A database data encryption system and method
A data encryption and database technology, which is applied in the field of information security, can solve the problems of invisible binary data and achieve the effect of protecting security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
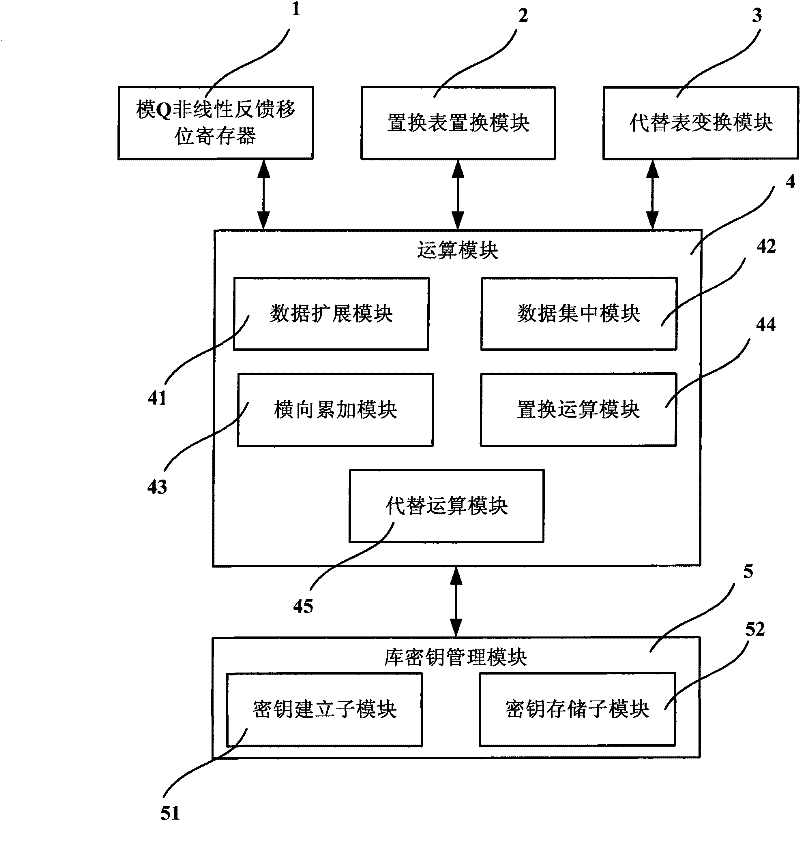
Method used
Image
Examples
Embodiment 1
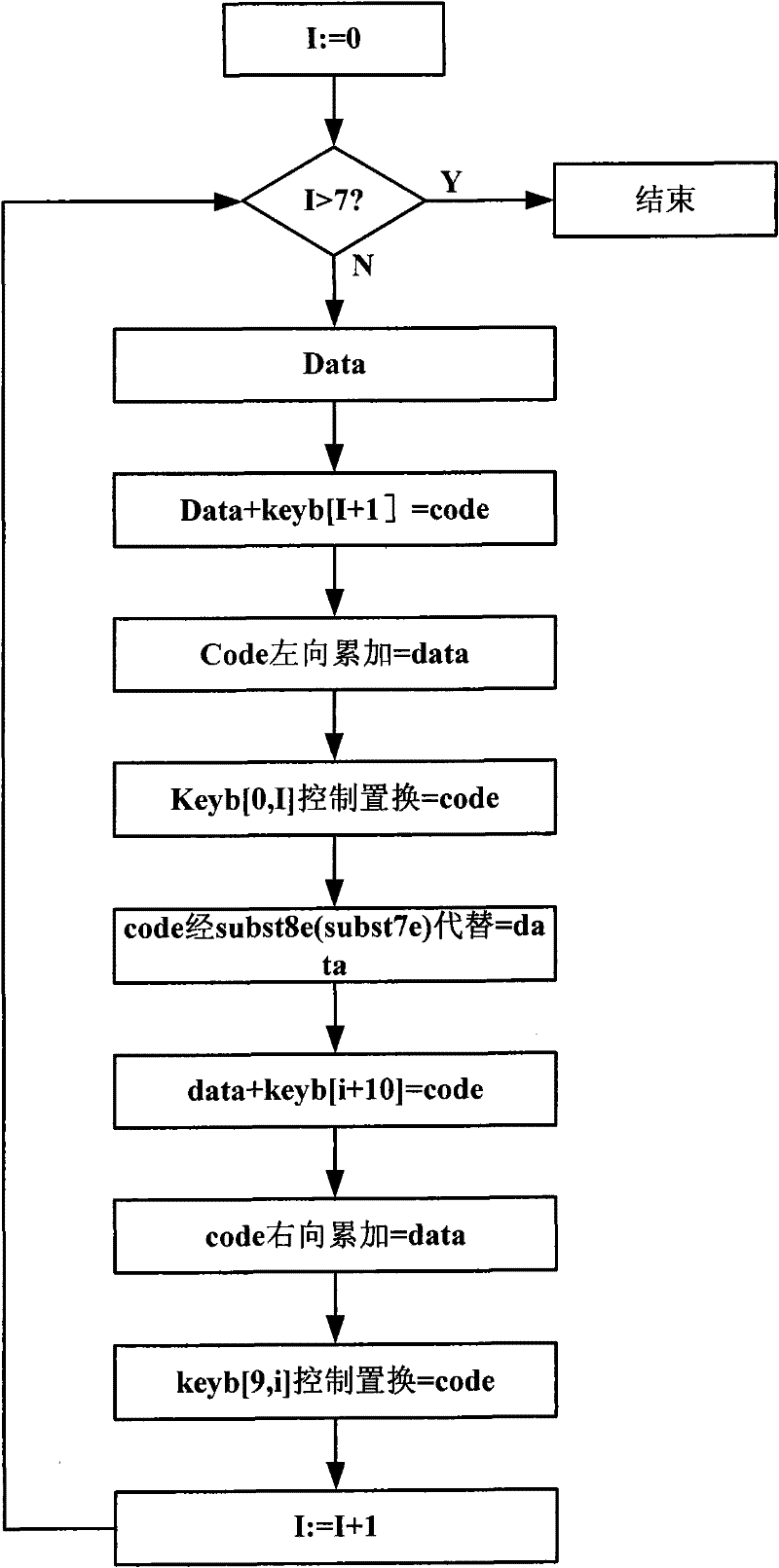
[0251] Embodiment 1: 8-bit unit code operation, 8-bit binary data is obtained after encryption
[0252] Given a key and data as follows:
[0253] Byte order [7][6][5][4][3][2][1][0]
[0254] Key variable key: 08 07 06 05 04 03 02 01
[0255] Given data:
[0256] Data length Data variable data
[0257] byte=1 01
[0258] byte=2 02 01
[0259] byte=3 03 02 01
[0260] byte=4 04 03 02 01
[0261] byte=8 08 07 06 05 04 03 02 01
[0262] in
[0263] byte: field length, byte=1, 2, 3, 4, 8 five kinds
[0264] i: operation of the i-th circle
[0265] key: given key variable
[0266] data: plaintext data to be encrypted
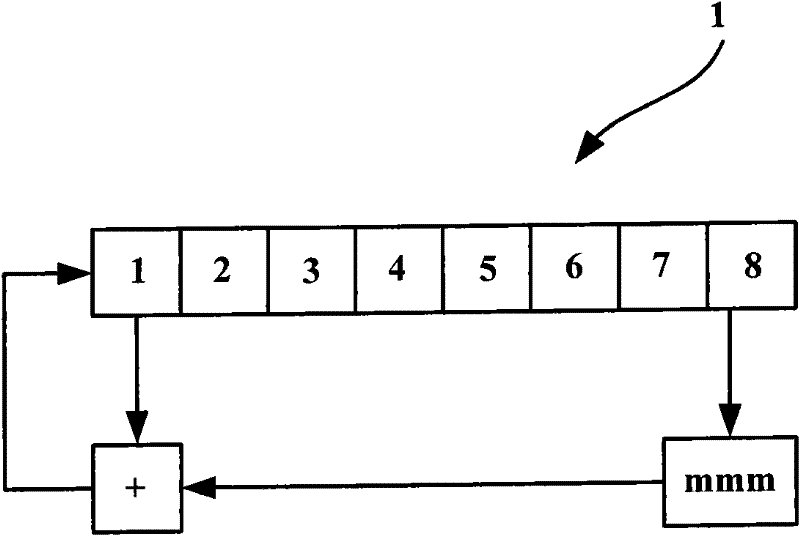
[0267] Step S11, from the given key key, use the modulo Q nonlinear feedback shift register 1 to perform feedback operation to obtain 18 groups of derived keys keyb;
[0268] [7][6][5][4][3][2][1][0]
[0269] Set the given key key: 08 07 06 05 04 03 02 01
[0270] Then derive the key keyb[0]: 4C A4 7F 5D 08 18 94 B7
[0271] [1]; 92 5F 60 D6 DC 38 9...
Embodiment 2
[0511] 8byte: 7 units 13 61 63 5A 61 3E 1C 6A are still expanded according to 7bit
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More