Sybil attack detection method based on node attention and forwarding characteristics and electronic equipment
An attack detection and node technology, applied in the field of Sybil attack detection, can solve problems such as poor robustness, and achieve the effect of improving accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
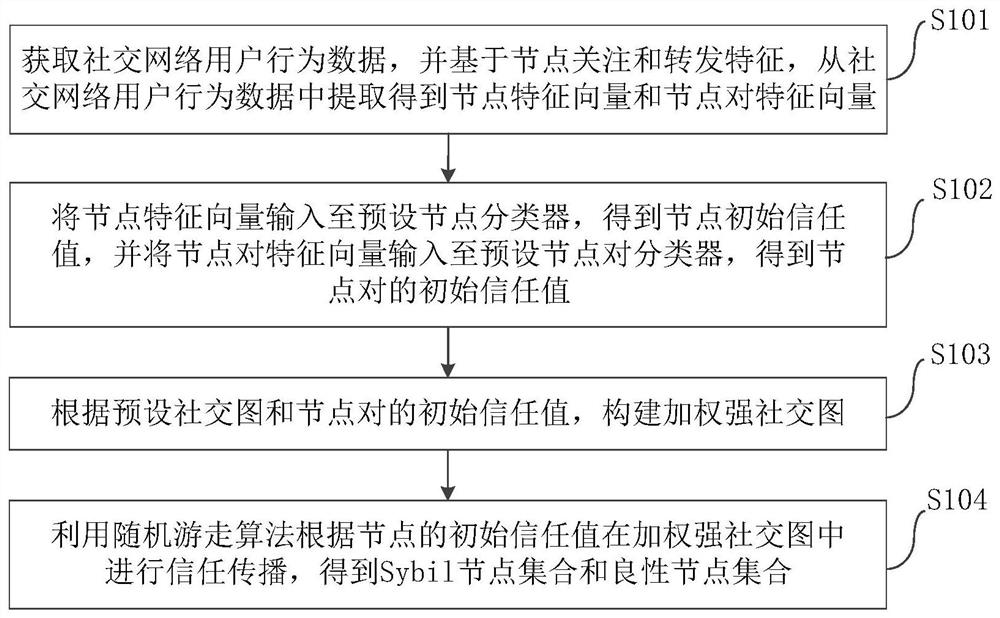
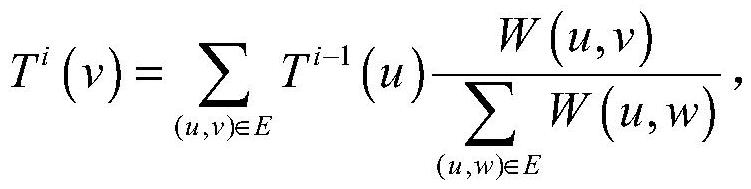
[0013] Embodiments of the present invention are described in detail below, examples of which are shown in the accompanying drawings, wherein the same or similar reference numerals designate the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary and are intended to explain the present invention and should not be construed as limiting the present invention.
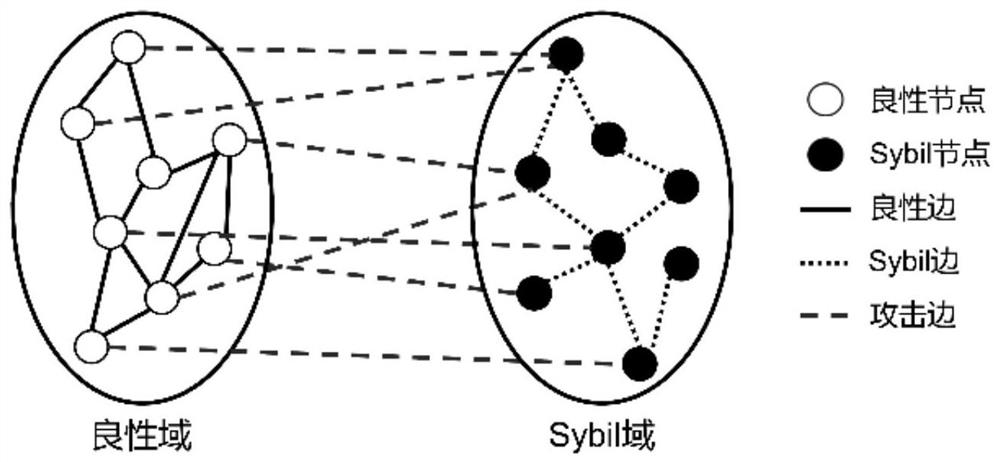
[0014] Sybil attacks refer to attackers using a large number of false identities they create to carry out malicious activities and destroy system functions. As a basic attack in distributed systems, Sybil attack was common in sensor networks in the early stage, and was widely used in social networks in the later stage. Since social networks have no limit on the number of identities created by users and lack of effective identity authentication mechanisms, social networks are vulnerable to Sybil attacks. Attackers us...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More