Malicious code obfuscation feature cleaning method
A technology of malicious code and feature selection method, applied in the field of machine learning information security, can solve problems such as poor timeliness, difficult system security, large computing resources, etc., to achieve the effect of improving effectiveness, prolonging effective time limit, and improving anti-interference.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
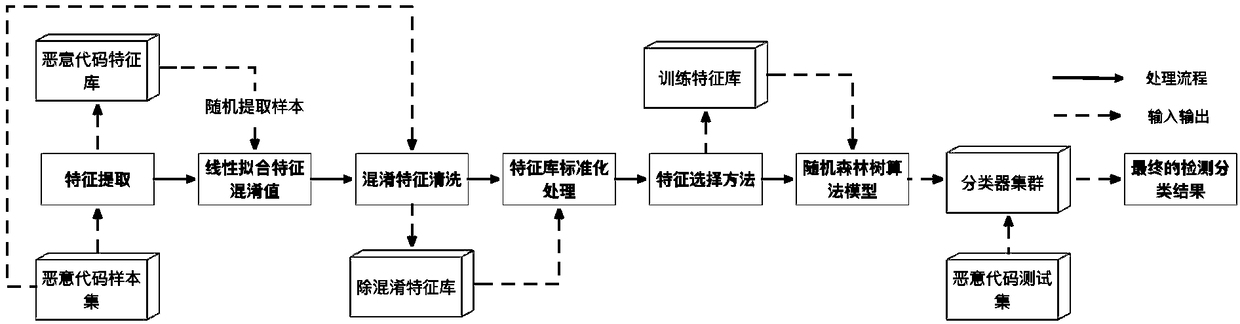
[0029] The present invention is explained and elaborated below in conjunction with relevant accompanying drawings:
[0030] In order to make the object, technical solution and features of the present invention more clear, the present invention will be further described in detail below in conjunction with specific implementation examples and with reference to the accompanying drawings. The overall frame diagram of the method of the present invention is as figure 1 shown. The flow of each step is described as follows:
[0031] (1) Extract the original malicious code features based on the n-gram algorithm, and build an initial feature library.
[0032] (2) Randomly extract samples to study the confusion threshold. A linear fitting equation is trained to predict the confusion threshold for unknown samples.
[0033] (3) Clean the confusing features in the feature library based on the confusing feature cleaning method.
[0034] (4) Standardize the feature database.
[0035] (5...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More