Attack behavior detection method and device and attack detection equipment
A behavioral and detection model technology, applied in the field of network security, can solve the problems of host performance degradation, violation of user privacy, large processor resources and memory resources, etc., and achieve the effect of low risk of violation of user privacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0115] In order to make the purpose, technical solution and advantages of the present application clearer, the implementation manners of the present application will be further described in detail below in conjunction with the accompanying drawings.
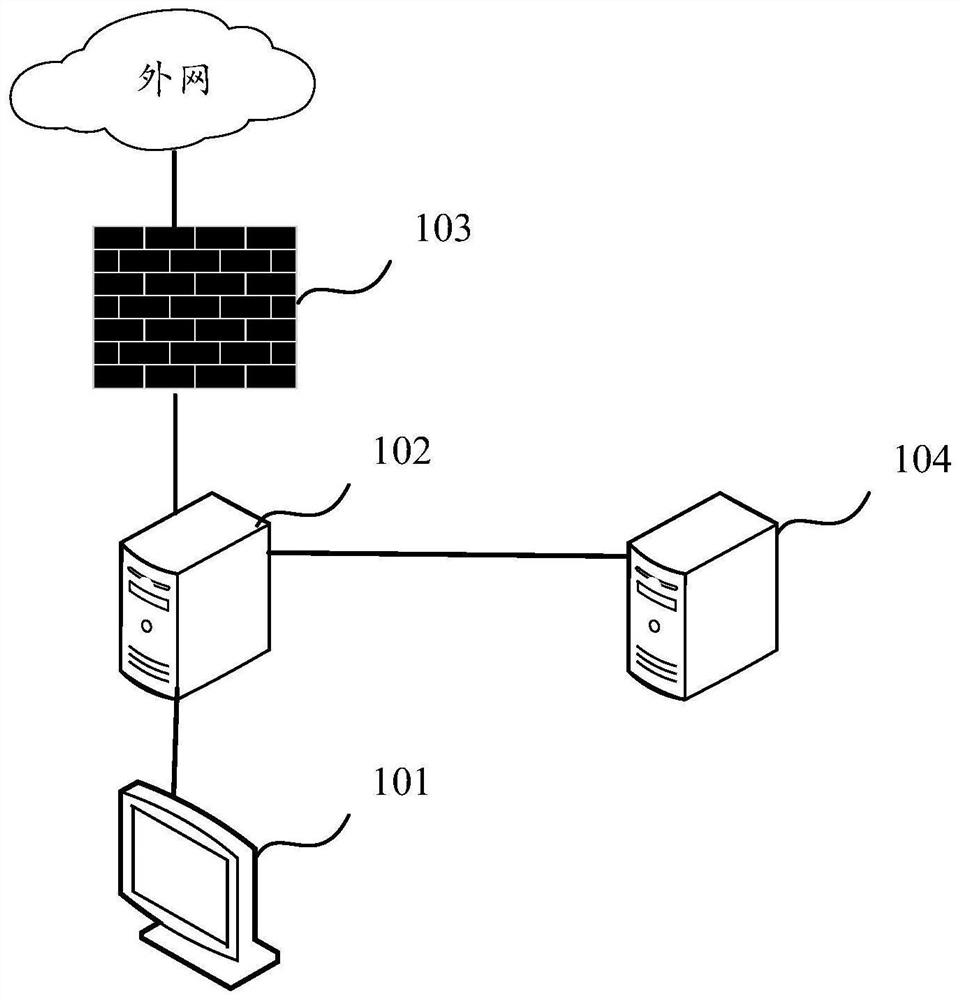
[0116] figure 1 It is a system architecture diagram involved in an attack behavior detection method provided by an embodiment of the present application. see figure 1 , the system architecture includes a host 101 , an HTTP proxy device 102 , a firewall 103 and an attack detection device 104 . The host 101 can communicate with the HTTP proxy device 102 in a wireless or wired manner. The HTTP proxy device 102 can communicate with the firewall 103 in a wireless or wired manner. The HTTP proxy device 102 can also communicate with the attack detection device 104 in a wireless or wired manner.
[0117] The host 101 is used to transmit (send or receive) HTTP message flow data. The HTTP proxy device 102 is used to proxy the host 101...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More