Method and system for agent signature
A proxy signature and signer technology, applied in data processing applications, user identity/authority verification, business, etc., can solve the problems of difficult server non-repudiation and poor operability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
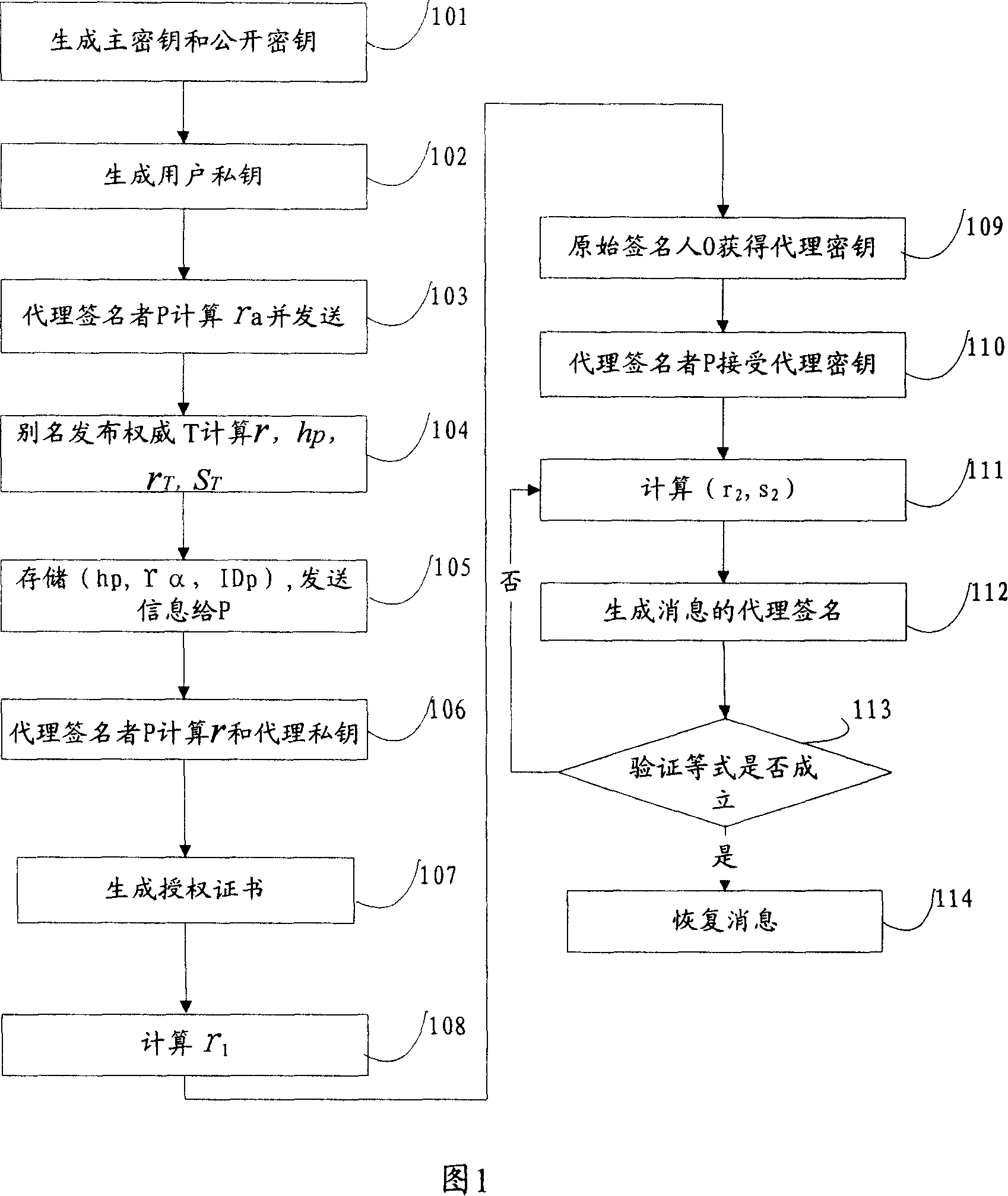
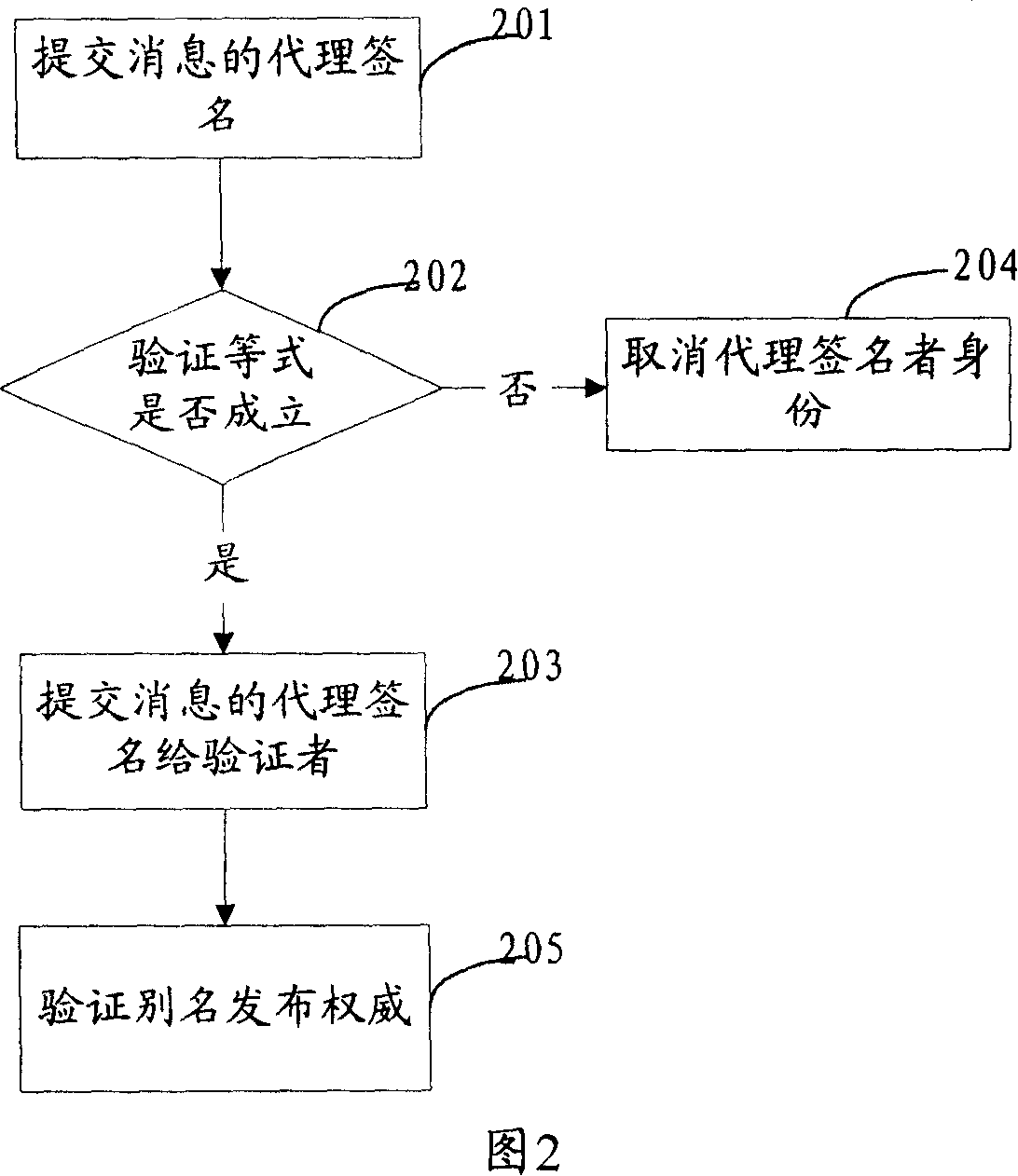
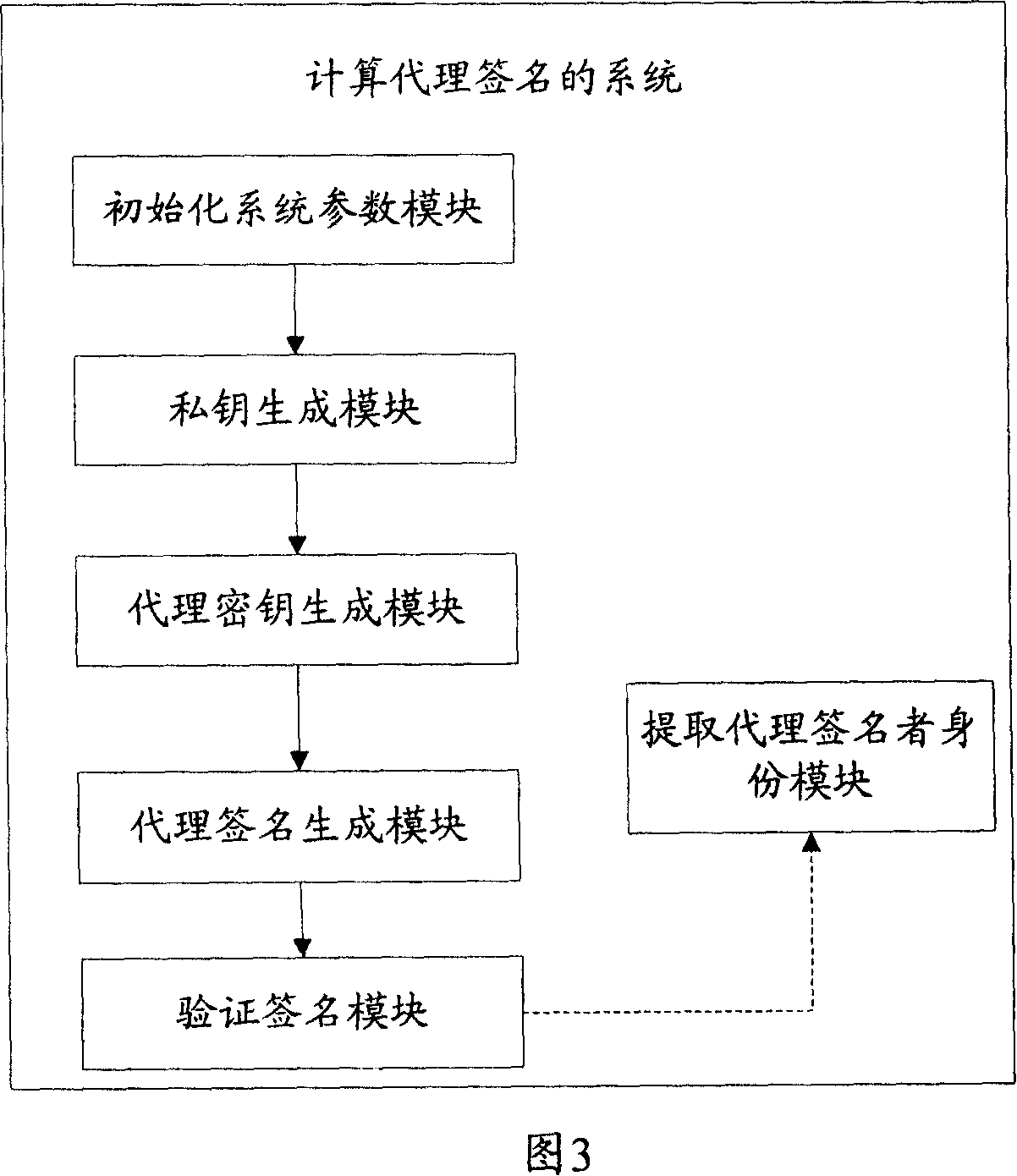
[0064] The present invention will be further described below with reference to the accompanying drawings and examples, but it is not intended to limit the present invention.
[0065] The invention proposes a proxy signature method and system. The method and system are identity-based proxy signatures without specifying a proxy signer, have the characteristic of recoverable messages, and use it to construct a mobile proxy scheme.
[0066] In the identity-based signature system, the signer first obtains the signature private key corresponding to his identity from a trusted third party, the private key generator PKG. Then the signer generates the signature with the signature private key. Any verifier only needs to use the identity of the signature generator as the user's public key to verify the correctness of the signature, and does not need to verify the validity of the public key certificate to check the correctness of the signature.
[0067] The scheme of the present inventio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More