure 1 As shown in , the method may include the following steps:
[0040] S1 generates a key handle in the TPM chip, which only exists inside the TPM chip hardware, ensuring the security of the key;
[0041] S2, in response to receiving the initial information for creating and logging in by the user, performs HMAC calculation according to the key handle, the initial information, and the digest algorithm to obtain the initial value;
[0042] S3 stores the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More