Detecting probe interlock based network security event tracking system and method
A network security and probe technology, applied in the field of network information security, can solve problems such as unobtainable, affecting the success rate and efficiency of accurate traceability, and uncontrollable
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0075] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
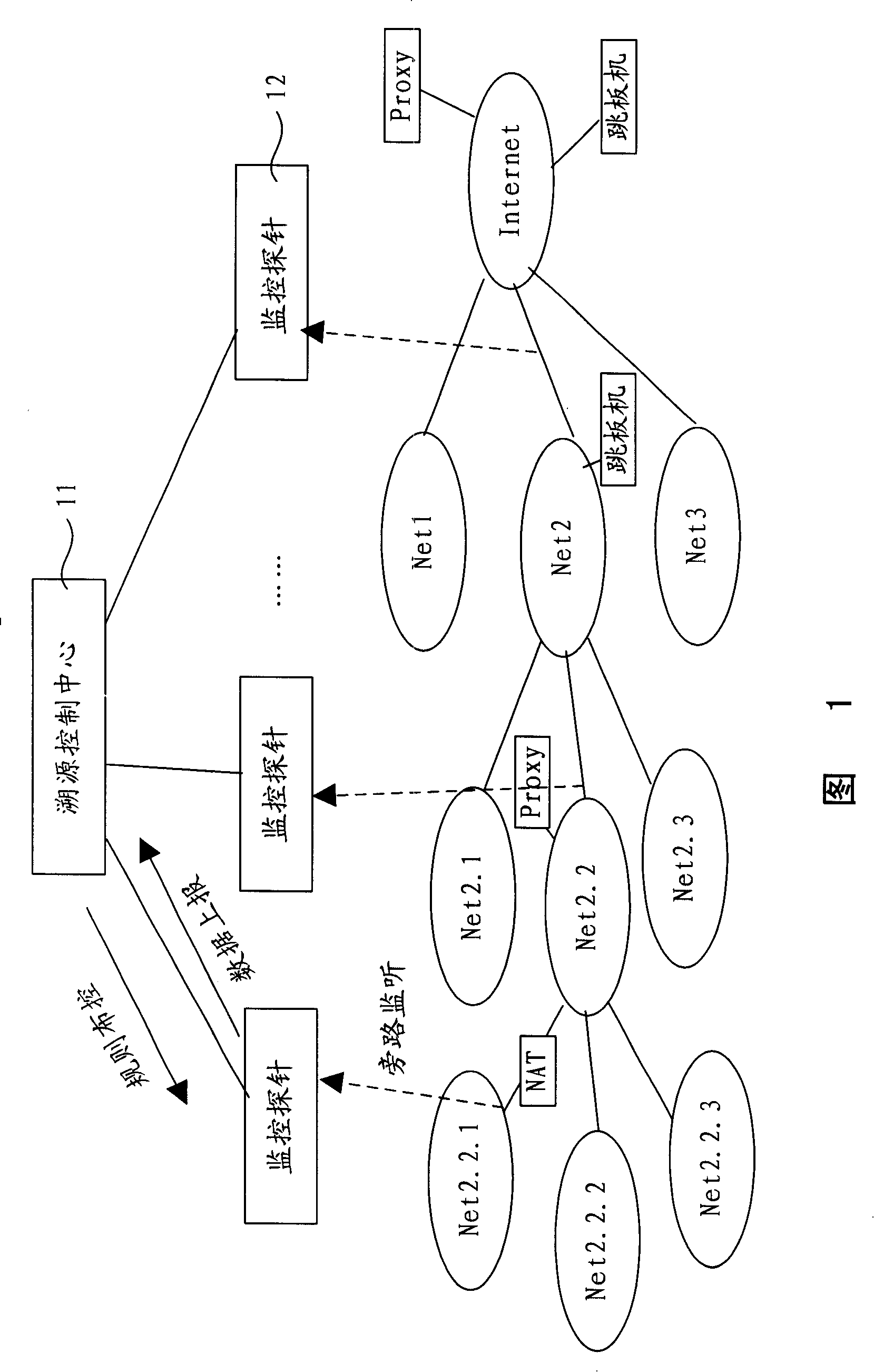
[0076] FIG. 1 shows the structure of the monitoring probe-based network security event tracing system of the present invention. Referring to Fig. 1, the system is made up of a traceability control center 11 and several monitoring probes 12, and the monitoring probes 12 are arranged on main network passages, such as being arranged at network exits including enterprise networks, NAT backend network passages, IDC ( Internet Data Center (Internet Data Center) network egress, provincial / city network egress and international egress, to monitor network data flow by way of bypass monitoring. When it is necessary to accurately locate a certain network security event, the traceability control center 11 formulates corresponding traceability rules based on the relevant information of the network security event and publishes them to the relevant monitoring probes 12...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More