System and method for implementing interoperability by using interconnected voice verification system
A voice verification and voice technology, applied in user identity/authority verification, transmission system, voice analysis, etc., can solve consumer disadvantages and other problems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
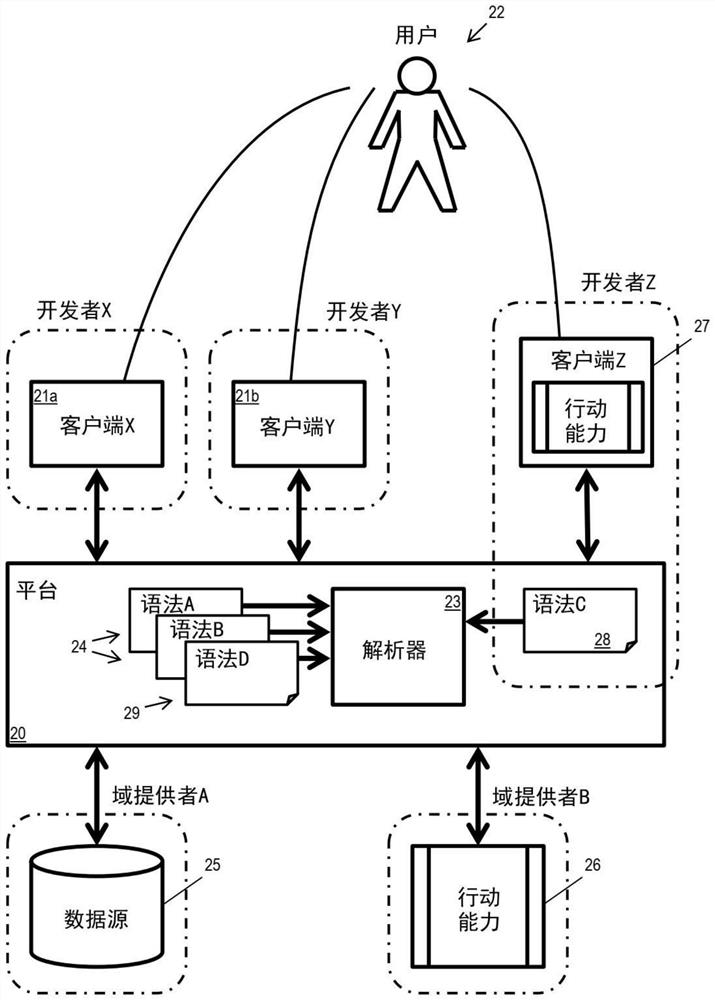
[0031] The following describes a system of process steps and a system of machines and components to achieve interoperability through interconnected voice authentication systems. Some implementations use a computer executing software instructions stored on a non-transitory computer-readable medium. The examples below illustrate design choices for various aspects of such systems. Overall, the design choices for the different aspects are independent and can be collaborated in any combination.
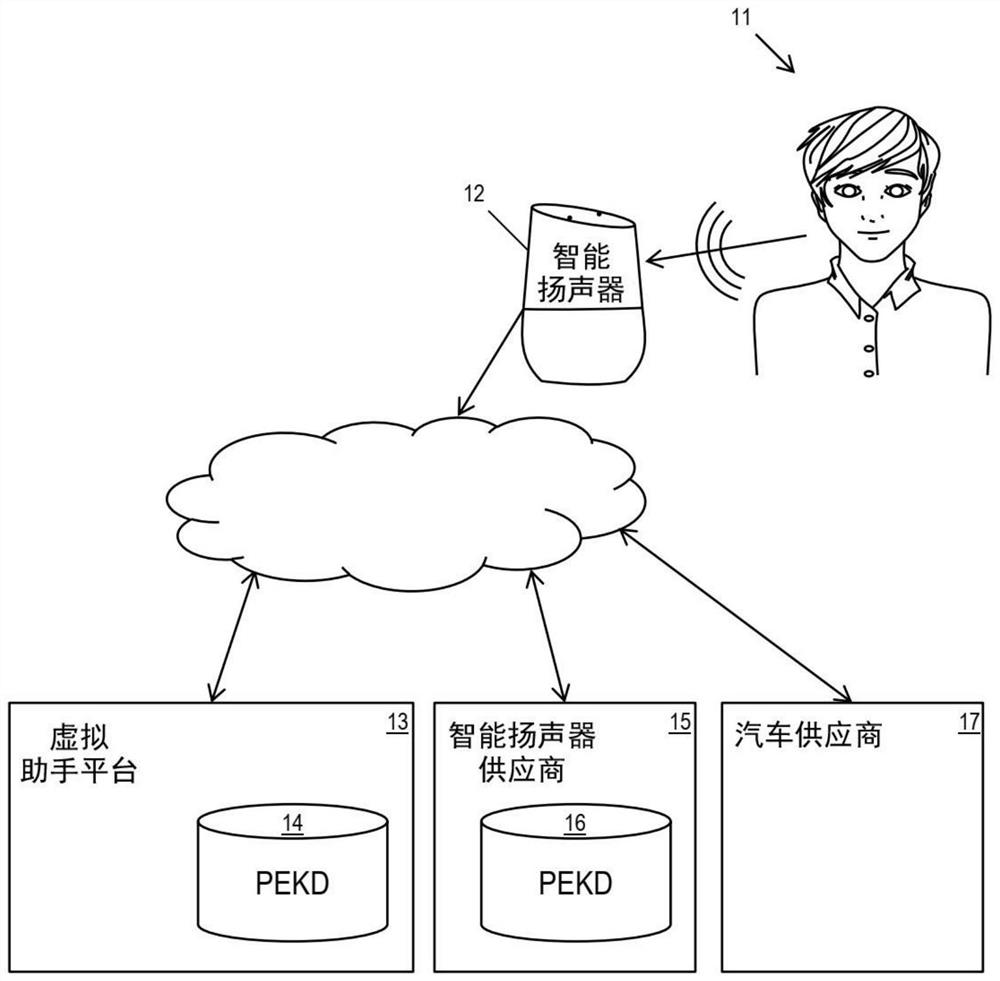
[0032] PEKD
[0033] The Personal Extended Knowledge / Preference Database (PEKD) is a personal database. It helps to expand an individual's personal knowledge / intelligence / preference / awareness. PEKD is stored and maintained by the personal data service provider's servers. Users can use speech and other input to construct and access PEKD and some of the personal data it stores. Note that for simplicity, in this application, the provider's server may also be referred to as the provider. ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com