Method for enabling local security context
A local security and context technology, applied in the field of communication, can solve the problems of communication process delay, reduce system performance, etc., and achieve the effects of reducing signaling load, optimizing benefits, and reducing communication delay
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] The preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
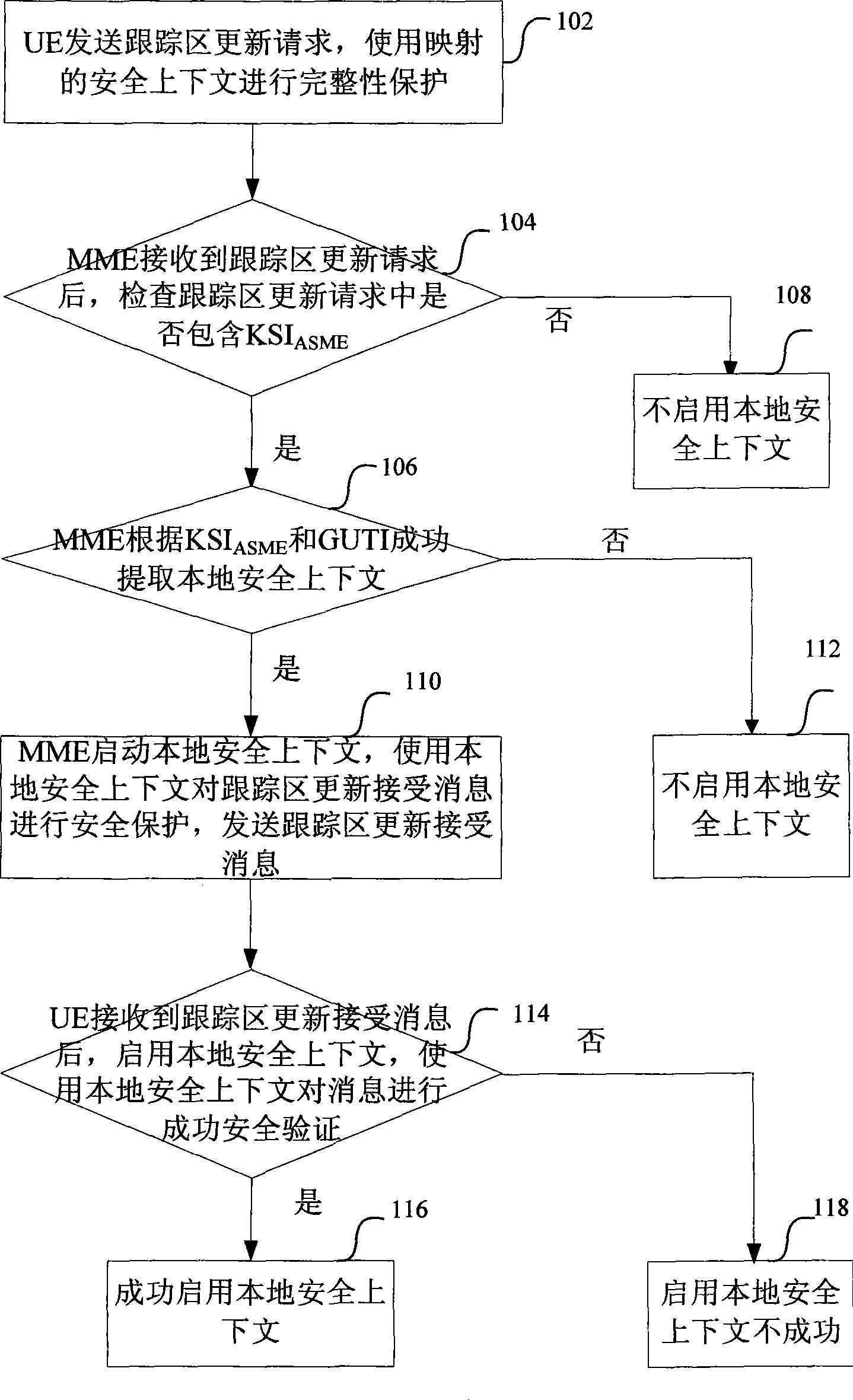
[0030] figure 1 The flow chart of enabling the local security context after switching between systems for the present invention includes:
[0031] Step 102, the UE sends a tracking area update request message to the MME, and uses the mapped security context to protect the integrity of the message. If the UE has a local security context, the message contains the KSI corresponding to the local security context ASME (Key Set Identifier of Access Security Management Entity, access security management entity key identifier).
[0032]The message also carries the UE's GUTI (Globally Unique Temporary Identity, Globally Unique Temporary Identity), GUTI is the UE's unique t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More