Authentication method and terminal for telecom smart card
A smart card and telecommunications technology, applied in the field of data security, can solve the problems of poor phone terminal security, theft of algorithms and keys, leakage of algorithms and keys, etc., to avoid the loss of call charges
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
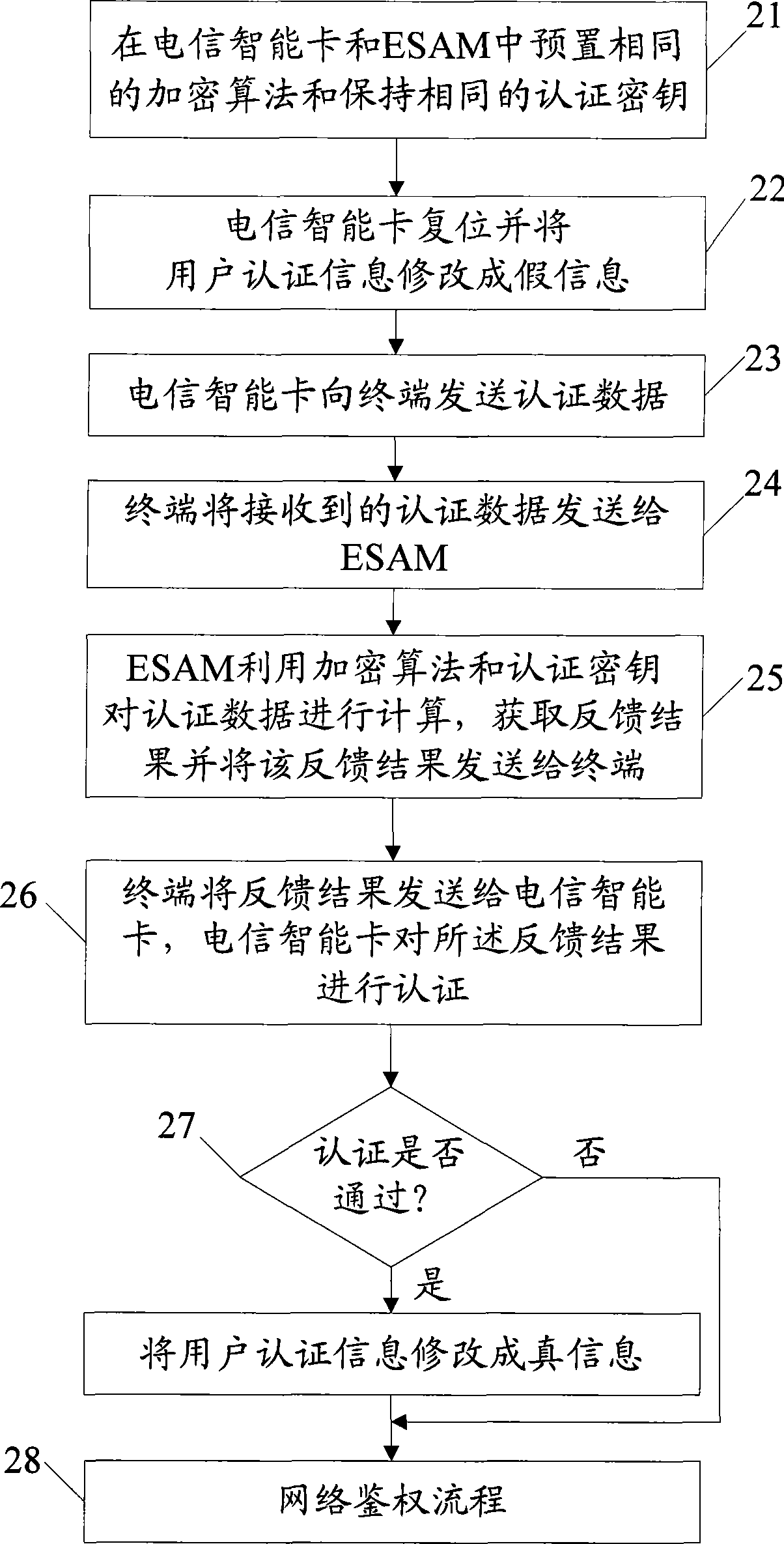
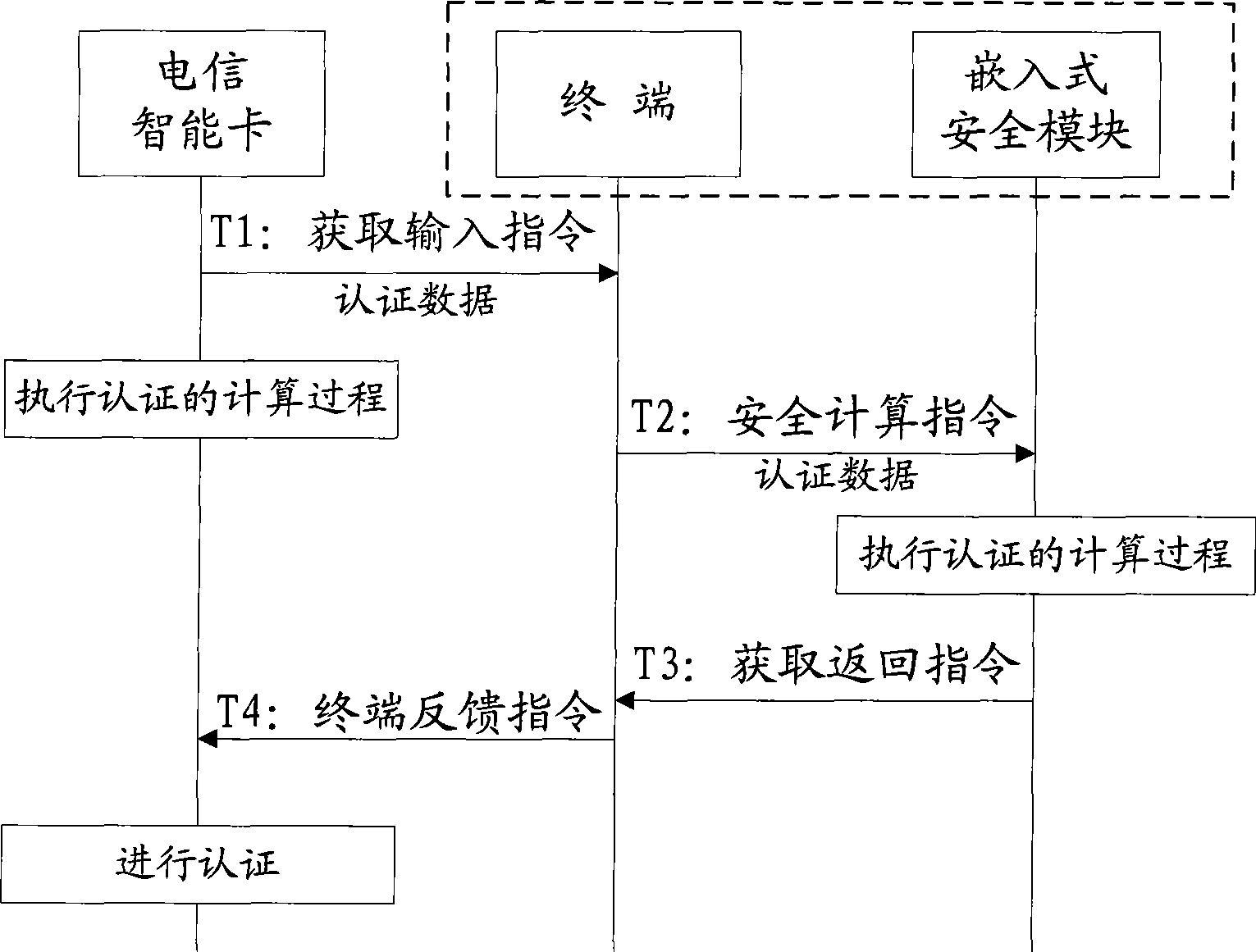
[0016] In order to illustrate the technical solutions of the embodiments of the present invention more clearly, the embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. The following descriptions are only some embodiments of the present invention. For those of ordinary skill in the art, Other implementations of the present invention can also be obtained according to these embodiments without any creative effort.
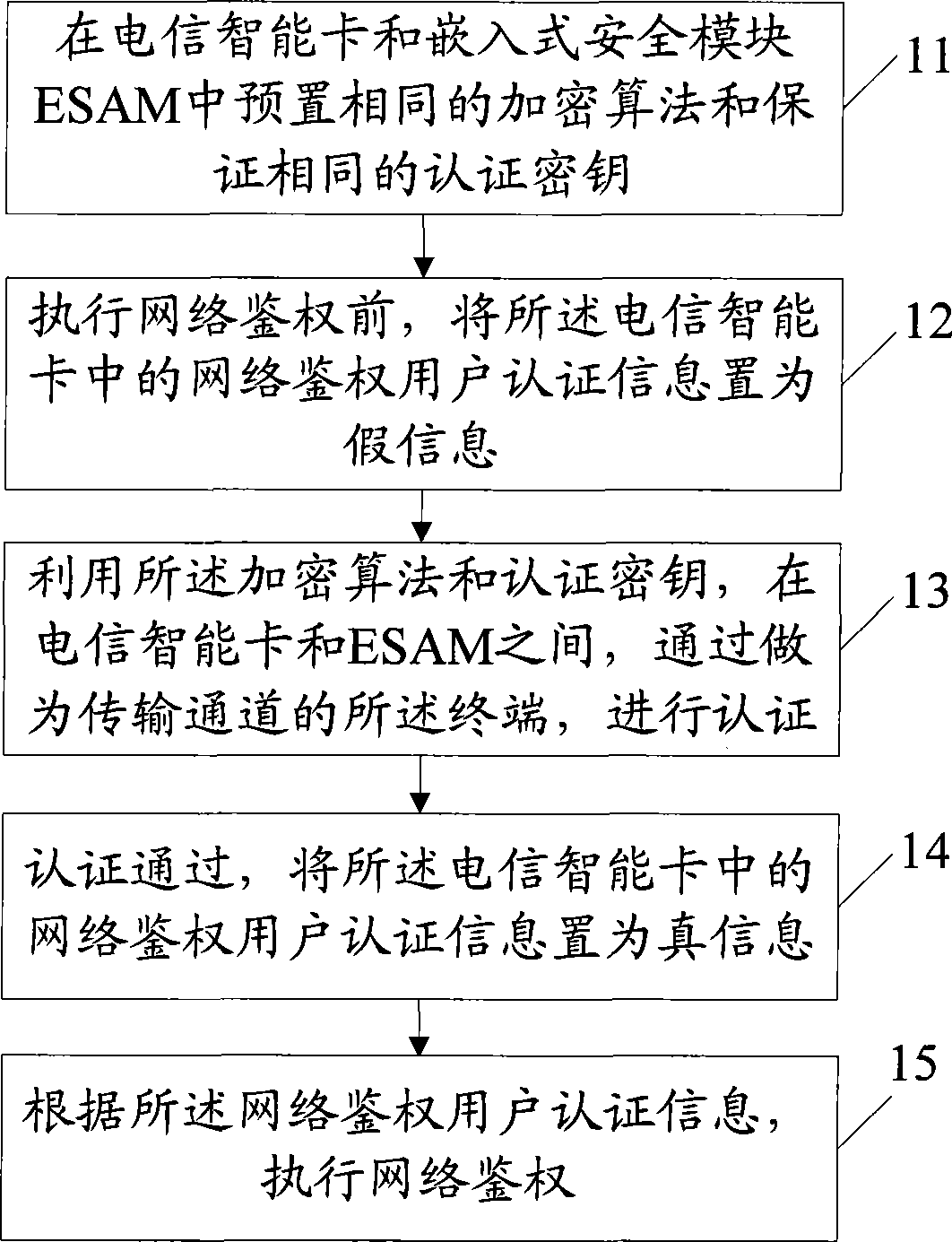
[0017] The authentication and authentication method of the telecom smart card provided by Embodiment 1 of the present invention, such as figure 1 As shown, the method includes:
[0018] Step 11: preset the same encryption algorithm and ensure the same authentication key in the telecommunications smart card and the embedded security module ESAM, and the embedded security module is located in the terminal;
[0019] Step 12: Before performing network authentication, set the network authentication user aut...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More