Method for protecting private data in association rule mining
A technology of privacy data and rules, applied in digital data protection, electronic digital data processing, special data processing applications, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
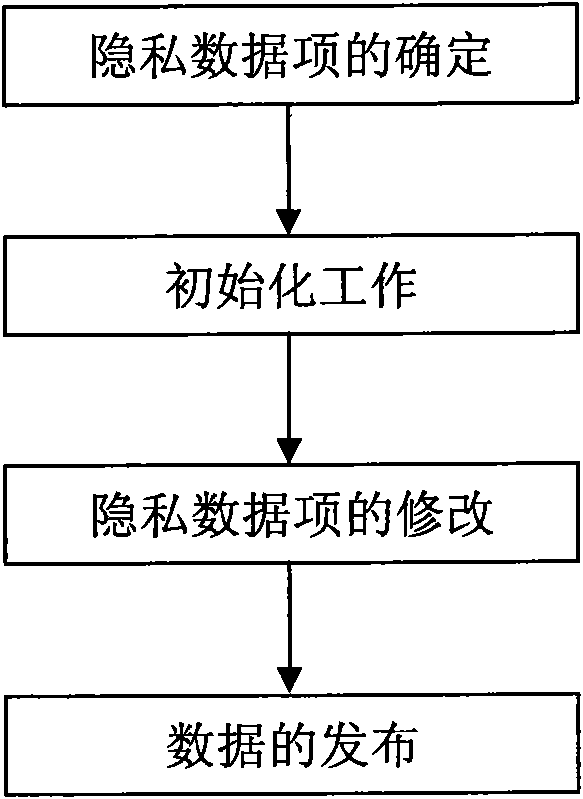
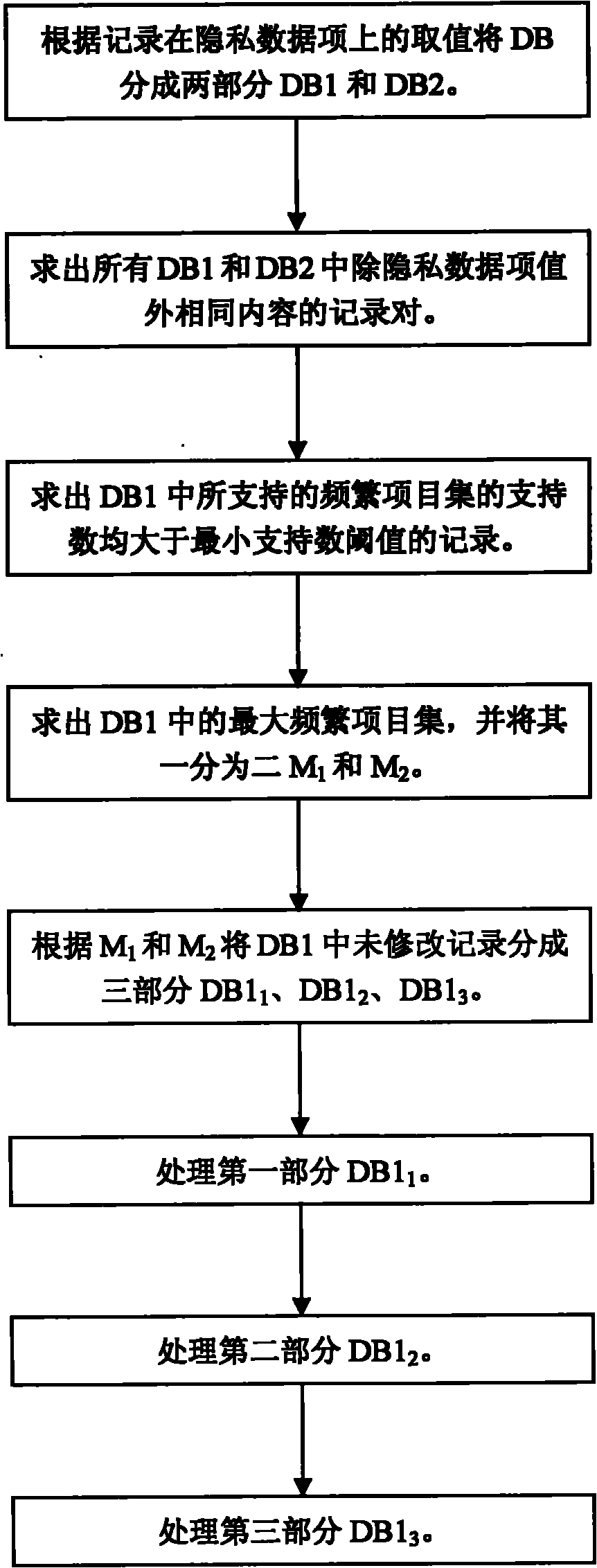
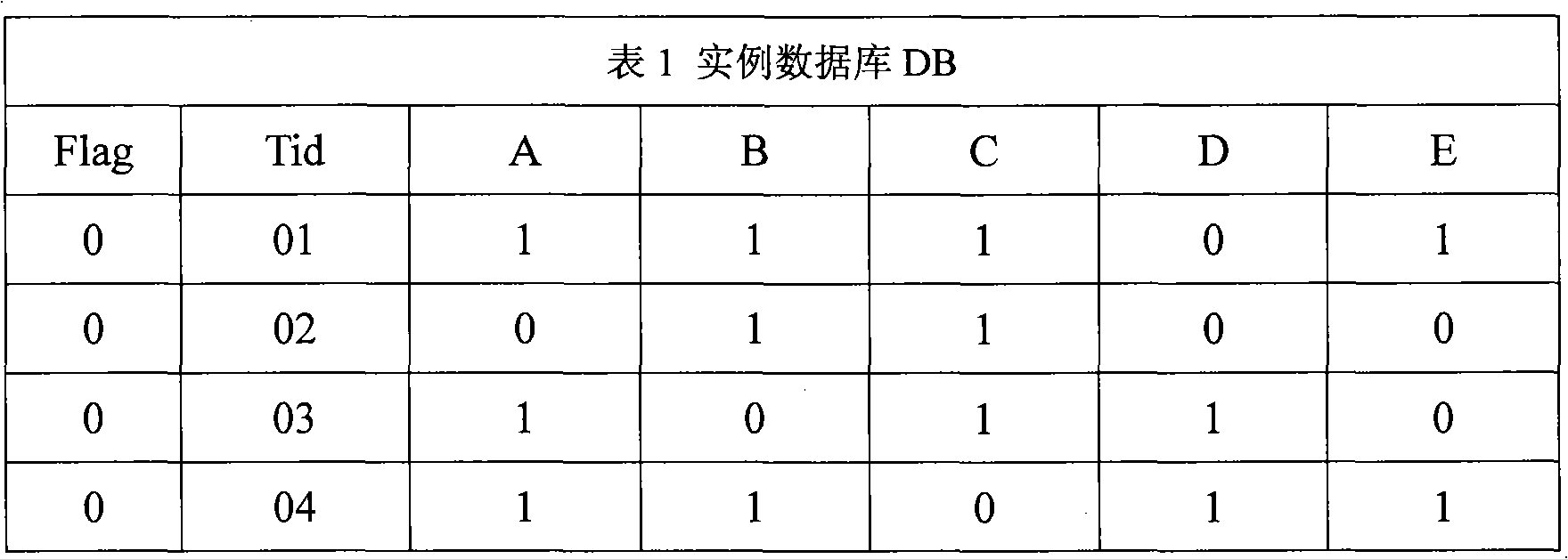
[0060] The following takes the relational database DB shown in Table 1 as an example, combining figure 1 , figure 2 The flow chart of the figure simply illustrates the implementation of the present invention. Table 1 sets five fields in total, which are respectively marked as A, B, C, D and E. Assume that the data item to be protected in this example is E, the minimum support threshold is 25% or the minimum support number threshold is 2, and the modification rate XP is 50%, that is, the E values of at least four records need to be modified.
[0061]
[0062]
[0063] The specific execution steps are as follows:
[0064] (1) Initialize the record modification number variable JXC, JXC=XP×|DB|=4, where |DB| is the number of records in the instance database DB.
[0065] (2) Set the modification flag, flag[i]=0, i=1, 2, 3, 4, 5, 6, 7, 8, namely the first column of Table 1.
[0066] (3) Scan the instance database DB once to obtain frequent 1-itemsets {{A}, {B}, {C}, {D}...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More