Method of network equipment invaded detection
A technology of intrusion detection and network equipment, which is applied in the field of communication network security, can solve the problems of high network resource consumption and high cost of intrusion detection methods, and achieve the effects of low resource consumption, rich security analysis strategies, and great flexibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0016] The technical features and functional features of the present invention will be further described below in conjunction with specific embodiments, with the purpose of better explaining the present invention, but not intended to limit the protection scope of the present invention.
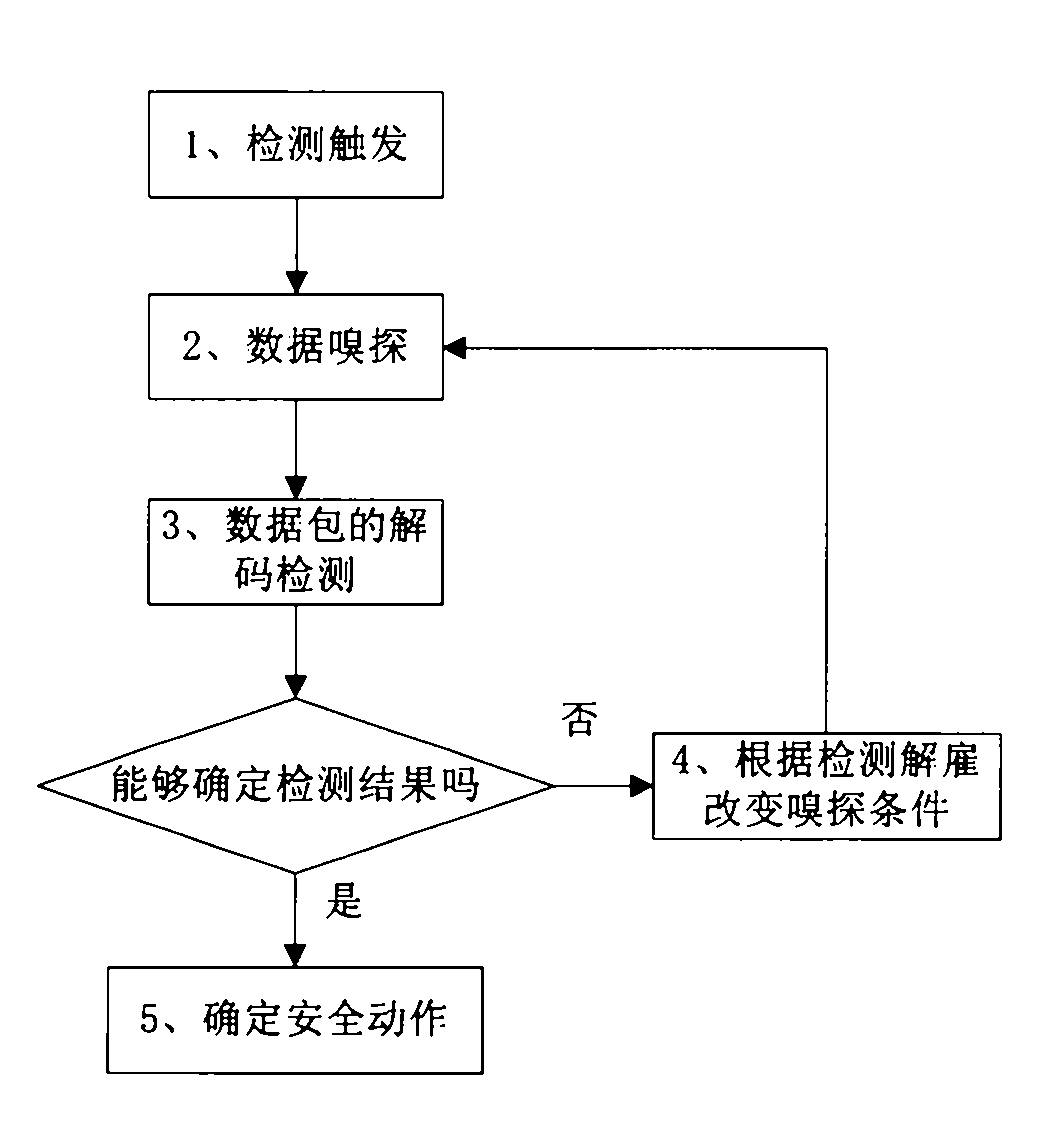
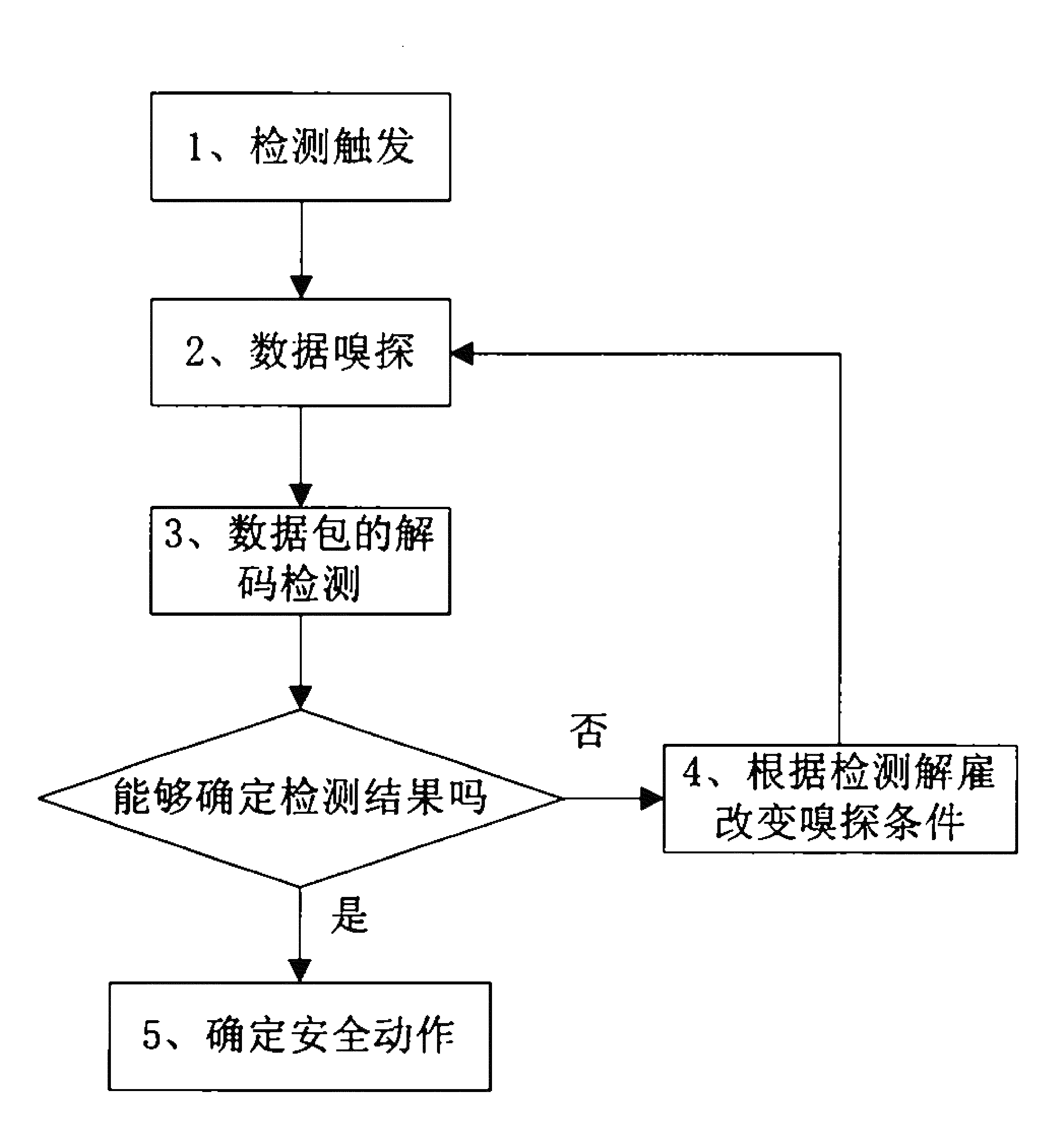
[0017] see figure 2 , the present invention comprises the following steps:
[0018] 1. Intrusion detection; intrusion detection can be executed all the time, or it can be triggered under set conditions. For example, when abnormal traffic on a certain port is detected, execution starts.
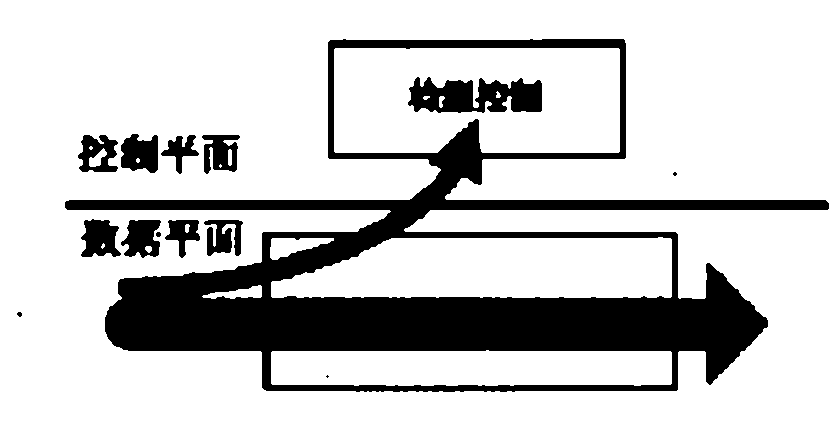
[0019] 2. Data sniffing; the feature of this method is that all data flows cannot be sent to the control plane, but are filtered according to certain conditions (such as only collecting the flow of ports with specified abnormal flows, or subdividing them to collect abnormal ports The traffic of the specified IP address segment on the network), and part of the data flow is sent to the control plane for analy...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More