Botnet detection method and system and storage medium
A botnet and detection system technology, applied in the field of botnet detection methods, systems and storage media, can solve the problems of low botnet detection efficiency, huge data flow, large processing load, etc. Effects of low number of features
Active Publication Date: 2020-07-03
ZTE CORP
View PDF6 Cites 4 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
However, these methods require a variety of data information, huge data streams, and need to analyze data packets to extract multiple features, and the processing load is too large, resulting in low detection efficiency of botnets
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
no. 1 example
[0178] Such as Image 6 As shown, the second embodiment of the present invention proposes a botnet detection method, based on the above figure 2 In the first embodiment shown, the method further includes:
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
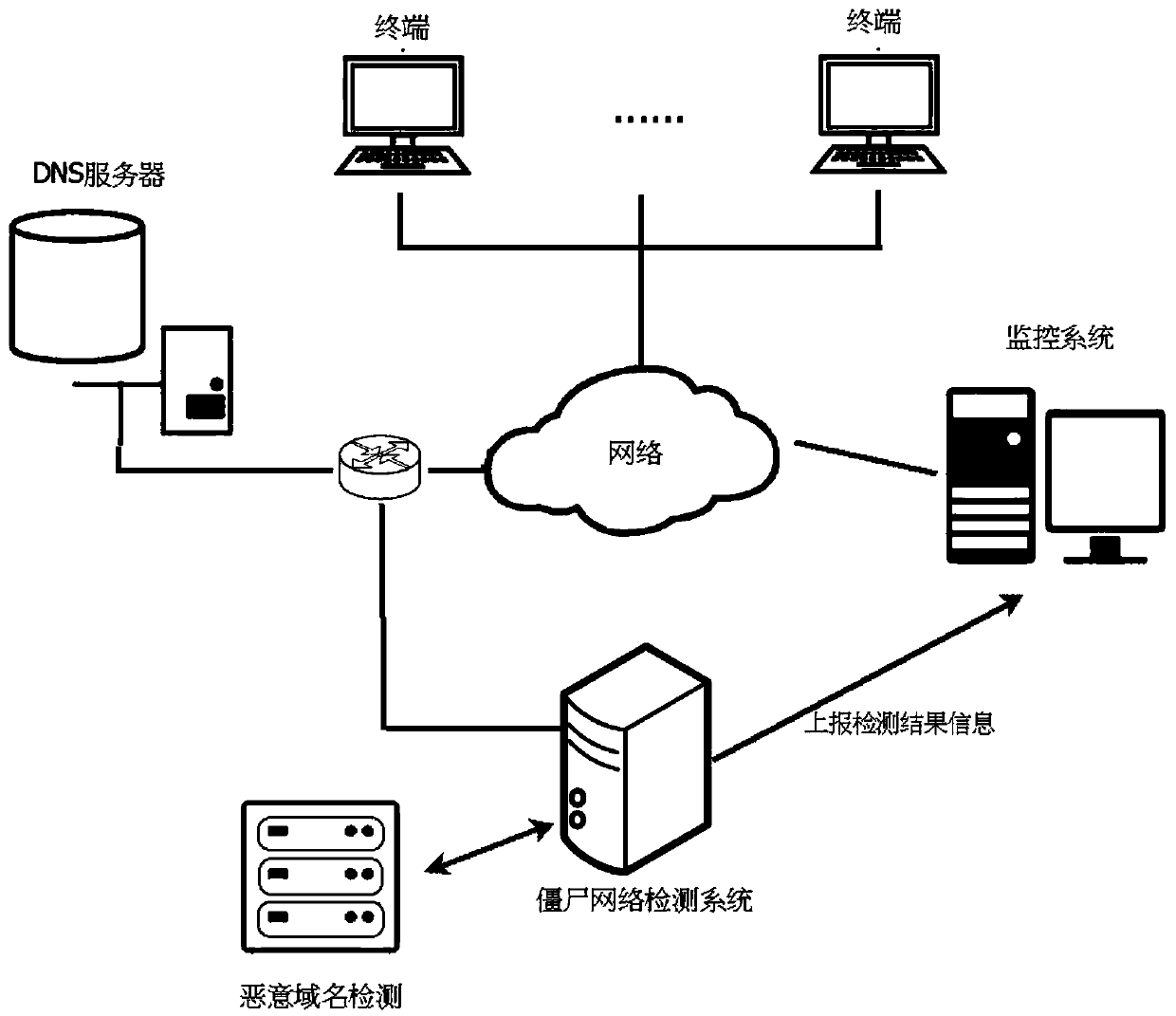
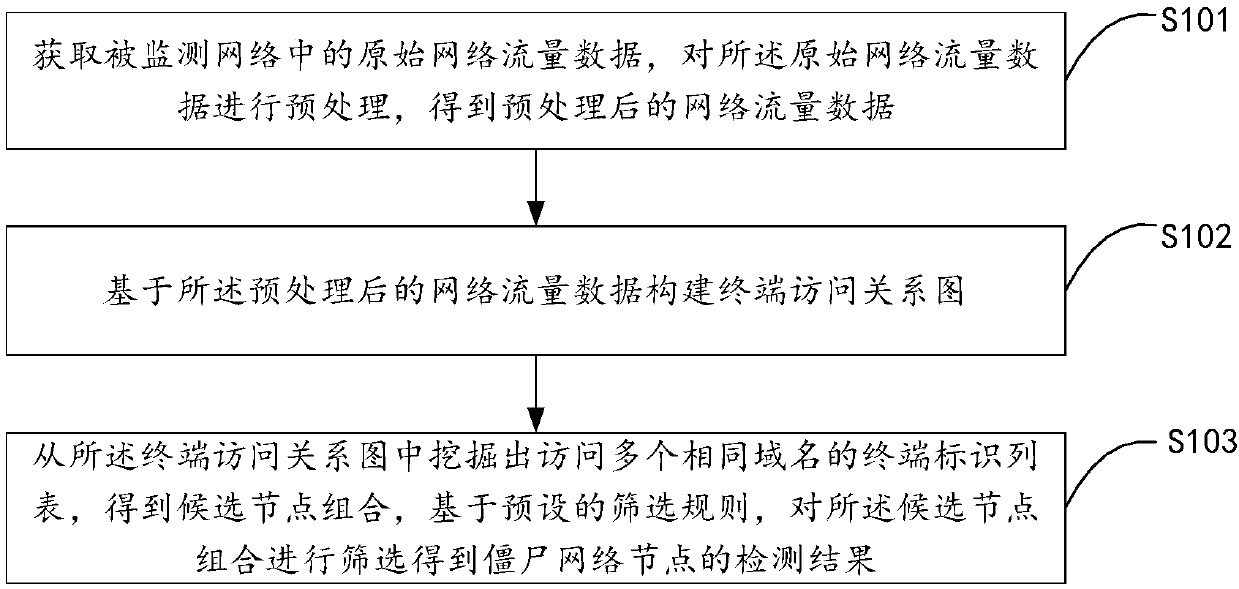
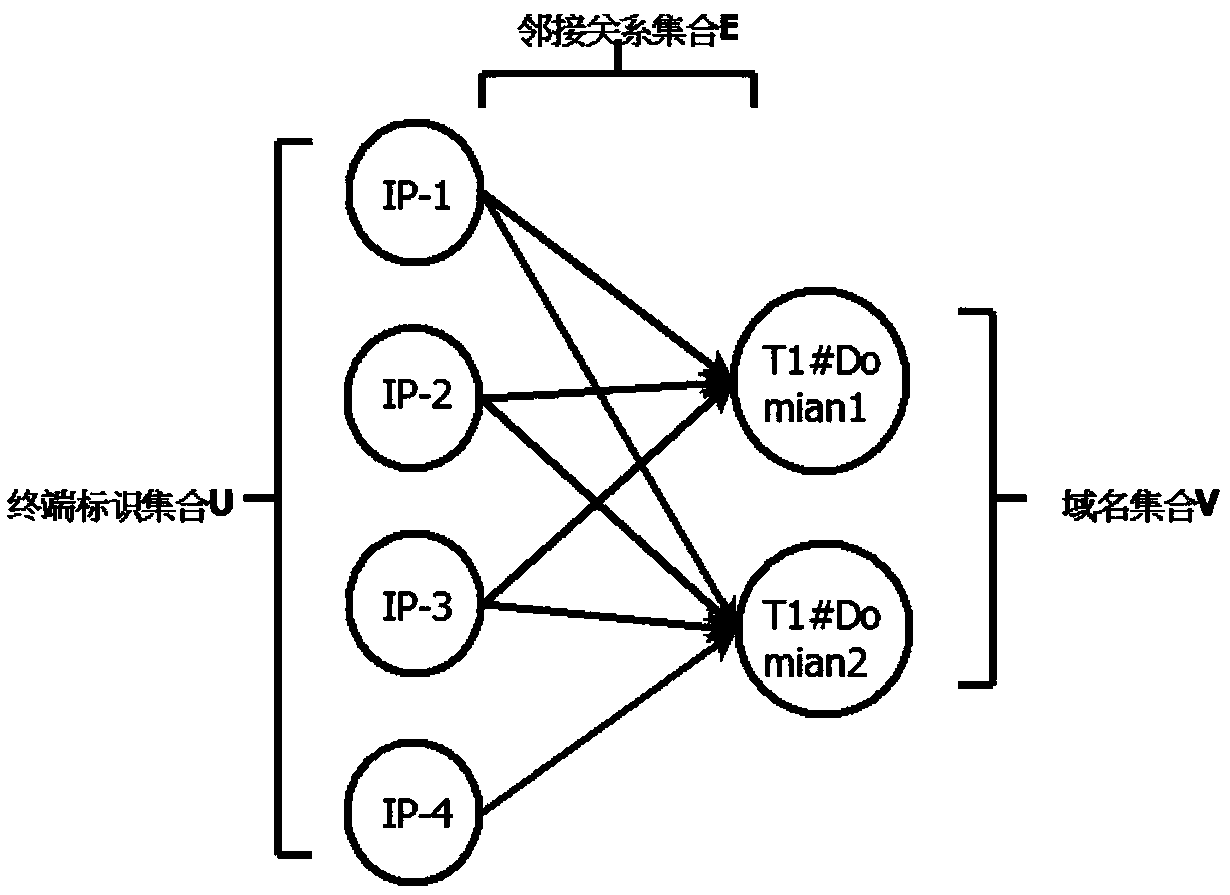
The invention discloses a botnet detection method and system and a storage medium, and the method comprises the steps: obtaining the original network flow data in a monitored network, carrying out thepreprocessing of the original network flow data, and obtaining the preprocessed network flow data; constructing a terminal access relation graph based on the preprocessed network traffic data; and mining a plurality of terminal identification lists accessing the same domain name from the terminal access relation graph to obtain a candidate node combination, and screening the candidate node combination based on a preset screening rule to obtain a botnet node detection result. According to the scheme, the types of the applied data are few, the number of the features extracted from the data flowis small, the calculation overhead is small, the detection efficiency can be effectively improved, detection does not need to be carried out based on the known botnet behavior features, and the scheme can be better applied to detection of unknown botnet threats.
Description
technical field [0001] The invention relates to the technical field of network security, in particular to a botnet detection method, system and storage medium. Background technique [0002] Botnet refers to the use of one or more means of transmission to make a large number of hosts infected with bot programs (BOT programs) virus, thus forming a one-to-many command and control (Command and Control) between the controller and the infected hosts. and Control, C&C) network. Attackers spread bots through various channels to infect a large number of hosts on the Internet, and the infected hosts accept instructions from attackers through a control channel to form a botnet. This attack method provides the attacker with a hidden, flexible and efficient one-to-many command and control mechanism, enabling the attacker to achieve information theft, distributed denial of attack and spam sending, and has become an important aspect of the current network security field. threaten. [00...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More Patent Type & Authority Applications(China)
IPC IPC(8): H04L29/06H04L29/12
CPCH04L63/1416H04L63/1425H04L63/145H04L2463/144H04L61/4511H04L43/0876H04L43/04H04L41/142H04L43/065
Inventor 成黎田甜李依馨罗熙杨婧王利明
Owner ZTE CORP
Features
- R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
Why Patsnap Eureka
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Social media
Patsnap Eureka Blog
Learn More Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com