Optimizing boundary information access in buffer protection
A boundary information and buffer technology, applied in memory architecture access/allocation, instruments, register devices, etc., can solve problems such as remote code execution or privilege escalation defects, dangers, intrusions, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
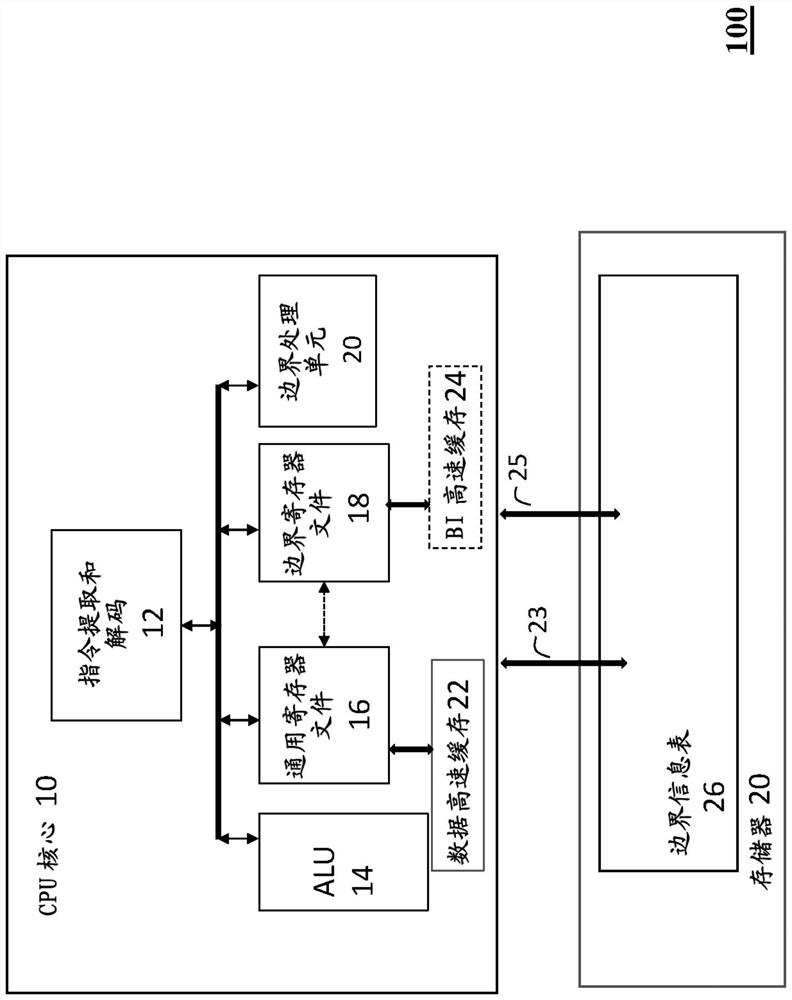
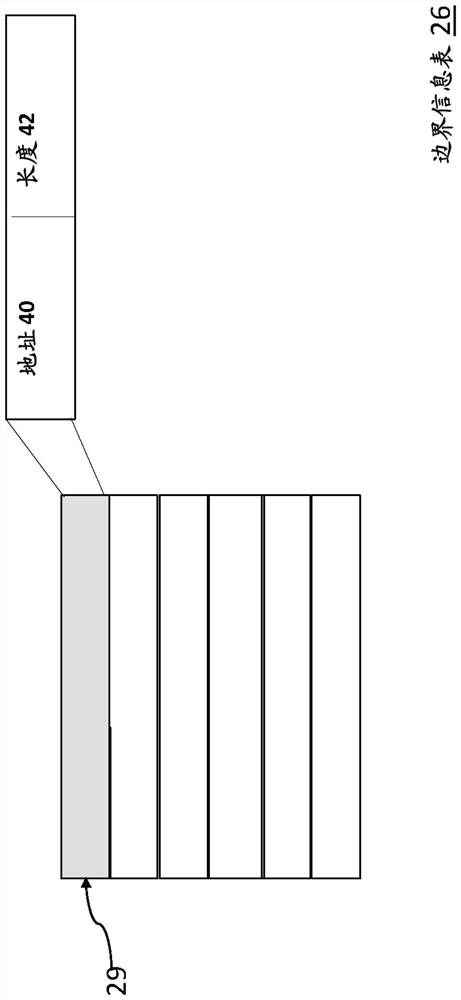
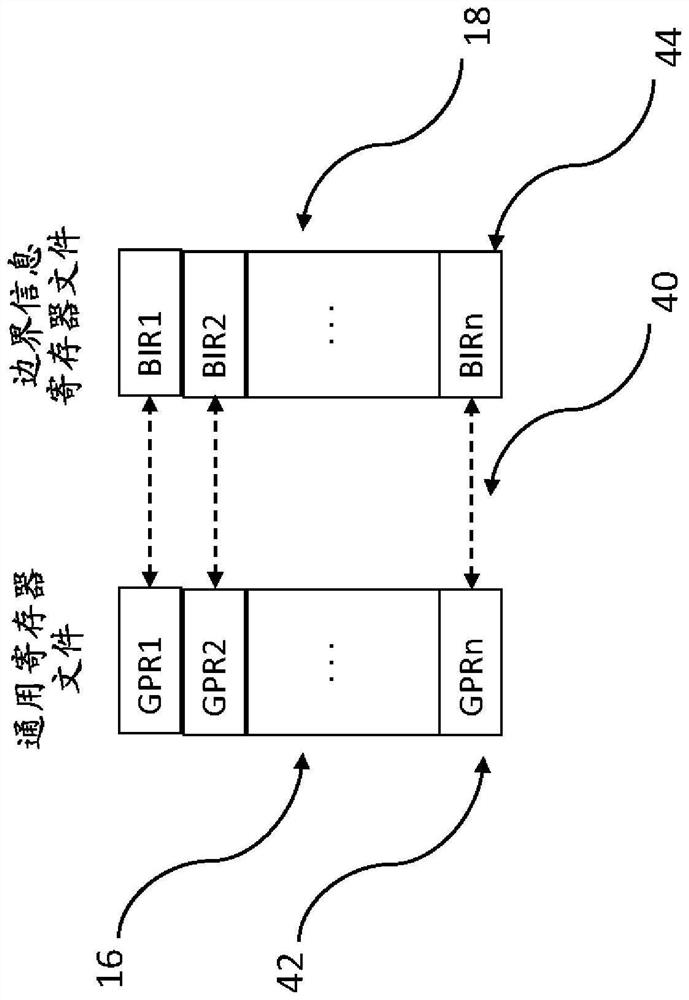
[0033] The present invention will now be described with reference to the drawings, wherein like reference numerals refer to like parts throughout. It is emphasized that, in accordance with common practice, the various features of the drawings are not necessarily drawn to scale. On the contrary, the dimensions of the various features may be arbitrarily expanded or reduced for clarity. The exemplary embodiments are provided below for purposes of illustration and not for limitation of the claims. Furthermore, please note that any of the steps may be performed in a different order, or in combination, or concurrently. Additionally, any of the structures and embodiments shown may be modified or combined.
[0034] Memory references outside of their scope can cause serious security problems. Buffer overflow vulnerability has been a problem for at least 30 years, eg Morris Internet Worm (1988). Buffer overflow vulnerabilities have enabled many forms of attack, including buffer over...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More