Memory loading method based on PE file transformation
A memory loading and file technology, applied in the field of network security, can solve problems such as enhancement and inability to deal with unknown memory loading methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
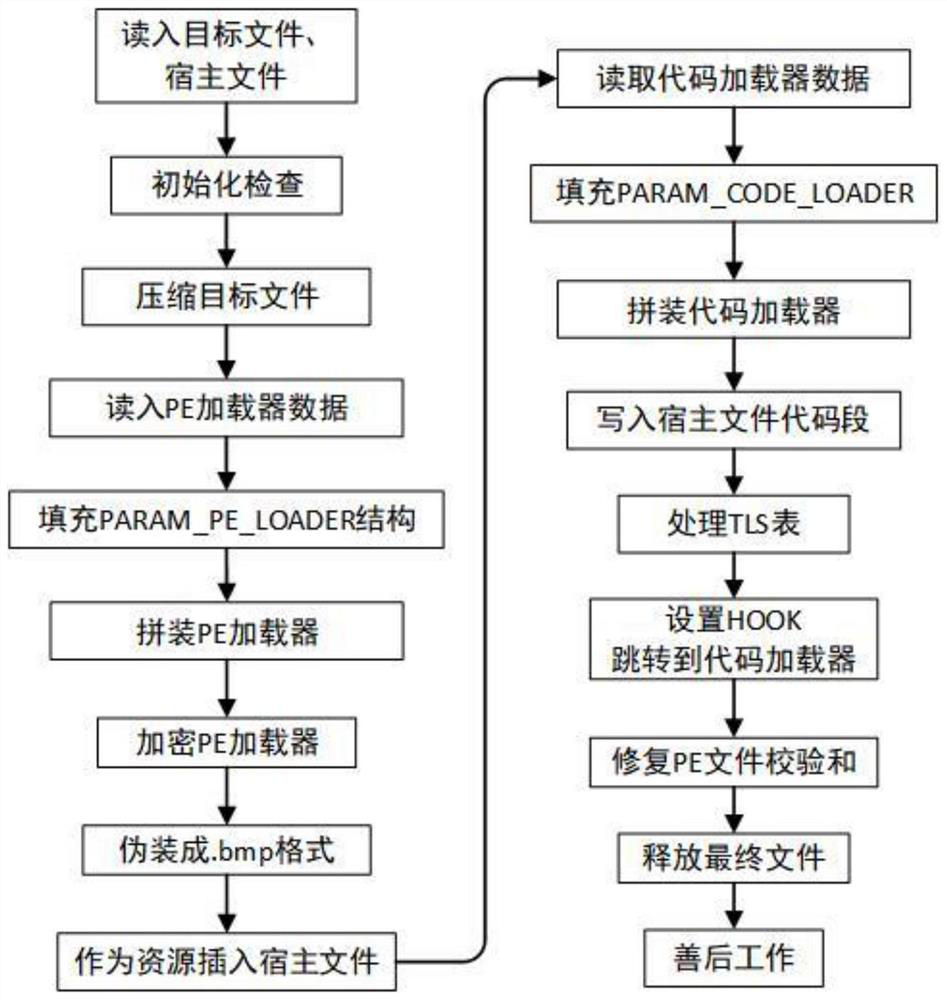
[0025] The invention proposes a memory loading method based on PE file transformation, which can load target PE files into memory and bypass the detection of some security products. Such as figure 1 As shown, the process of transforming the host file: first read the target file and the host file into the memory, and then perform an initialization check on both, this step is mainly to check whether both are PE files; then use the LZMA algorithm to perform Compression; then read the data of the PE loader, that is, the Shellcode, into the memory, and fill the PARAM_PE_LOADER structure. The PARAM_PE_LOADER structure here provides external parameters for the PE loader in the form of Shellcode. The parameters include ①The size of the compressed target program, ②The target program Original size, ③The total size of the PE loader and other parameters, among which ①②Guide the decompression of the target program, and other parameters ensure the normal operation of the PE loader; then ass...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More