Method for analyzing characteristic of software vulnerability sequence based on cluster
A software vulnerability and sequence technology, applied in the field of information security, can solve the problems of difficulty in feature analysis, low efficiency of feature analysis of suspected vulnerability sequences, and cluster analysis of software vulnerability sequences.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0056] The technical solutions of the present invention will be described in detail below in conjunction with specific embodiments.
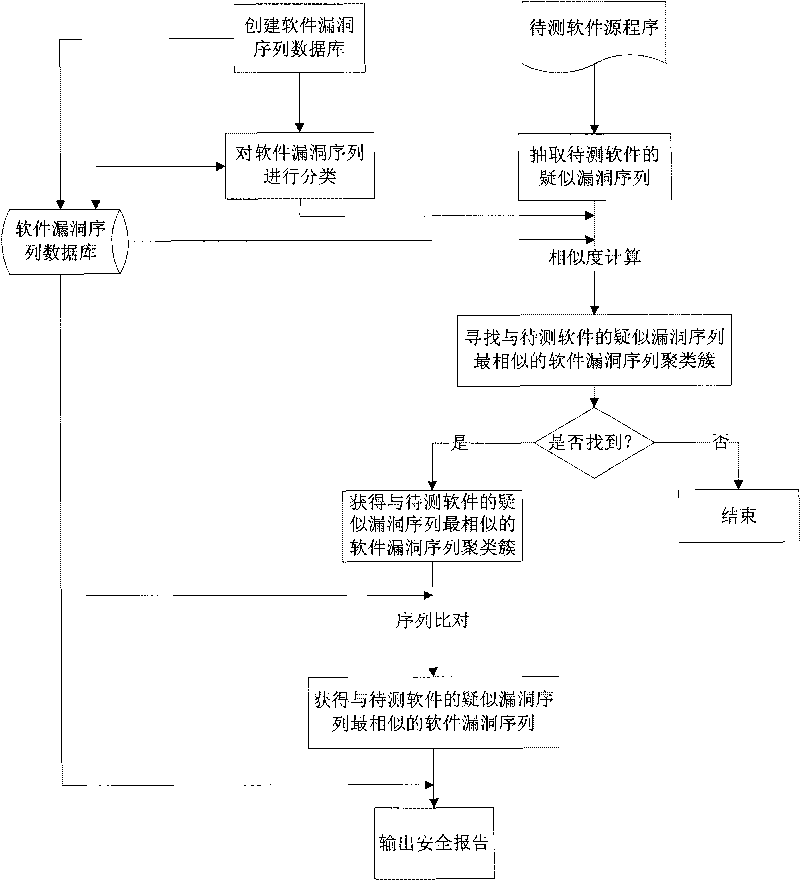
[0057] A schematic flow chart of a method for analyzing the sequence characteristics of software vulnerabilities based on clustering in the present invention is as follows: figure 1 As shown, the specific operation steps are as follows:
[0058] Step 1. Using the existing software vulnerability sequence data, create a software vulnerability sequence database, as shown in Table 1.
[0059] Table 1 Software Vulnerability Sequence Database
[0060] SID
S i
INF
CID
1
S 1 =ACBAA
sync error
C 1
2
S 2 =ABA
Installation parameter error
C 2
3
S 3 BCACCB
Boundary condition error
C 3
[0061] SID
S i
INF
CID
4
S 4 =CBCBCC
Access verification error
C 3
5
S 5 =CABCBCCB
source validation erro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More