Cloud data encryption storage and sharing method, device and system
A data encryption and cloud technology, applied in the blockchain field, can solve the problems that cloud data cannot guarantee the authenticity, traceability and data leakage of storage and sharing records
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
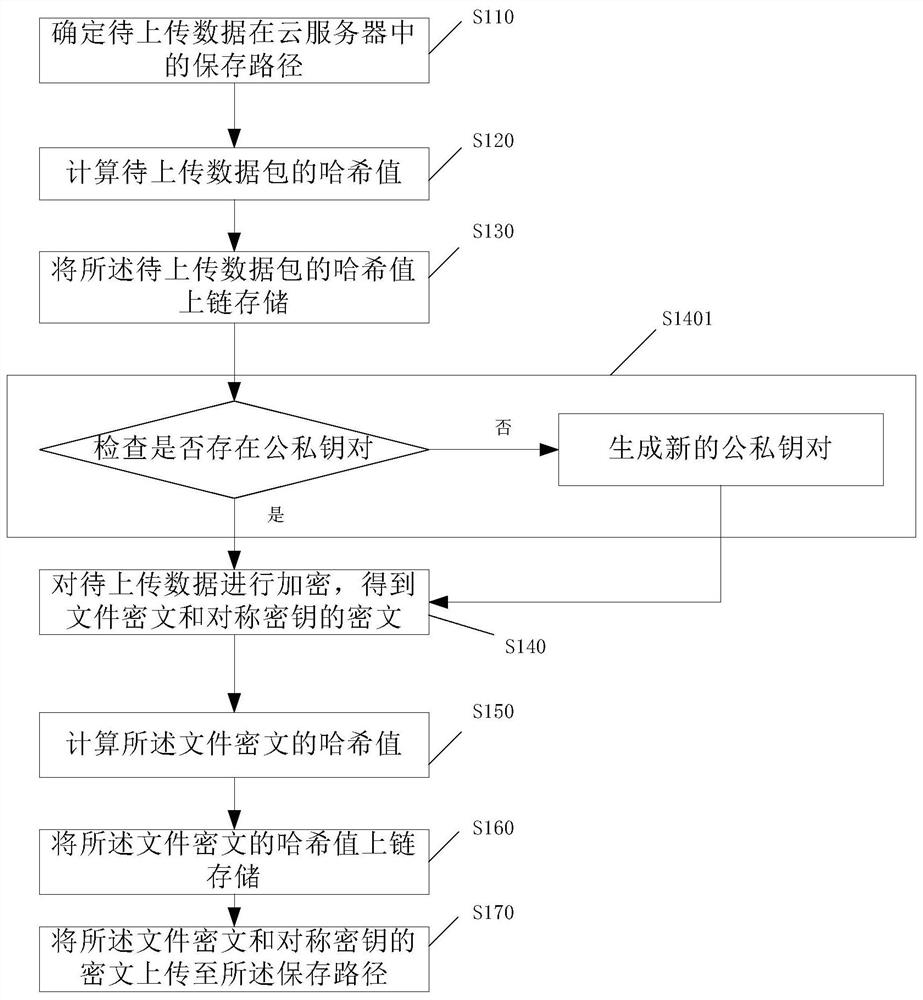
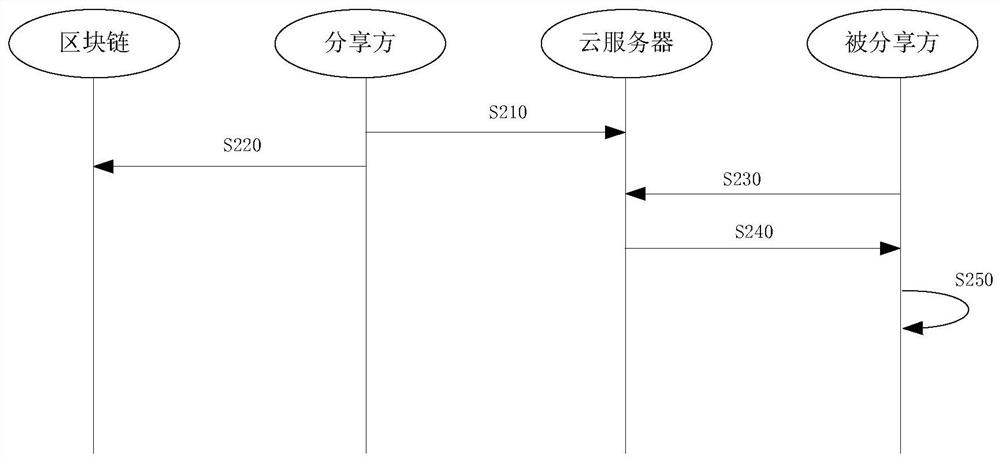
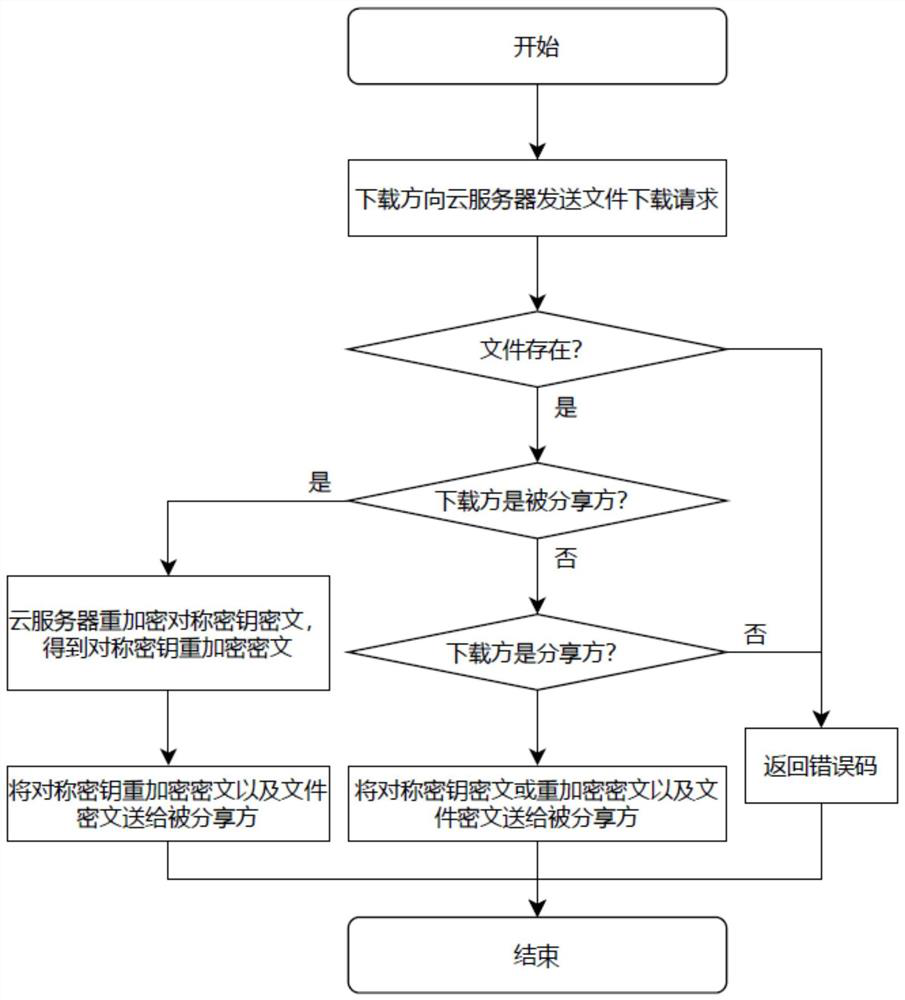
[0054]Blockchain has the characteristics of decentralization, traceability, tamper-proof, and anonymity. Through blockchain technology, data confirmation can be realized to a certain extent, and data security can be further ensured. Proxy re-encryption technology is an encryption method that can safely convert ciphertext. This technology can convert the ciphertext encrypted and uploaded by user A with his own public key into another form of ciphertext, so that user B can use his own The private key decrypts the converted ciphertext, and does not disclose any corresponding plaintext information during the entire conversion process, which can ensure safe access and sharing of cloud data. The embodiment of this application is based on the existing technology of cloud data storage, adding technical means such as data uplink, proxy re-encryption public-private key pair encryption and decryption, and the method of this application will be described in detail below:
[0055] see fig...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More