Information recommendation method and system considering compactness of social network user group
A technology for social network and information recommendation, applied in the field of social network mining, can solve the problems of high time consumption, large breadth-first traversal strategy search range, and difficulty in sharing and utilization of calculation results, so as to save costs and improve experience.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0043] This embodiment provides an information recommendation method that considers the closeness of social network user groups;
[0044] An information recommendation method that considers the closeness of social network user groups, including:
[0045] S101: Obtain all users in the user group to be analyzed in the social network;
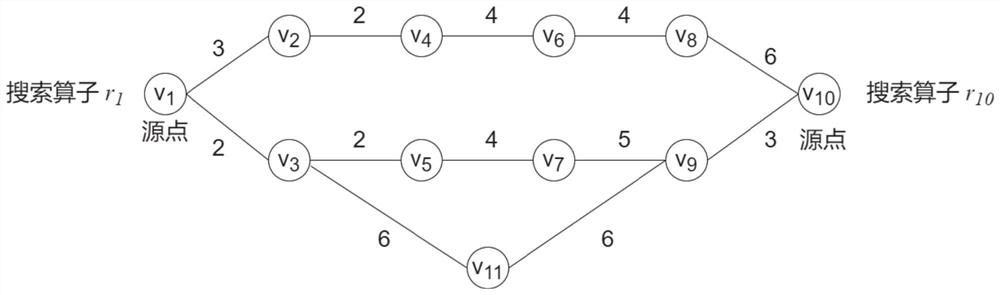
[0046] S102: Construct a graph structure according to all users in the user group to be analyzed; that is, each user is regarded as a vertex of the graph structure, and if there is a friend relationship or follow relationship between users, it means There are edges corresponding to the connection, and the number of interactions between users is regarded as the weight of the edge;
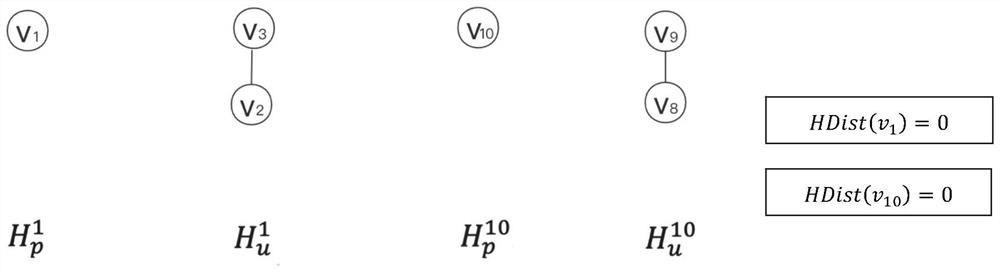
[0047] S103: Obtain a vertex set based on the graph structure, and query the shortest distance between any two vertices in the vertex set;
[0048]S104: weighted and summed the shortest distance between any two vertices to obtain the relationship closeness of the user...
Embodiment 2
[0127] This embodiment provides an information recommendation system that considers the closeness of social network user groups;
[0128] An information recommendation system that considers the closeness of social network user groups, including:
[0129] An acquisition module configured to: acquire all users in the user group to be analyzed in the social network;
[0130] The graph structure component module is configured to: construct a graph structure according to all users in the user group to be analyzed; that is, each user is regarded as a vertex of the graph structure, if there is a friend relationship or a follow relationship between users, then Indicates that there is a correspondingly connected edge between the vertices corresponding to the user, and the number of interactions between users is regarded as the weight of the edge;
[0131] A query module configured to: obtain a vertex set based on a graph structure, and query the shortest distance between any two verti...
Embodiment 3
[0138] This embodiment also provides an electronic device, including: one or more processors, one or more memories, and one or more computer programs; wherein, the processor is connected to the memory, and the one or more computer programs are programmed Stored in the memory, when the electronic device is running, the processor executes one or more computer programs stored in the memory, so that the electronic device executes the method described in Embodiment 1 above.
[0139] It should be understood that in this embodiment, the processor can be a central processing unit CPU, and the processor can also be other general-purpose processors, digital signal processors DSP, application specific integrated circuits ASIC, off-the-shelf programmable gate array FPGA or other programmable logic devices , discrete gate or transistor logic devices, discrete hardware components, etc. A general-purpose processor may be a microprocessor, or the processor may be any conventional processor, o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More