Low-power-consumption key destroying device
A technology of destroying keys and key buttons, which is applied in the field of low-power consumption destroying devices, and can solve problems such as conflicts, affecting user experience, and inability to adjust the design
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
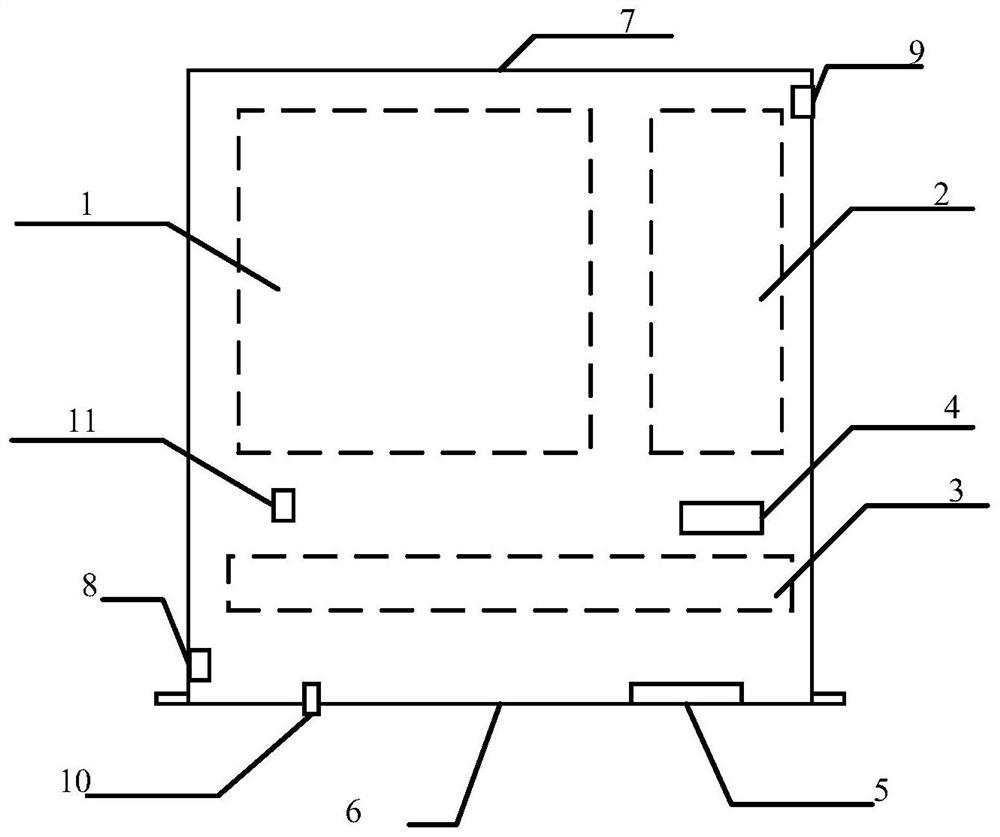
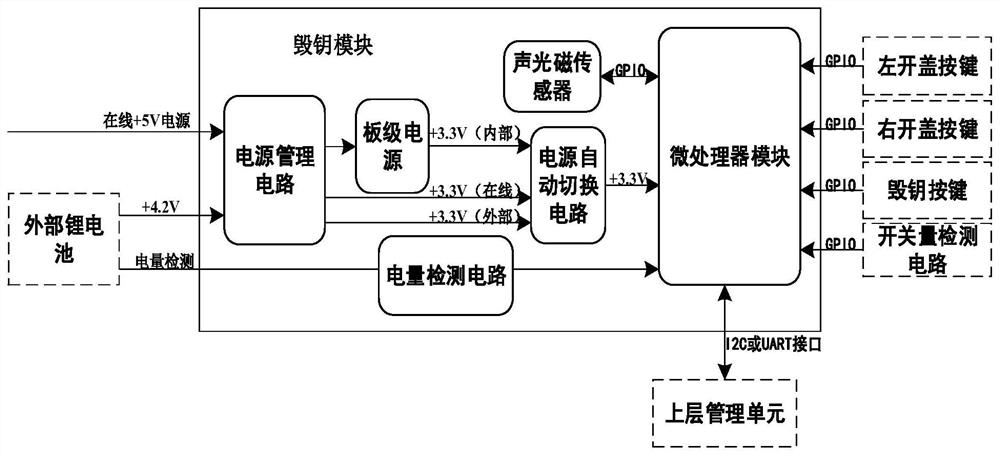
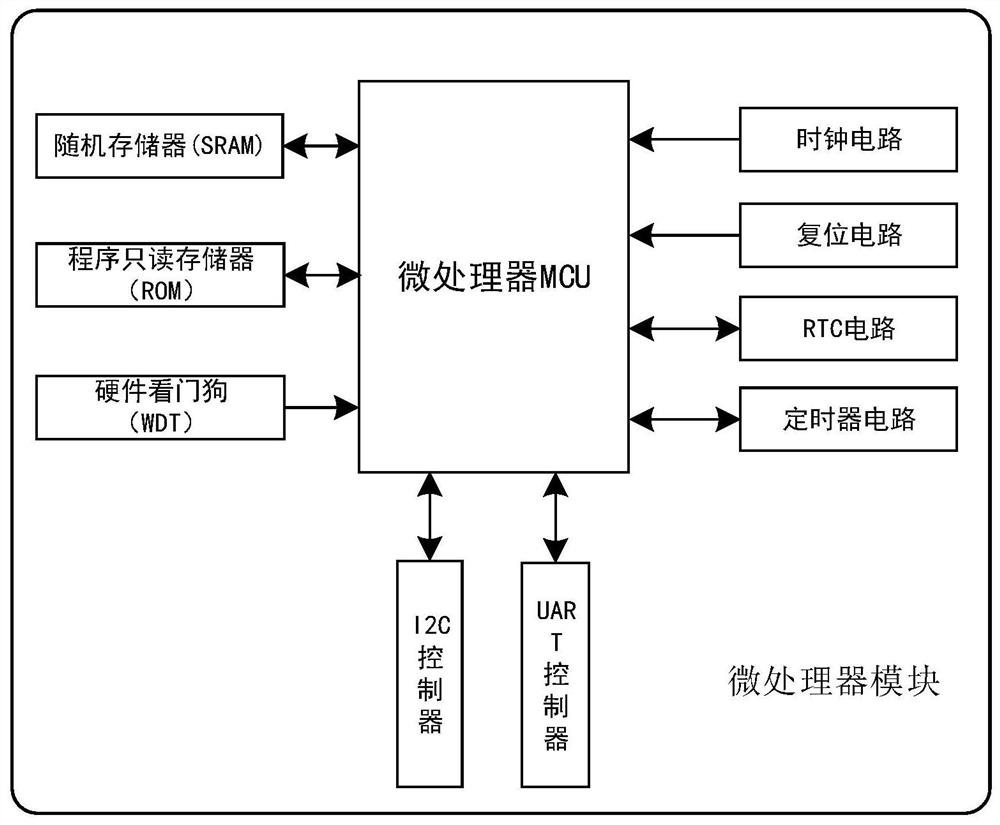
[0027] The technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the drawings in the embodiments of the present application.
[0028] In the following introduction, the terms "first" and "second" are only used for the purpose of description, and should not be understood as indicating or implying relative importance. The following description provides multiple embodiments of the present invention, and different embodiments can be replaced or combined in combination, so the present invention can also be considered to include all possible combinations of the same and / or different embodiments described. Thus, if one embodiment contains features A, B, C, and another embodiment contains features B, D, then the invention should also be considered to include all other possible combinations containing one or more of A, B, C, D Although this embodiment may not be clearly written in the following content.
[...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More