Method and system for spreading pseudowire routing and sink node equipment
A diffusion method and a technology of convergence nodes, applied in the field of communication, can solve the problems of increasing the complexity of access equipment and increasing the burden of access equipment, and achieve the effect of reducing complexity
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
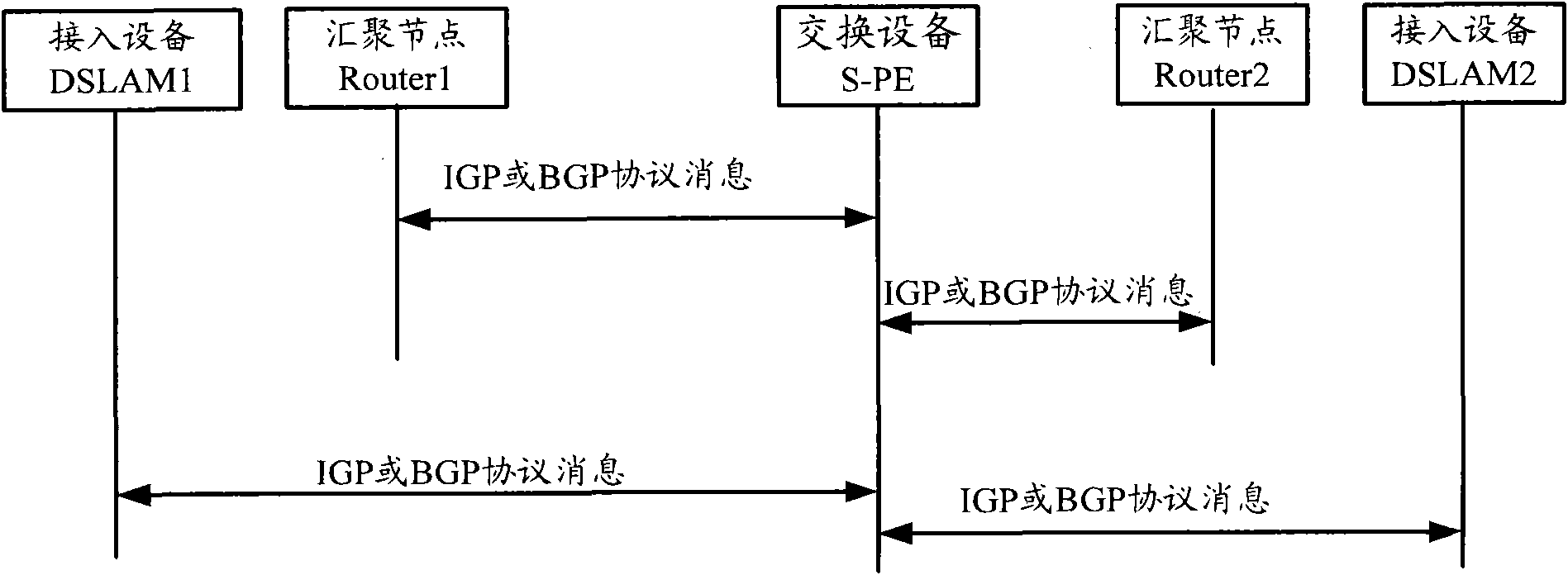
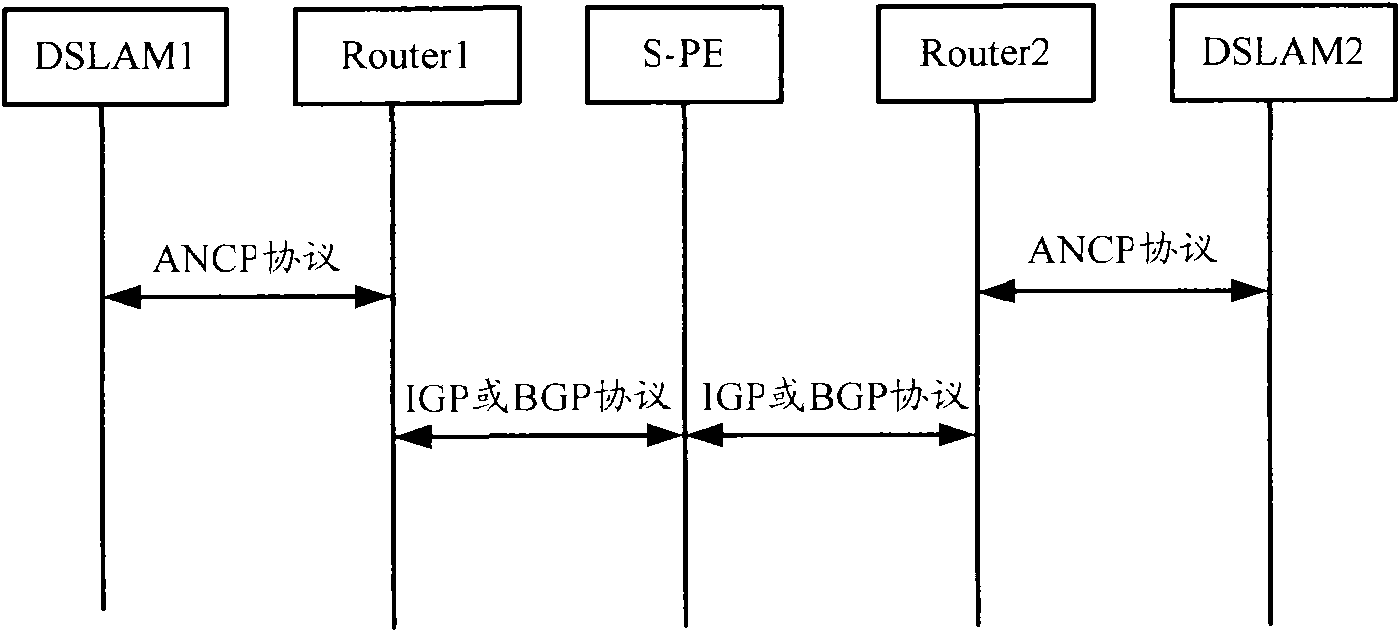
[0038] See figure 2 , from the access device DSLAM1 to the aggregation node Router1, and from the access device DSLAM2 to the aggregation node Router2 are generally referred to as the access section, and non-routing protocols can be used to transmit messages on the access section, for example, in the unique Distributes PW routes using a specific configuration protocol, which can simplify the complexity and burden of access devices.
[0039] For example, the access device DSLAM1 and the access device DSLAM2 can adopt specific configuration protocols such as Access Node Control Protocol (Access Node Control Protocol, ANCP) or Ethernet Operation, Administration and Maintenance (Ethernet Operation, Administration and Maintenance, ETH The OAM protocol is used to realize the PW path of the diffuse access device. Usually, the ANCP protocol is used for Digital Subscriber Line (Digital Subscriber Line, DSL) or Ethernet access scenarios; the Eth OAM protocol is used for Gigabit-bit pas...
Embodiment 2
[0052] see Figure 4 , is a flow chart of the pseudowire routing diffusion method according to the second embodiment of the present invention. In this embodiment, a specially configured non-routing protocol such as the ANCP protocol or the ETH OAM protocol is used to implement PW routing of the flooded access device (such as a DSLAM). Schematic diagram of PW routing extension in this embodiment and figure 2 same. Generally, the ANCP protocol is used in DSL or Ethernet access scenarios, and the Eth OAM protocol is used in GPON access scenarios, but other situations are not excluded. For example, ETH OAM protocol is used in DSL or Ethernet or EPON access scenarios.
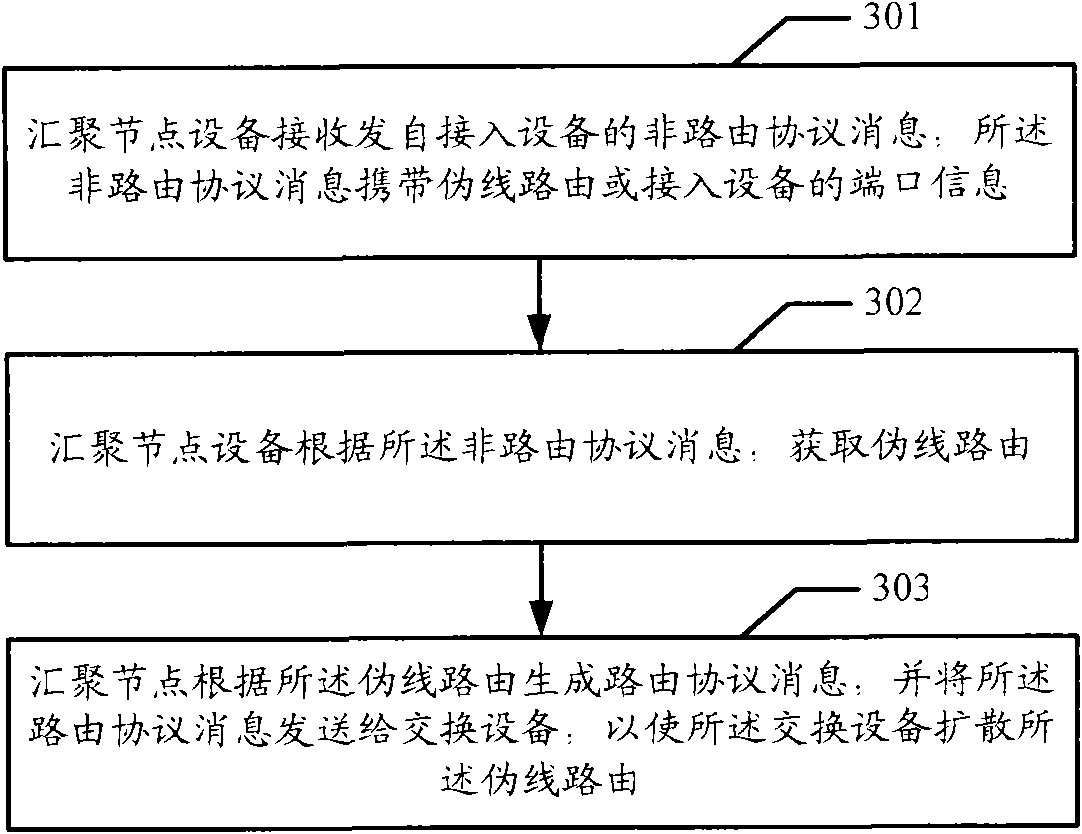
[0053] Wherein, the specific steps of the pseudowire routing diffusion method are:
[0054] In step 401, the access device DSLAM1 enables the PW routing function, and encapsulates the GlobalID, Prefix and AC ID of the access device DSLAM1 into AII information, that is, into PW routing.
[0055] In step 402, the...
Embodiment 3
[0074] In the second embodiment, the PW route of the access device needs to be maintained and released by the access device. For example, the PW route of the DSLAM11 needs to be maintained and released by the DSLAM11 itself, and a PW routing table is maintained in the DSLAM1. In this embodiment, the PW routing of the access device is maintained by the aggregation node as an agent, and between the aggregation node and the access device, an existing configuration protocol (such as ANCP protocol or ETH OAM protocol) is used to control the aggregation node to access Maintain the PW route of the device.
[0075] In this example, the aggregation node Router1 maintains the PW route of DSLAM1, and also maintains the PW route of Router1. Next, the ANCP protocol or the ETH OAM protocol is used to realize the PW routing of the diffuse DSLAM1. Generally, the ANCP protocol is used in DSL or Ethernet access scenarios, and the Eth OAM protocol is used in EPON access scenarios, but other sit...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com