Method for protecting security of visualized information system
A security protection and information system technology, applied in the field of security protection for visual information systems, can solve problems that cannot be fully applied to visual information systems, and achieve the effects of reliable data storage and application, safe collection, and perfect security systems
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0051] Below in conjunction with accompanying drawing, the present invention is described in further detail:
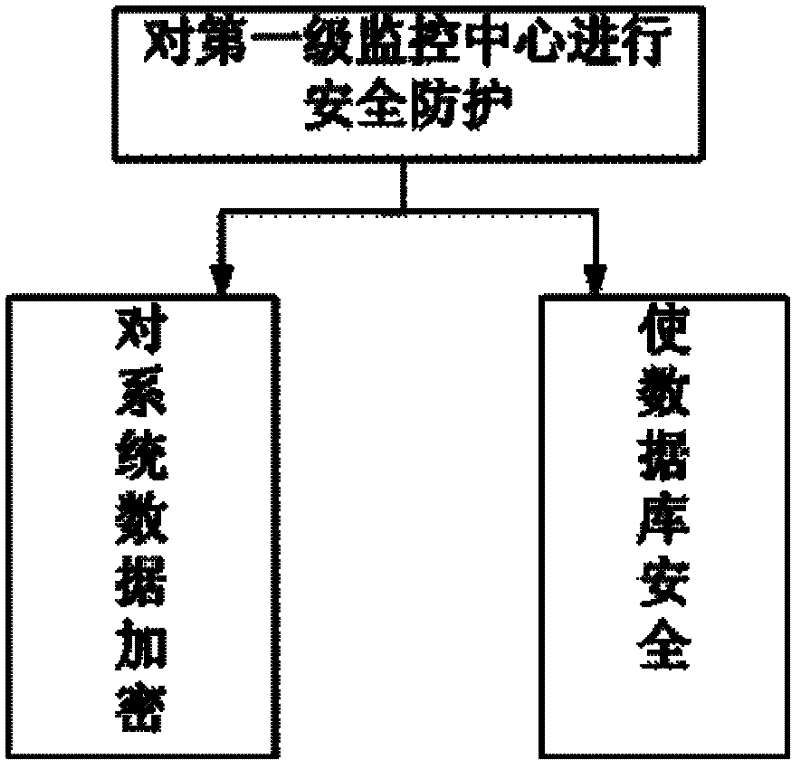
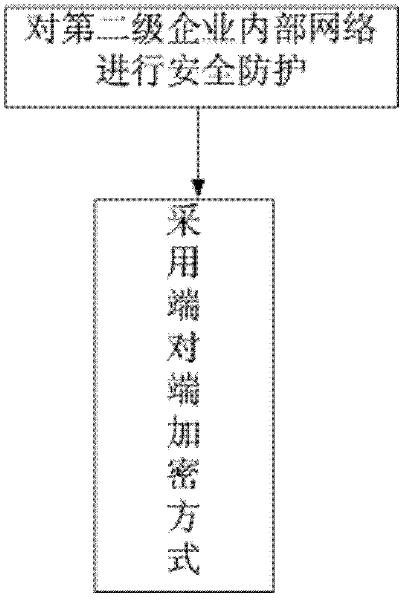
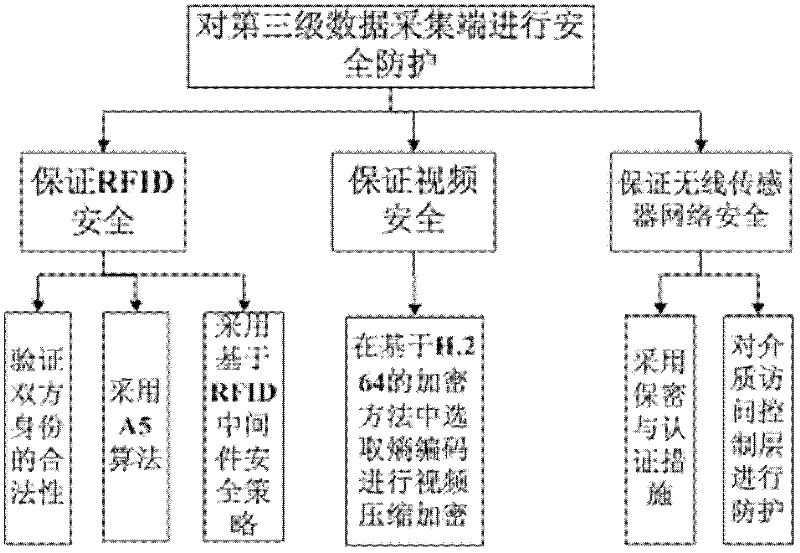
[0052] A method for security protection of a visual information system, which includes security protection for a first-level monitoring center (the third-party government monitoring center is the first-level monitoring center), and second-level enterprise internal network (it specifically refers to the cold monitoring center). The internal network management system of each enterprise in the chain process) for security protection and for the third-level data collection end (referring to the data collection end of video data, temperature and humidity data, and item RFID data information); in the design of the visual information system , full consideration has been given to the high reliability, availability, performance and interconnection of the system. The present invention is a safety guarantee system capable of effectively guaranteeing terminal safety, communication...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More