Control flow monitoring method and device and storage medium
A technology for controlling flow and monitoring points, applied to electrical components, transmission systems, etc., can solve problems such as poor monitoring effect and failure to detect all abnormalities in control flow, and achieve the effect of improving monitoring effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] In order to make the purpose, technical solutions and advantages of the embodiments of the present application clearer, the following will further describe the embodiments of the present application in detail in conjunction with the accompanying drawings.
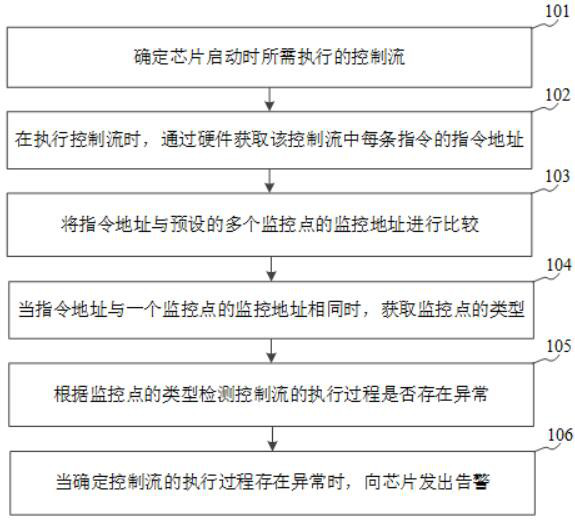
[0043] Please refer to figure 1 , which shows a flow chart of a method for monitoring a control flow provided by an embodiment of the present application, and the method for monitoring a control flow can be applied to a chip. The control flow monitoring method may include:
[0044] Step 101, determine the control flow to be executed when the chip starts.
[0045] Typically, there are multiple control flows in a chip that reside in unchangeable, fixed locations in non-volatile memory inside the chip. For example, reside in ROM (Read-Only Memory, read-only memory) or eFUSE (one-time programmable memory). If it resides in ROM, the control flow can be cured together with Boot ROM before chip tape-out; if it resides in...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com