Website data tampering preventing method based on network isolation structure
A technology for network isolation and network data, which is applied in the field of information security and can solve problems such as the inability of tamper-proof systems to protect data
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
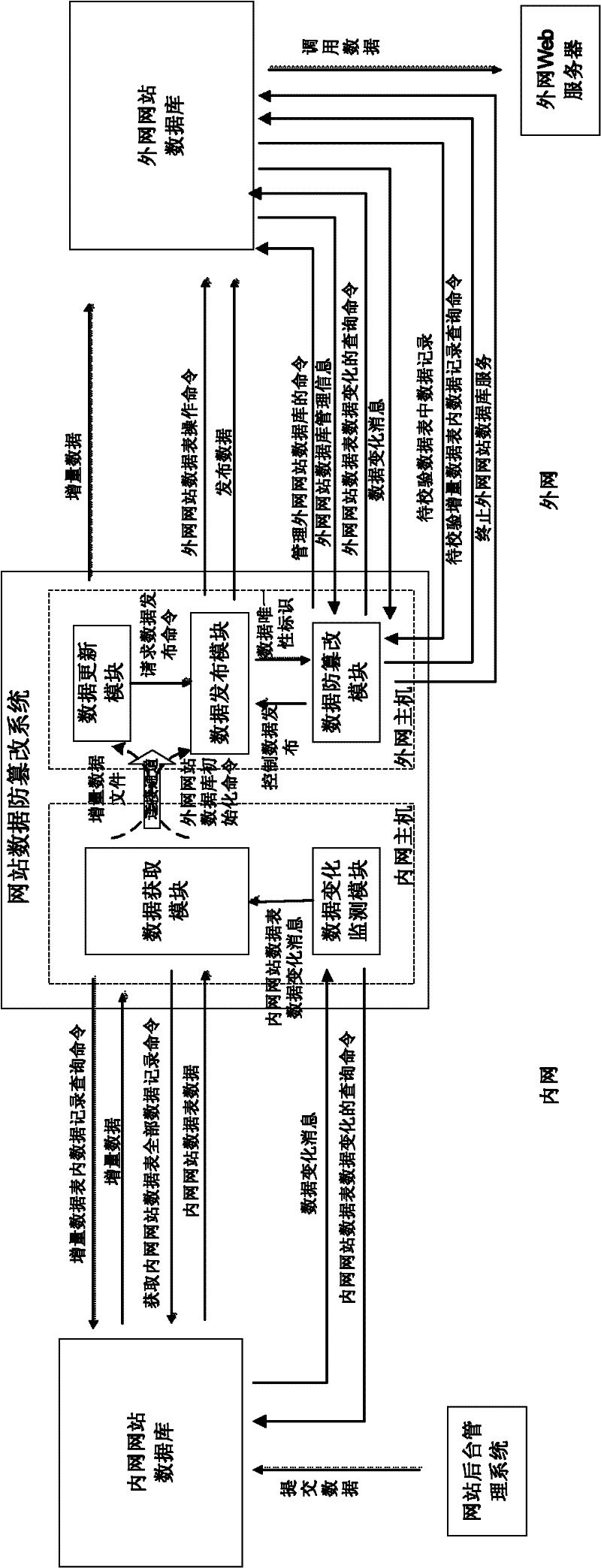
[0088] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
[0089] The physical composition of the website data anti-tampering system can adopt dual-host or single-host architecture:
[0090] ●In the dual-host architecture, the website data anti-tampering system is composed of two independent hosts connected to the internal and external website databases and communication components connected to the two hosts. The communication components can use network cards or special one-way isolation components;
[0091] ●In the single-host architecture, the framework structure described above is realized through the division of modules inside the system and the communication mechanism between modules.
[0092] An application framework for applying this technical solution is as attached figure 1 as shown,
[0093] These include the anti-tampering system for website data, databases for internal and external websites, backgro...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More