Key negotiation method, security guiding method and system for self-encryption solid state disk
A solid-state drive and key negotiation technology, applied in computer security devices, instruments, platform integrity maintenance, etc., to achieve the effect of improving security and flexibility, improving security strength, and reducing space overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
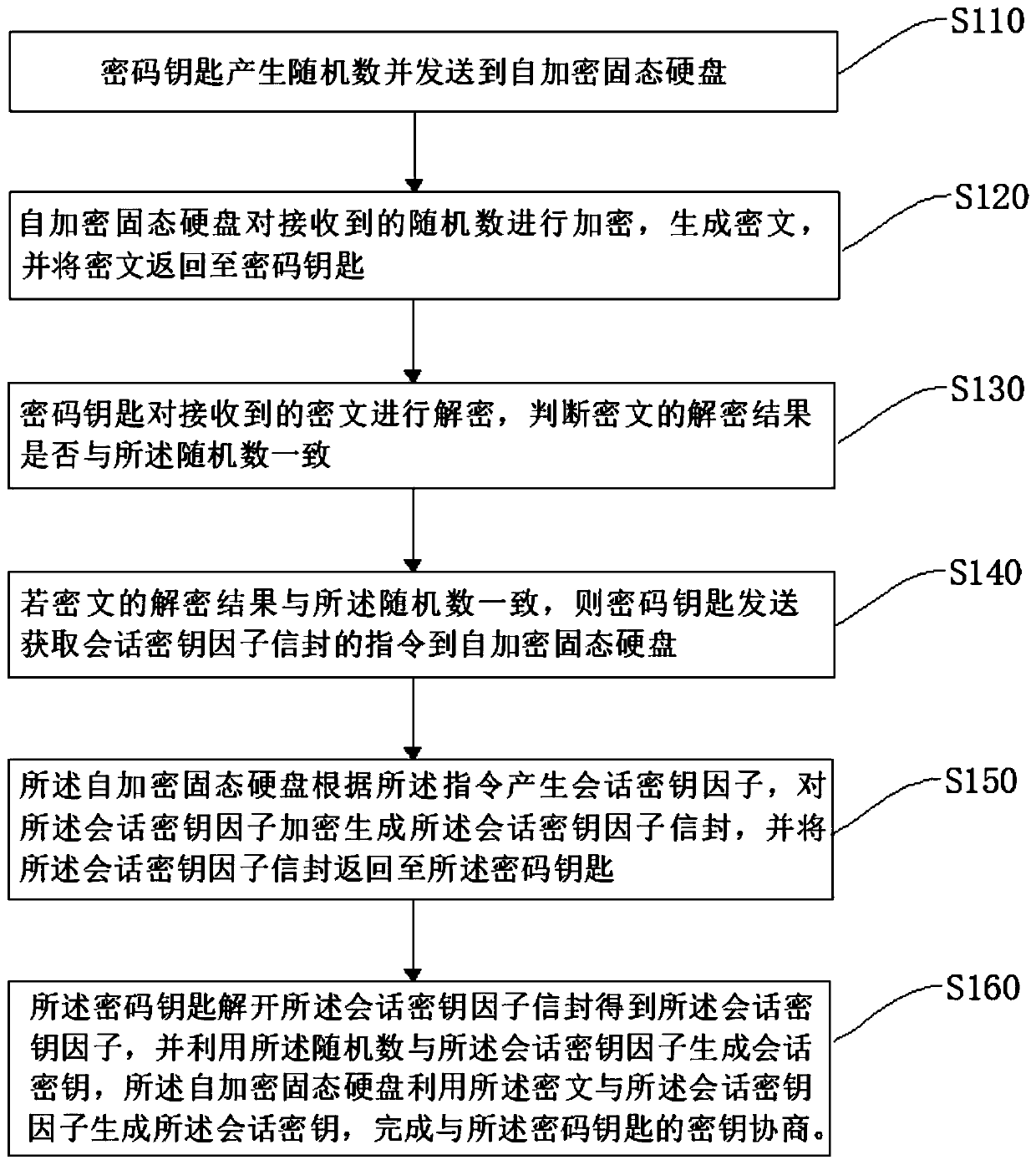
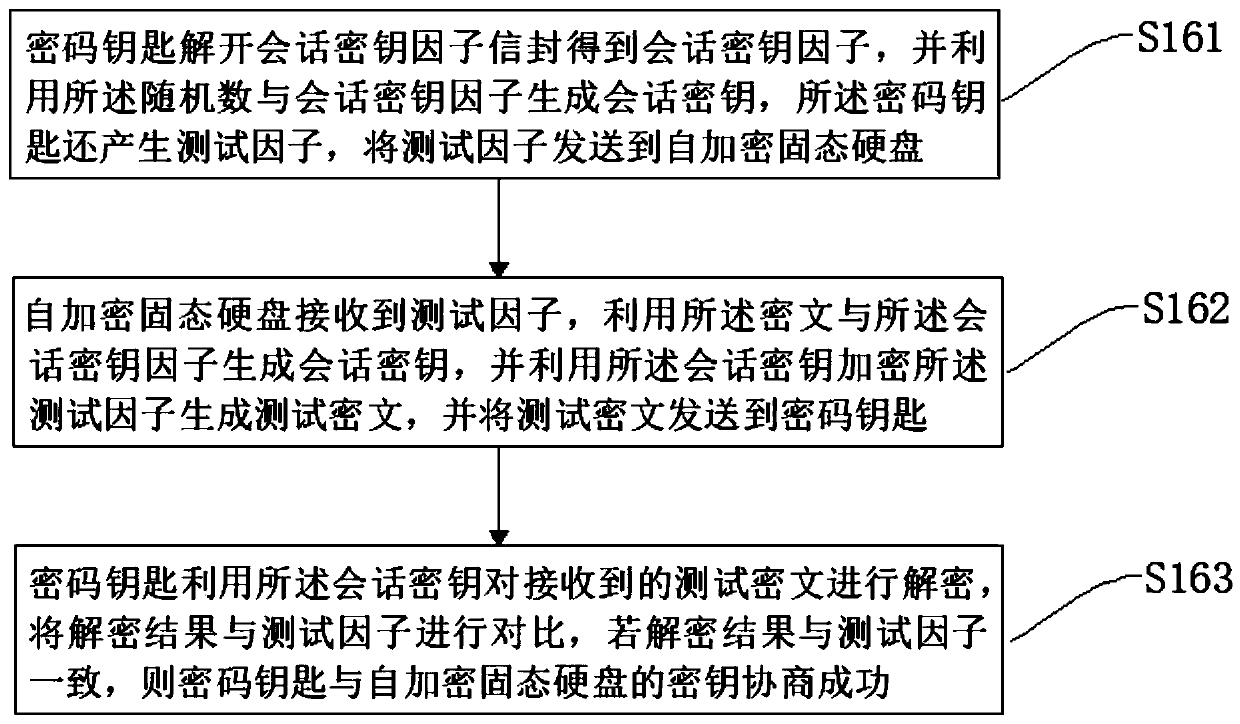
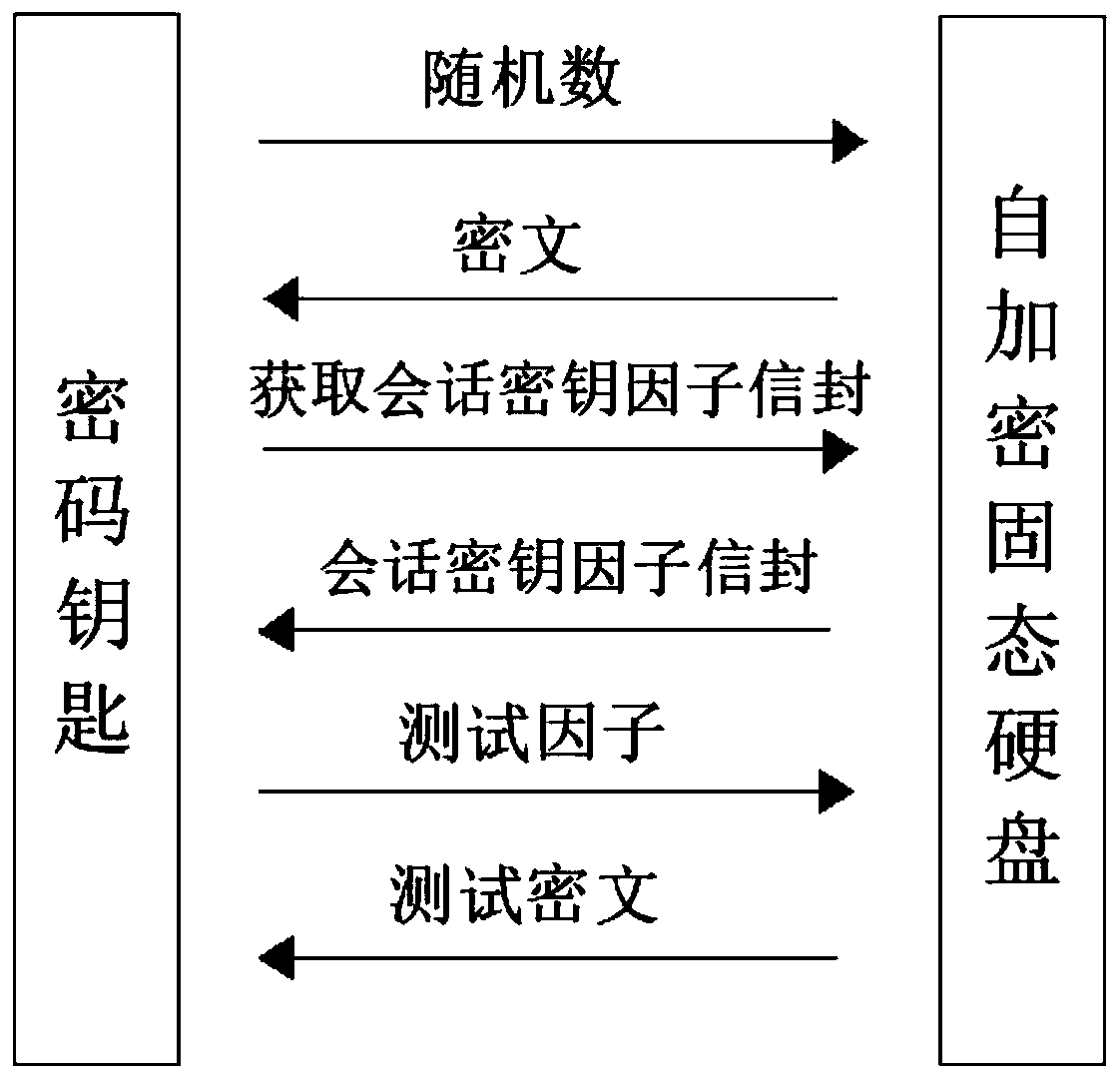
[0062] The specific embodiments of the present invention will be described in detail below with reference to the accompanying drawings. It should be understood that the specific embodiments described herein are only used to illustrate and explain the present invention, and not to limit the present invention.
[0063] The cryptographic key involved in this embodiment may be a USBKEY with cryptographic algorithms and storage functions. The self-encrypting solid-state drive involved in this embodiment supports the PCIe interface NVME protocol.
[0064] The self-encrypting solid state drive involved in this embodiment may be a solid state drive that performs full disk encryption or partition encryption. Full disk encryption refers to the encryption of user data, applications, and operating systems. The encryption key (DataEncrypt Key, hereinafter referred to as DEK) of the self-encrypting solid-state hard disk is used to encrypt all data stored in the hard disk, such as user files, s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More