File protection method and device
A file and starting location technology, applied in digital data protection, secure communication devices, computer security devices, etc., can solve problems such as key confusion processing, reduce the risk of leakage, reduce workload, and improve randomness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
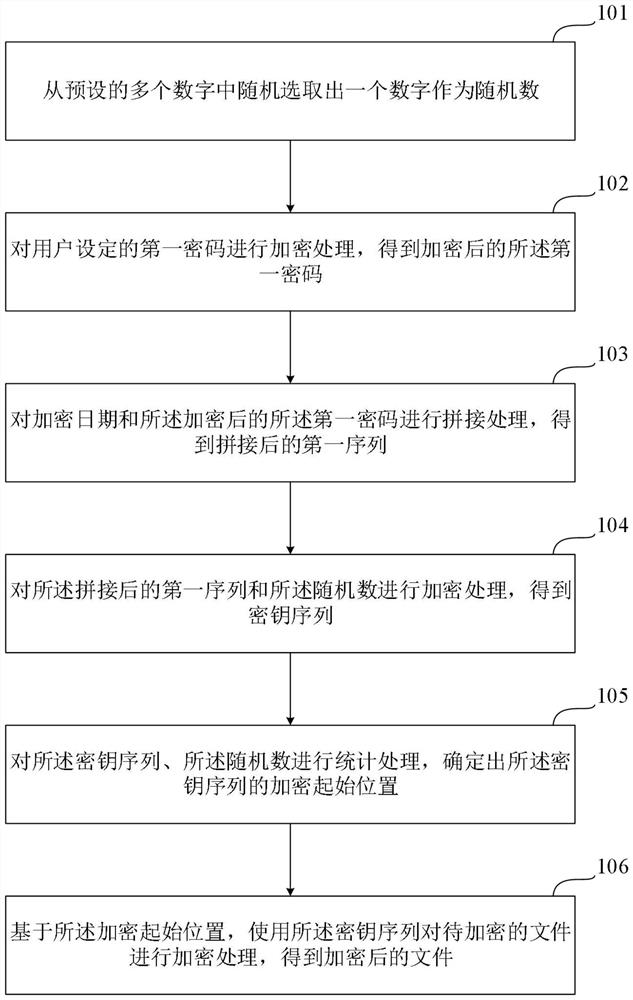
[0066] In order to make the purpose, technical solution and advantages of the application clearer, the application will be further described in detail below in conjunction with the accompanying drawings. Apparently, the described embodiments are only some of the embodiments of the application, not all of them. Based on the embodiments in this application, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the scope of protection of this application.
[0067] The exemplary embodiments and descriptions of the application are used to explain the application, but not to limit the application. In addition, elements / members with the same or similar numbers used in the drawings and embodiments are used to represent the same or similar parts.
[0068] It should be understood that the "first", "second", etc. used in this application do not specifically refer to the meaning of sequence or order, nor are they used to limit thi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More