Implementation method and system for resisting quantum computation attack based on CPK public key system
A technology of quantum computing and public key system, which is applied in the field of cryptography and computer, and can solve problems affecting the life of the public key system
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
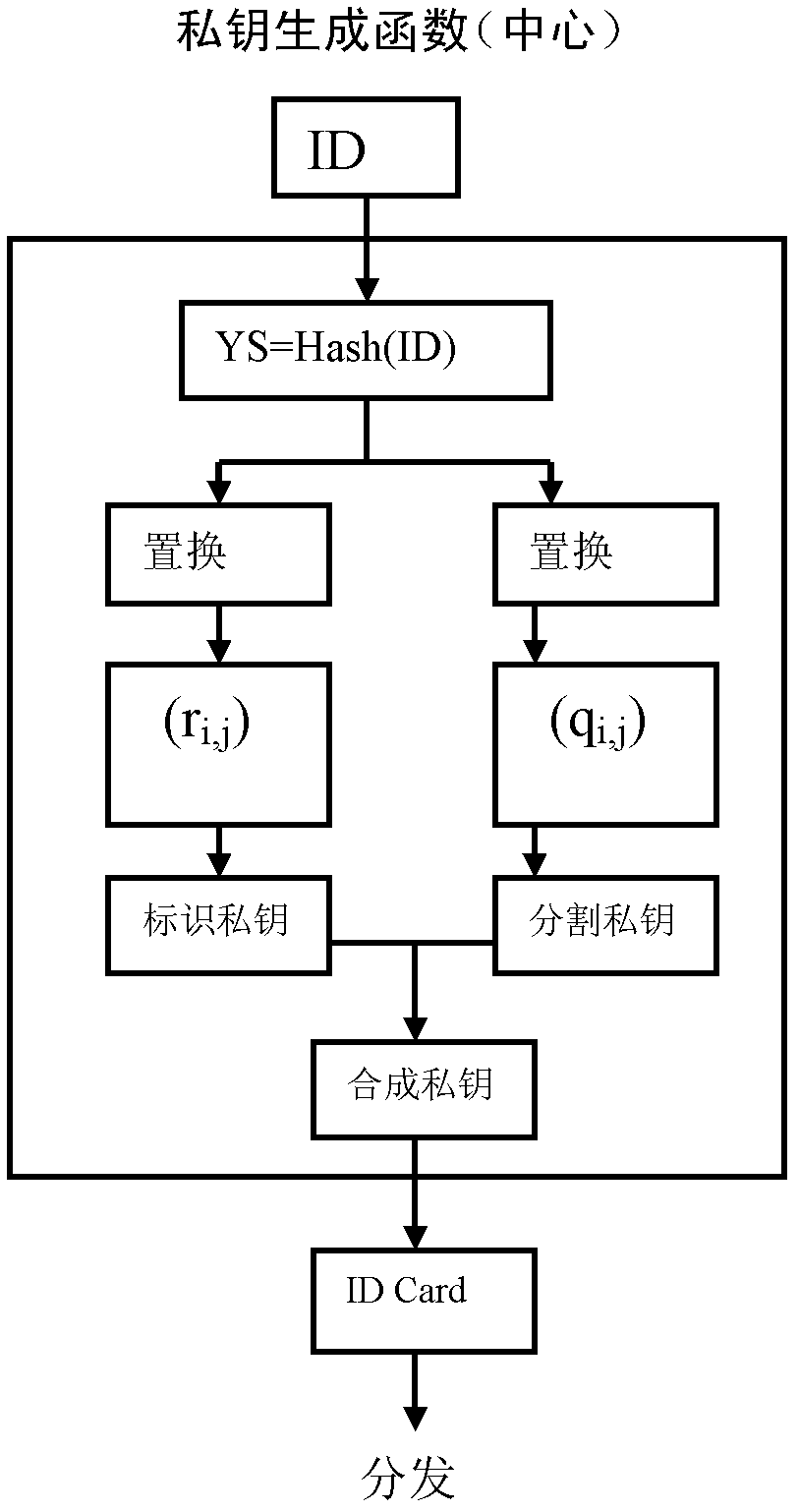
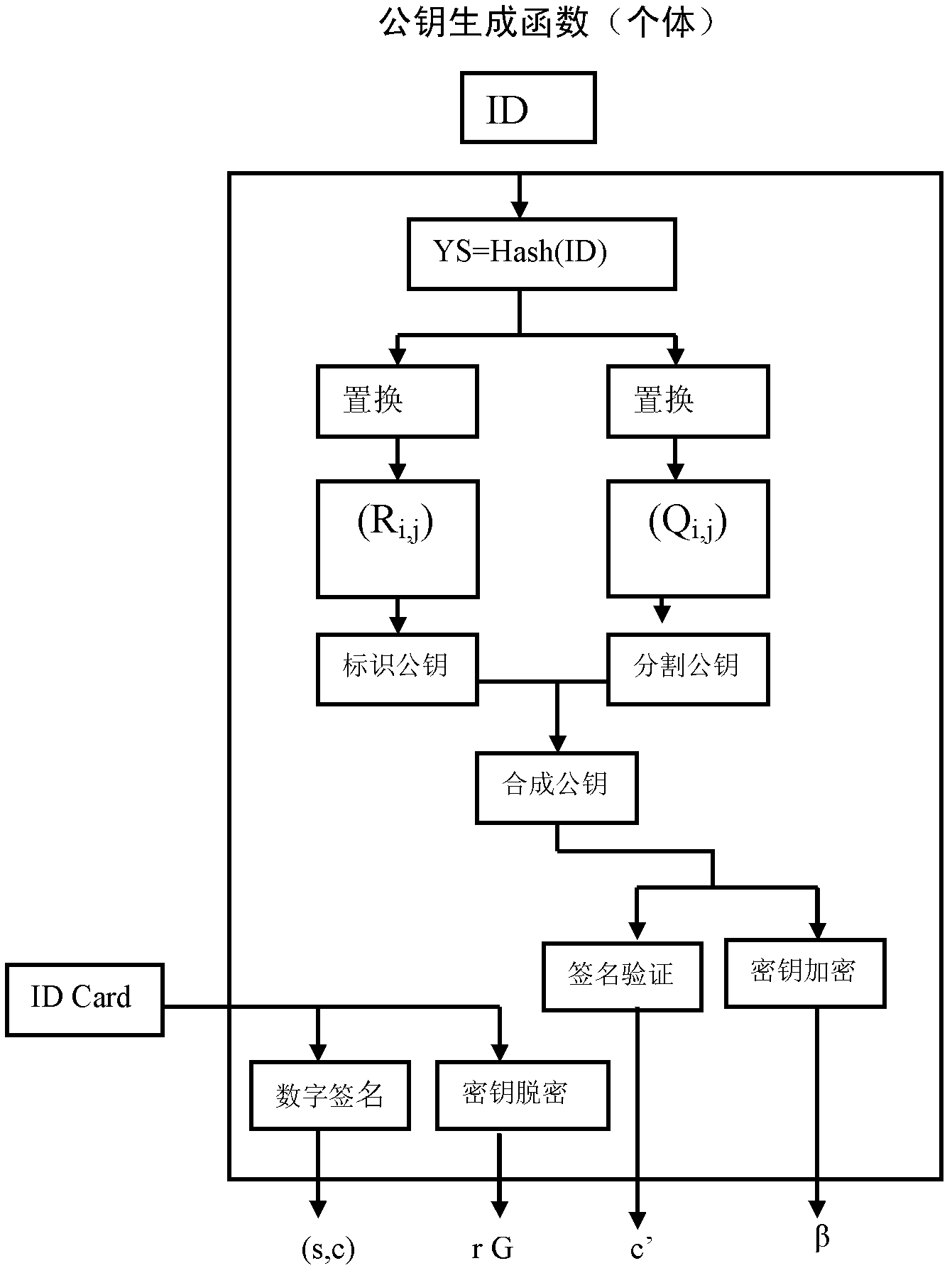
[0134] The preferred embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings; it should be understood that the preferred embodiments are only for illustrating the present invention, rather than limiting the protection scope of the present invention.
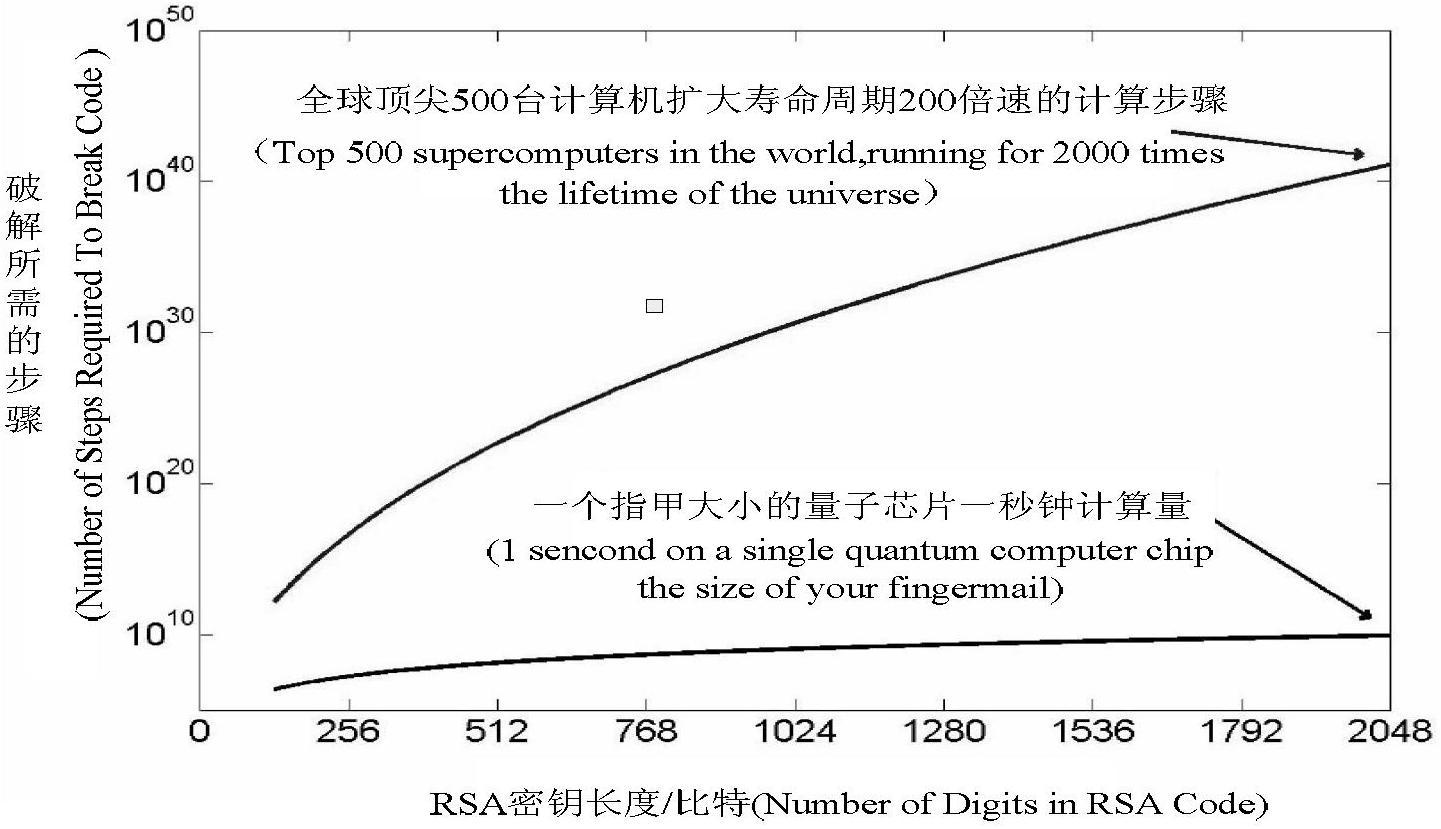
[0135] Because CPK has a structure that can deal with quantum computing attacks, it is possible to construct a system that is also viable in the quantum era. CPK adopts the method of making quantum exhaustive calculation meaningless to deal with the exhaustive attack of quantum computing, so that the current public key system can still have vitality. Such as solving the equation: (a+b)mod 13=7, mental arithmetic can also be solved, but this equation is an infinite solution, because the solution of the infinite solution equation or multi-solution equation has nothing to do with the operation speed, exhaustive enumeration can be invalidated. Any exhaustive enumeration is ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More