High-interaction honeypot based network security system and implementation method thereof
A honeypot and network technology, applied in the field of network security systems based on high-interaction honeypots, can solve the problems of inability to analyze attack events, discover unknown attacks, and fail to discover unknown events, etc., to achieve the effect of improving application value
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
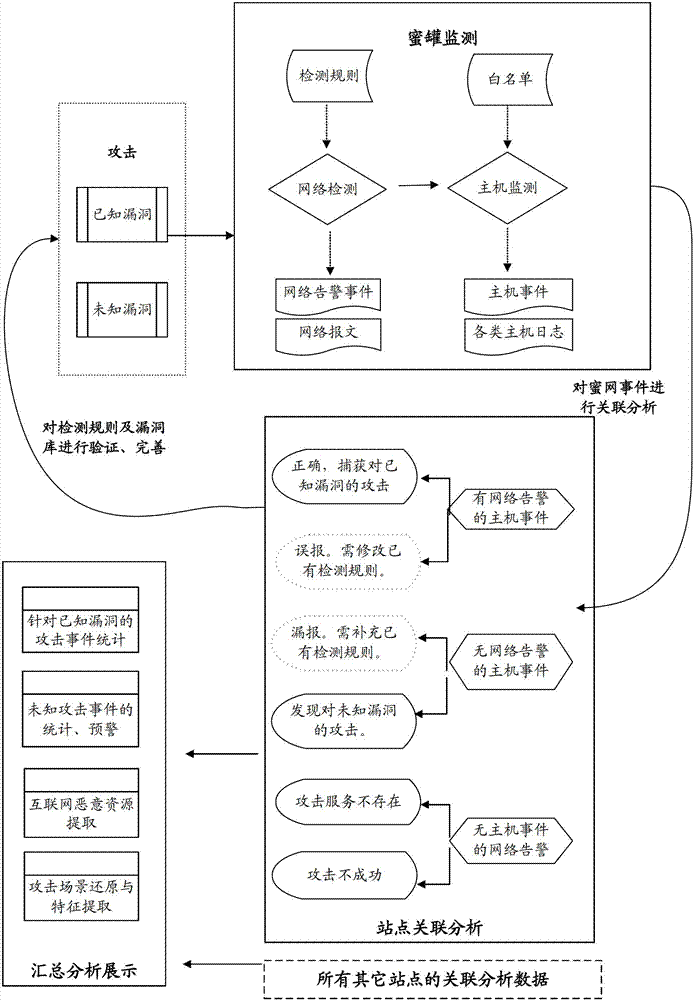
[0023] In order to solve the above-mentioned technical problems in the prior art, the present invention provides a network security system and implementation method based on high-interaction honeypots, which can automatically discover unknown attack events and restore attack scenarios from many high-interaction honeypot logs, It also supports active detection of malicious download resources on the Internet controlled by attackers. The present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
[0024] System embodiment
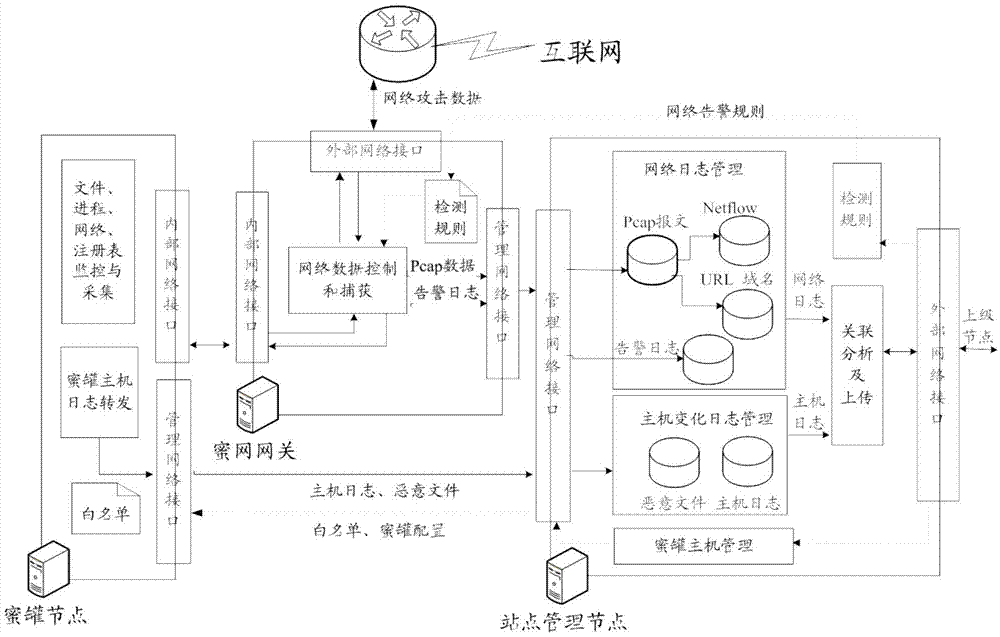
[0025] According to an embodiment of the present invention, a network security system based on a high-interaction honeypot is provided, figure 1 is a schematic structural diagram of a network security system based on a high-interaction honeypot ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More