Chaotic-hash structuring method based composite non-linear digital wave-filter
A digital filter and construction method technology, applied in the field of information security, can solve the problems of destroying the global uniform distribution characteristics of PWL, the hash results are not uniformly distributed, and difficult to resist statistical attacks, and achieve easy expansion, software and hardware implementation, and simple implementation. Fast, resistant to the effects of linear analysis
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
[0025] The present invention will be further described in detail below in conjunction with the drawings and specific embodiments.
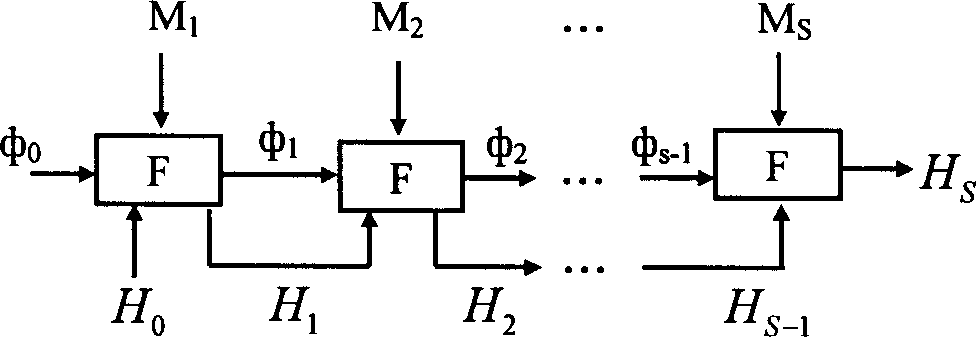
[0026] The general method of the method for constructing a chaotic hash based on a composite nonlinear digital filter of the present invention is as follows:
[0027] 1) Initialization:
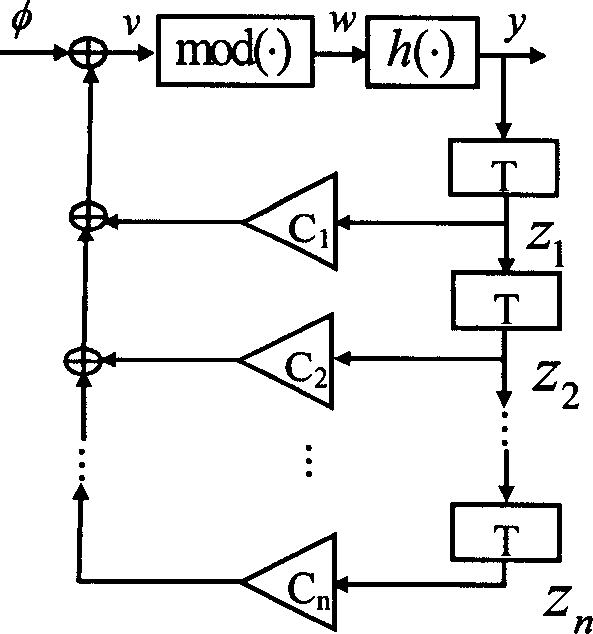
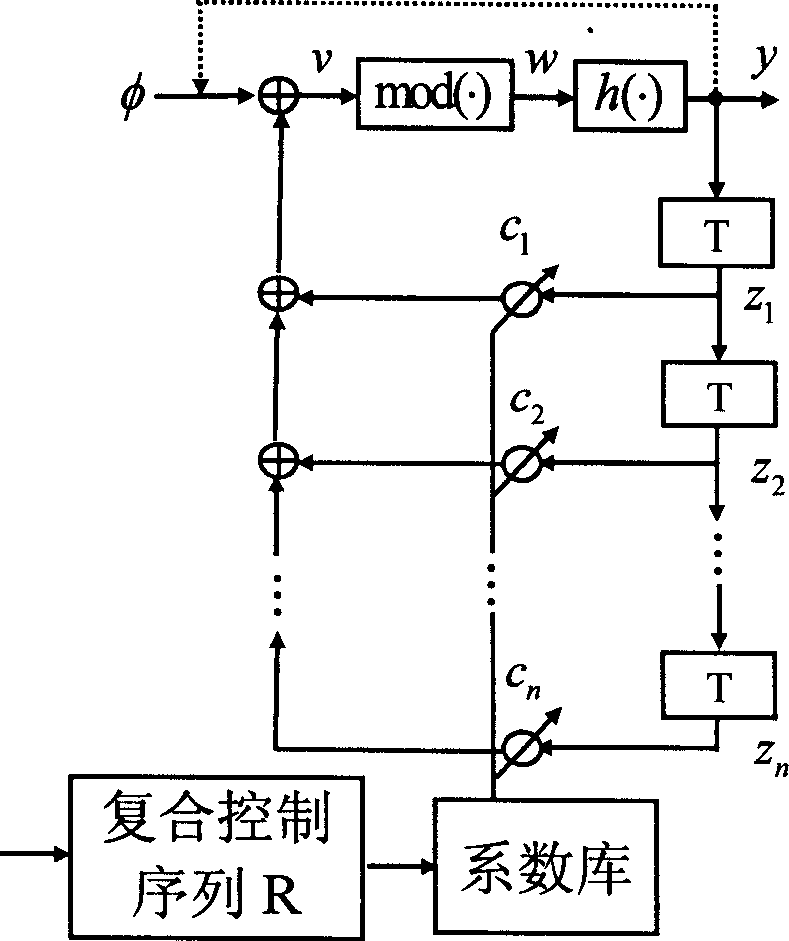
[0028] figure 1 Show: an n-dimensional nonlinear autoregressive digital filter can be expressed as
[0029] Where φ∈(-1,1) is the initial input signal of the filter, {z 1 ,z 2 ,…z n }∈(-1, 1) is the initial state of the filter, {c 1 , C 2 ,...C n } Is the filter coefficient, T is the unit delay, h(·) is the non-linear transfer function, mod(·) is the hardware overflow function, y is the output of the filter. When the filter satisfies the Kelber condition, that is, it satisfies the following three conditions: ①Coefficient c n ∈□, |c n |>1, {c i ∈R, c i ≠0|i=1,2,...n-1}; ②The absolute value of the characteristic root of the filter is not 1; ③The nonlinear transfor...
Embodiment 1
[0037] n=2-dimensional nonlinear digital filter, k=2 sets of coefficients pre-stored in the coefficient library, and a chaotic hash construction method under the condition that the hash length L=128.
[0038] 1) Initialization:
[0039] N-dimensional autoregressive nonlinear digital filter, n=2, p=1, parameter library pre-stored k=2 p =2 sets of coefficients {c 0 =[3.57, 4], c 1 =[5.7,7]}, the hash length L=128 bits, the initial value of the filter is the key SK={φ 0 ,z 1 ,z 2 }={φ 0 = 0.5648, z 1 = -0.564, z 2 =0.679}, the initial hash value H 0 = { 0 } 1 128 , Non-linear mapping h ( w ) = - 1 + 2 w / ...
Embodiment 2
[0052] n=3-dimensional nonlinear digital filter, k=4 sets of coefficients pre-stored in the coefficient library, and a chaotic hash construction method under the condition of L=256 hash length.
[0053] 1) Initialization:
[0054] n-dimensional autoregressive nonlinear digital filter, n=3, p=2, parameter library pre-stored k=2 p =4 sets of coefficients {c 0 =[2.53, -0.63, 2], c 1 =[5.1, 1.2, 5], c 2 =[-3.64, 4.23, 3], c 3 =[0.75, 3.24, 4]}, the hash length L=256 bits, the initial value of the filter is the key SK={φ 0 ,z 1 ,z 2 ,z 3 }={φ 0 = 0.5648, z 1 = -0.564, z 2 = 0.679, z 3 =0.132}, the initial hash value H 0 = { 0 } 1 256 , The non-linear mapping h(w), the quantization function T(x) output by the filter, and the hardware overflow function mod(·) are all the same as in the first embodiment. To simplify the length, we al...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More