Using social information for authenticating a user session
A social network and social networking technology, applied in digital data authentication, instruments, computing, etc., can solve problems such as failure of CAPTCHA mechanism and failure of behavior
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
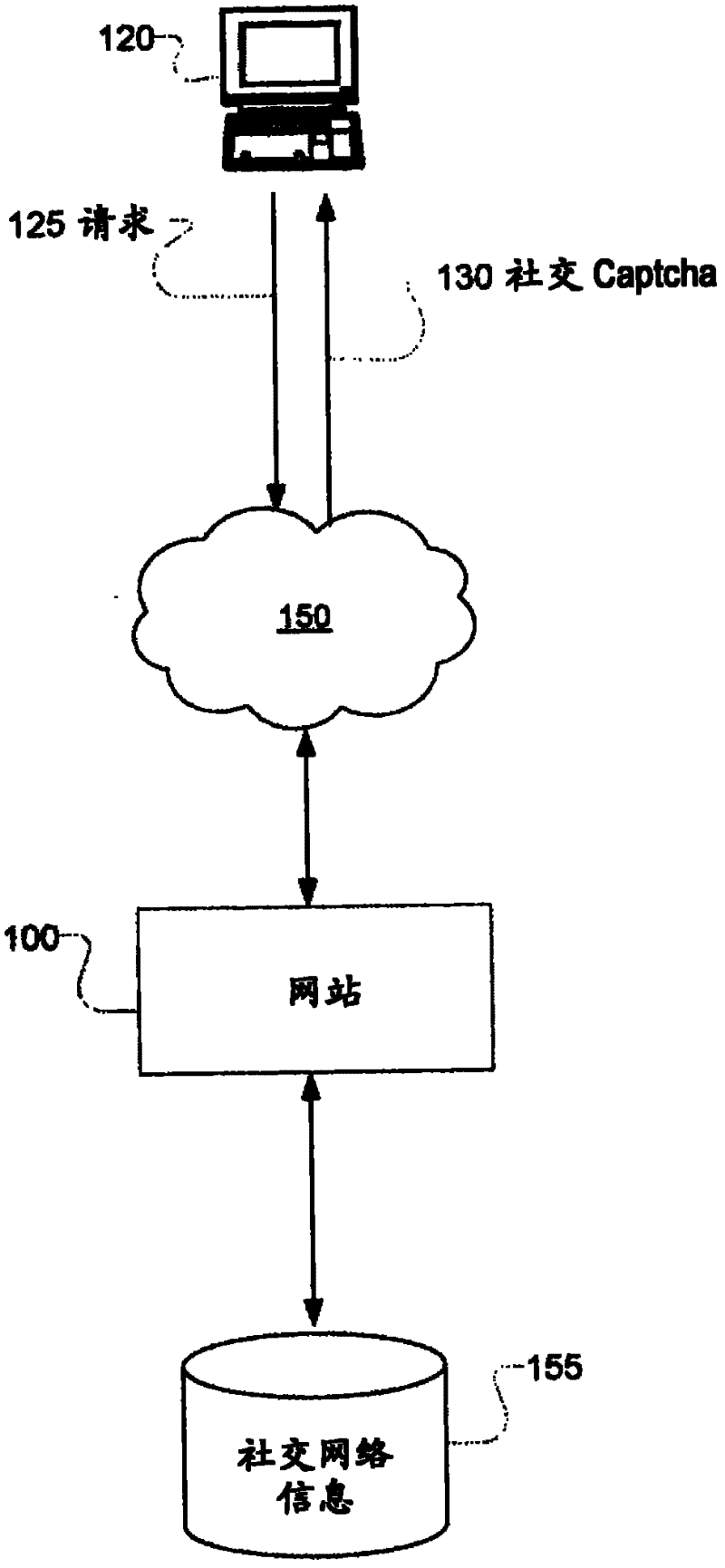
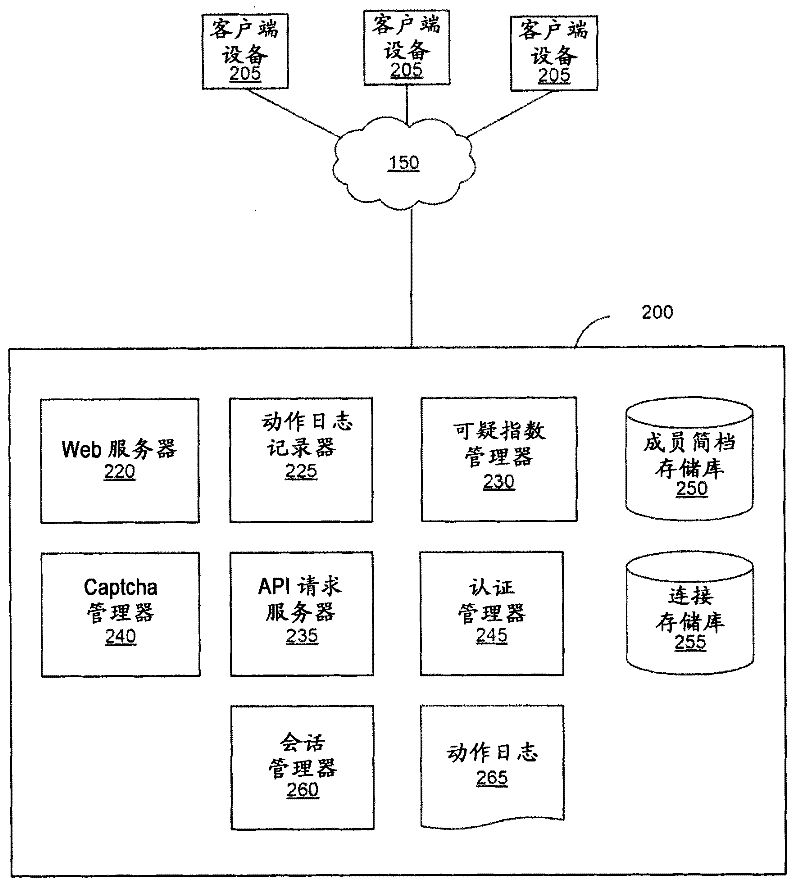
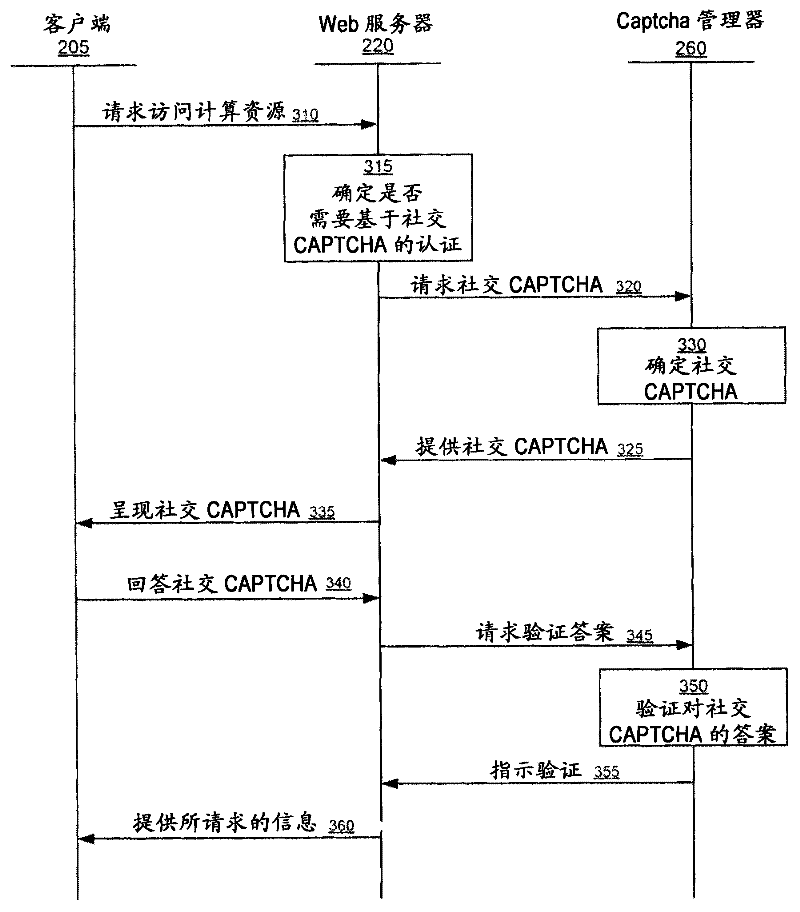
[0012] CAPTCHAs based on distorted character recognition or common sense questions can be cracked by using human power. However, CAPTCHAs based on questions that require only a specific user to possibly know cannot be cracked by using human power. For example, a question requesting information associated with a user's close friends cannot be answered by anyone unfamiliar with the user. A CAPTCHA based on information about the user's social circle and the user's social interactions is called a social CAPTCHA. These questions ask for information that can be obtained in social networks.
[0013] A social network gives its members the ability to communicate and interact with other members of the social network. In use, members join a social network and then add connections to a number of other members with whom they desire to connect. As used herein, the term "friend" refers to any other member with whom a member forms a connection, association or relationship via a social netw...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More