GF-2 image integrity authentication method using SIFT and SVD perceptual hash
A perceptual hashing, GF-2 technology, applied in the fields of cartography and geographic information systems, to achieve good robustness, effective extraction, and good robustness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
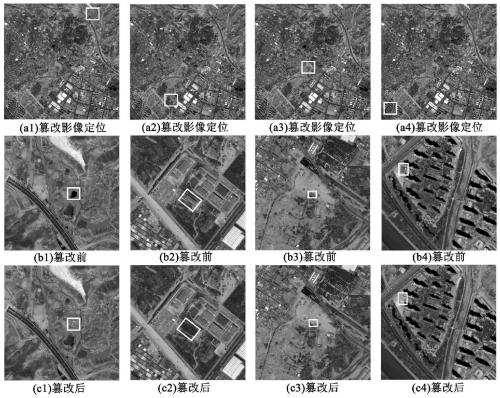
[0026] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
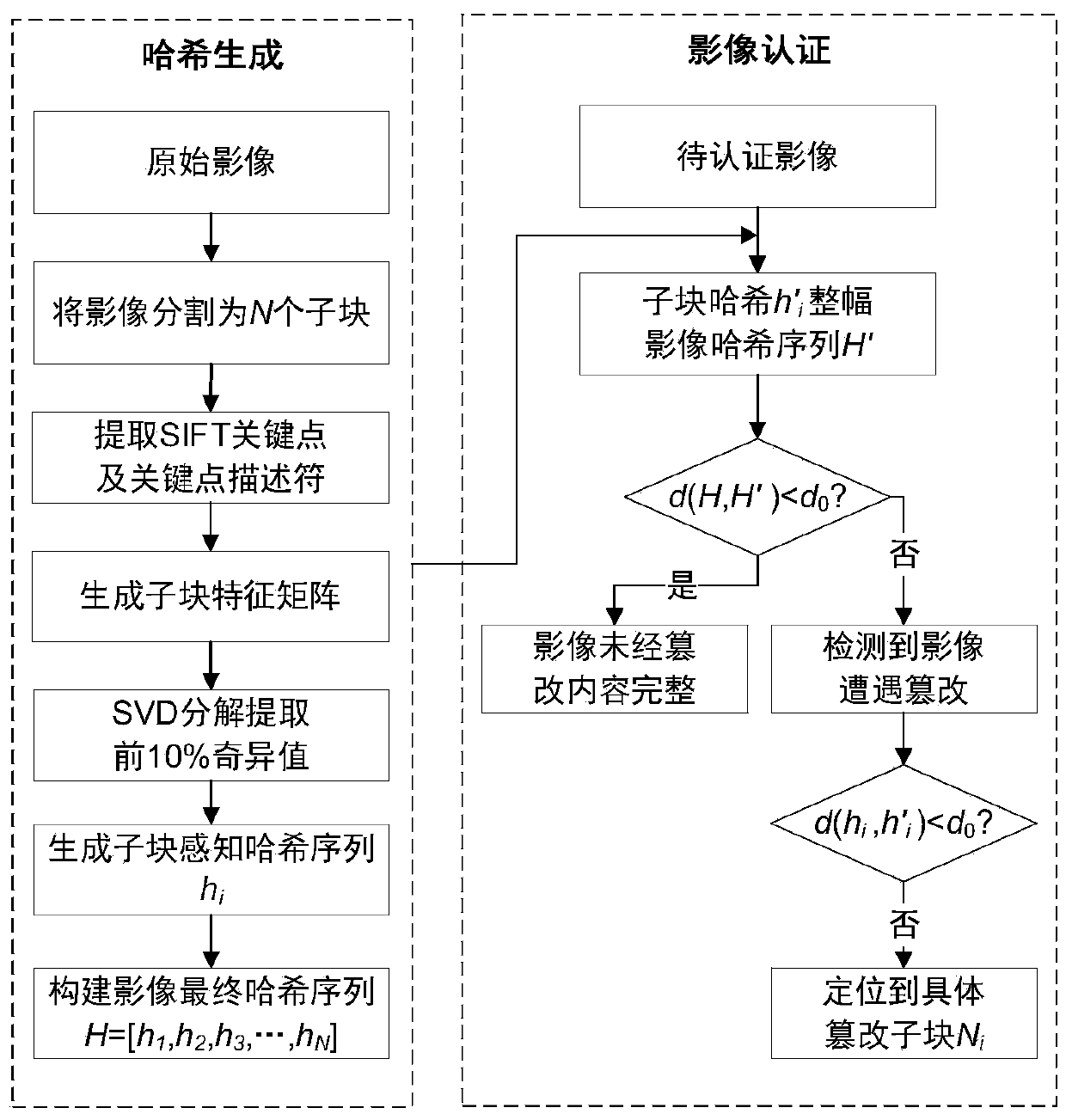
[0027] See attached figure 1 , the embodiment of the present invention discloses a GF-2 image integrity authentication method using SIFT and SVD perceptual hashing, including:
[0028] 1. Generation of image hash sequence
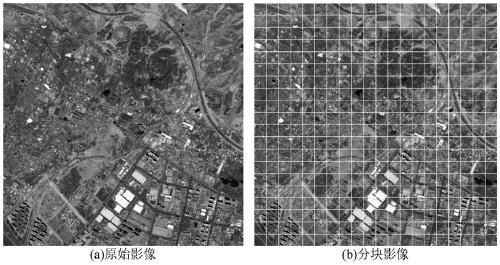
[0029] Step 1. Divide the original image into N fixed-size sub-blocks by using fixed block method.
[0030] Among them, the size of N is determined by factors such as specific image size, feature extraction efficiency, and robustness. In...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More