A trusted network connection method based on three-element peer authentication
A ternary peer-to-peer and network connection technology, applied in the field of network security, can solve problems such as unequal AIK certificate validity and platform integrity evaluation, poor scalability, and inability to verify access requesters
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
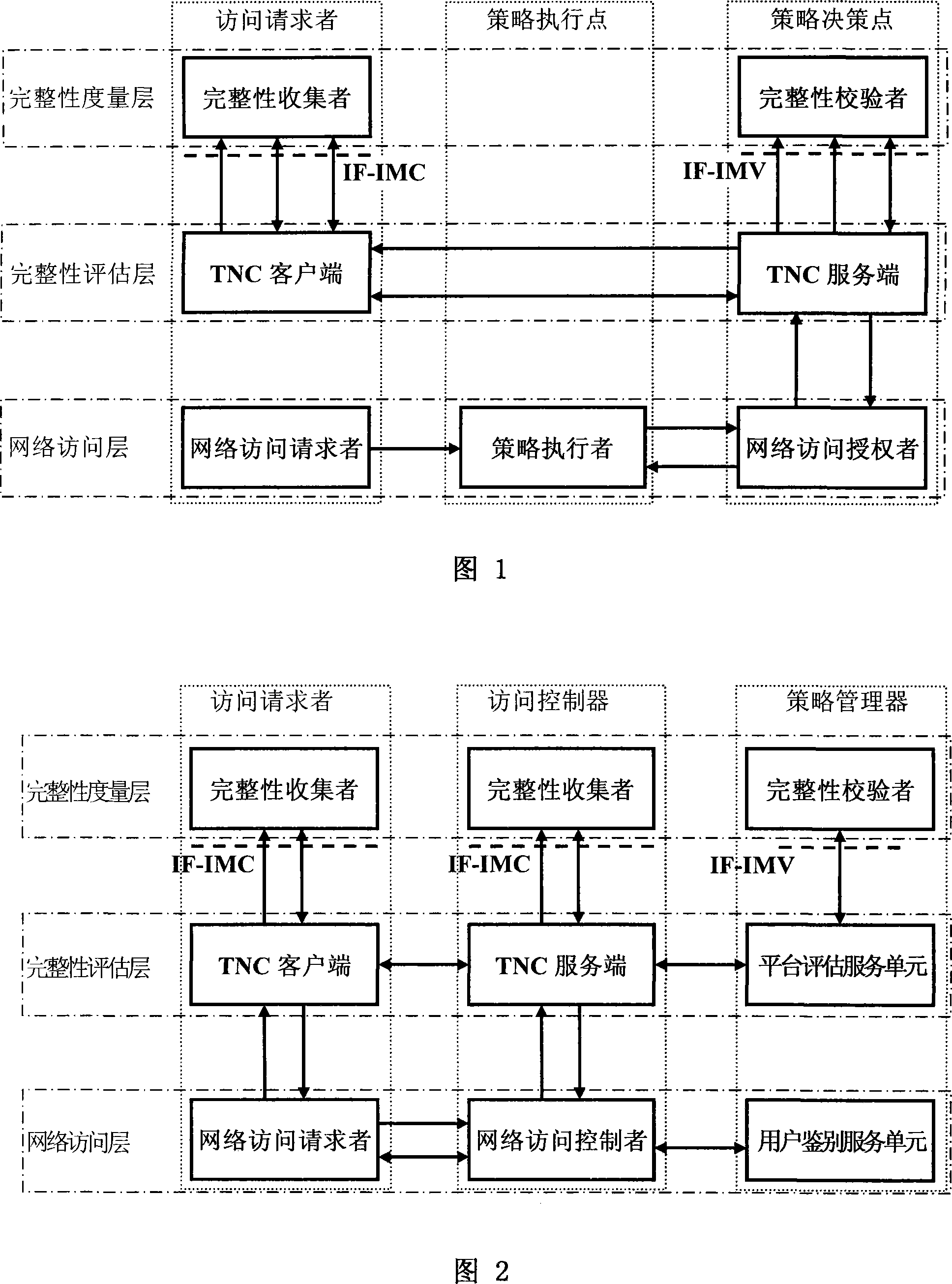
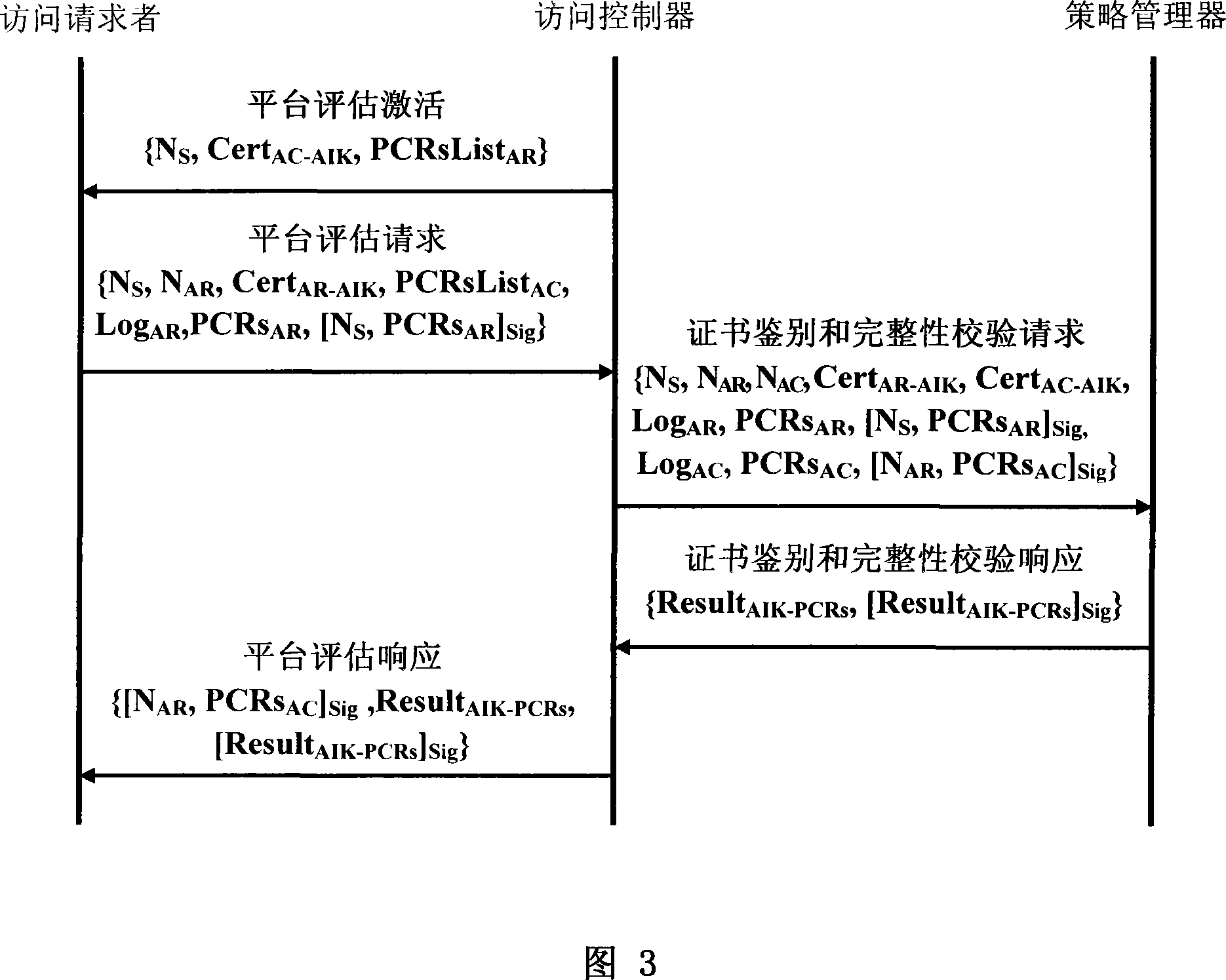
[0065] The present invention is mainly composed of network access layer, integrity evaluation layer and integrity measurement layer. Access requester, access controller and policy manager are three logical entities in the present invention, which can be distributed anywhere in the network. The access requester is also called requester, user station, etc.; the access controller is also called authentication access controller, base station, access service unit, etc.; the policy manager is also called authentication server, trusted server, background server, etc.
[0066] The network access layer is responsible for two-way user authentication and key negotiation between the access requester and the access controller, and mutual access control between the access requester and the access controller based on the network user authentication result and the platform integrity evaluation result. The network access layer can adopt an access control method based on ternary peer-to-peer au...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More