Log analysis method and log analysis device
An analysis method and log technology, applied in the field of information security, can solve the problems of large manpower and material resources, tediousness, and boring, etc., and achieve the effect of reducing the implementation cycle, low entry cost, and low maintenance cost
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
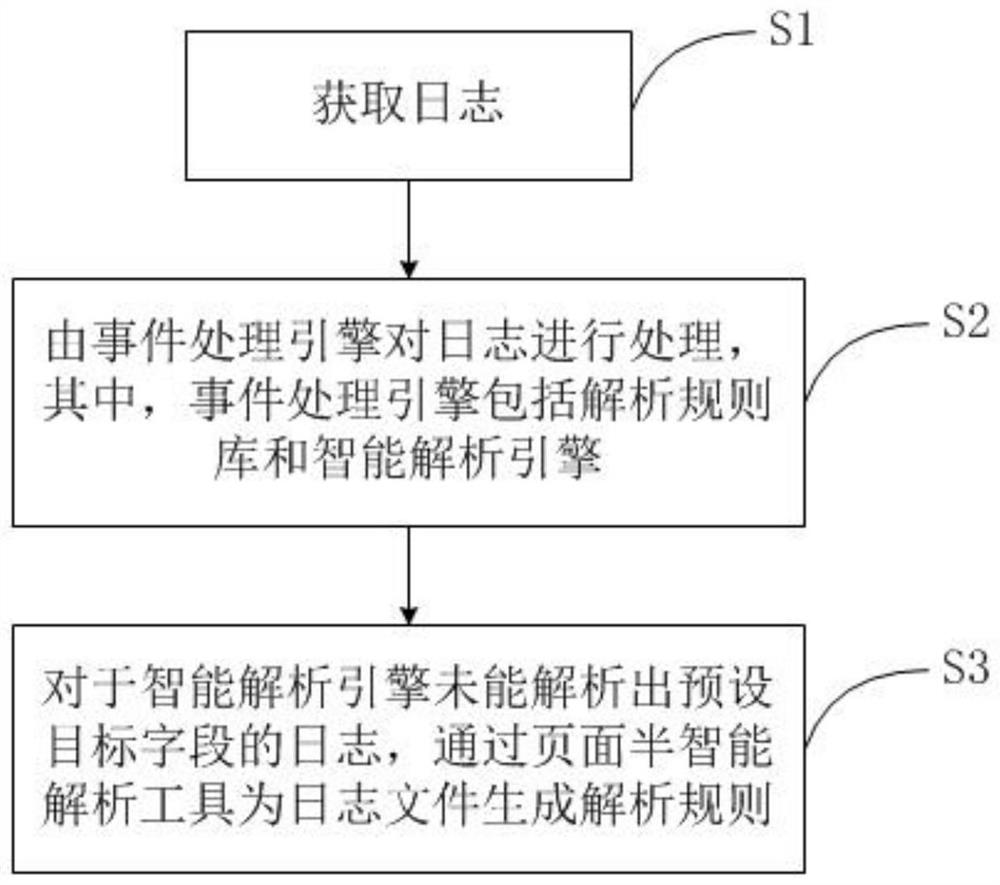
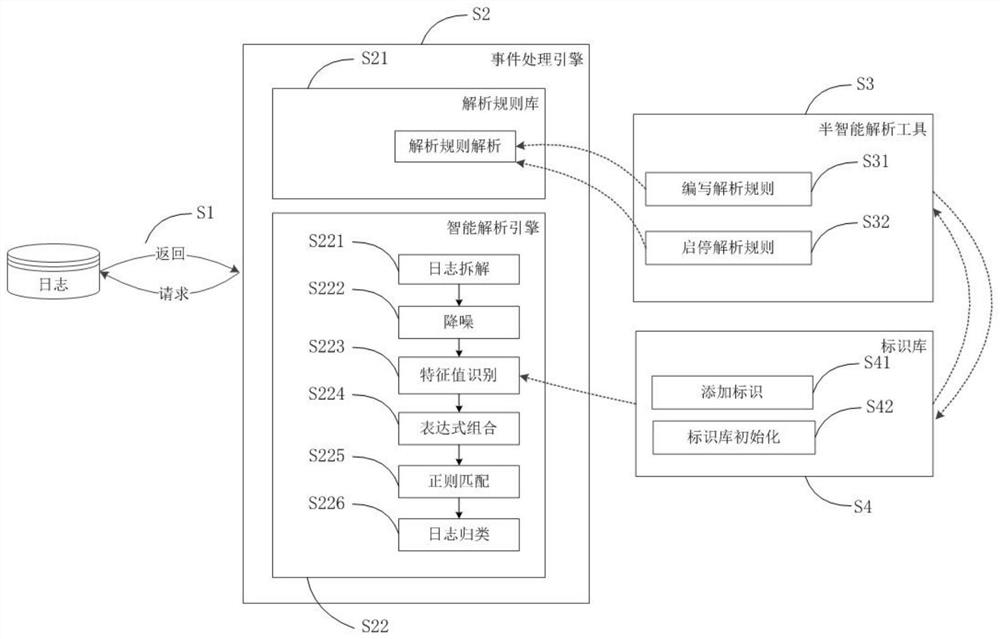
Method used
Image
Examples
Embodiment Construction
[0052] In order to make the purposes, technical solutions and advantages of the embodiments of the present application clearer, the following will clearly illustrate the spirit of the content disclosed in the application with the accompanying drawings and detailed descriptions. After any person skilled in the art understands the embodiments of the content of the application , when it can be changed and modified by the technology taught in the content of the application, it does not depart from the spirit and scope of the content of the application.
[0053] The exemplary embodiments and descriptions of the present application are used to explain the present application, but not to limit the present application. In addition, elements / members with the same or similar numbers used in the drawings and embodiments are used to represent the same or similar parts.
[0054] As used herein, "first", "second", ... etc. do not specifically refer to a sequence or order, nor are they used ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More