Key management method and system
A key management and data key technology, applied in the field of information security, can solve problems such as hidden dangers of information security, and achieve the effect of reducing the risk of leakage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0060] The technical solutions in the embodiments of the present application are clearly and completely described below in combination with the drawings in the embodiments of the present application. Obviously, the described embodiments are part of the embodiments of the present application, not all of them. Based on the embodiments in this application, all other embodiments obtained by those skilled in the art without making creative efforts belong to the scope of protection of this application.
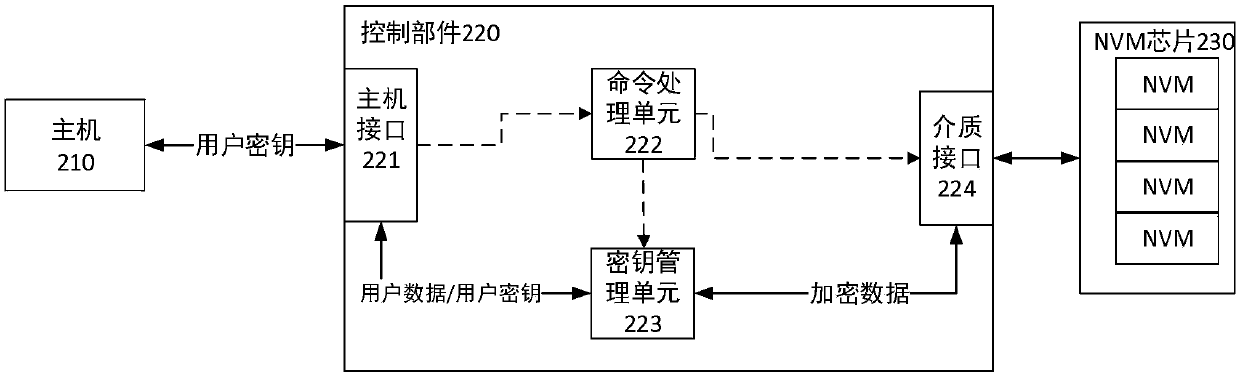
[0061] figure 2 is a schematic diagram of a key management system according to an embodiment of the present application.
[0062] According to the embodiment of the present application, the host 210 accesses the storage device through the host interface 221 . The control unit 220 includes a command processing unit 222 and a key management unit 223 . The command processing unit 222 acquires and processes commands provided by the host 210 . The commands provided by the host 210 in...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More