Data protection method and system based on homomorphic encryption
A homomorphic encryption and data protection technology, applied in the field of information security, can solve problems such as user behavior and habits, privacy leakage, user data tampering, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
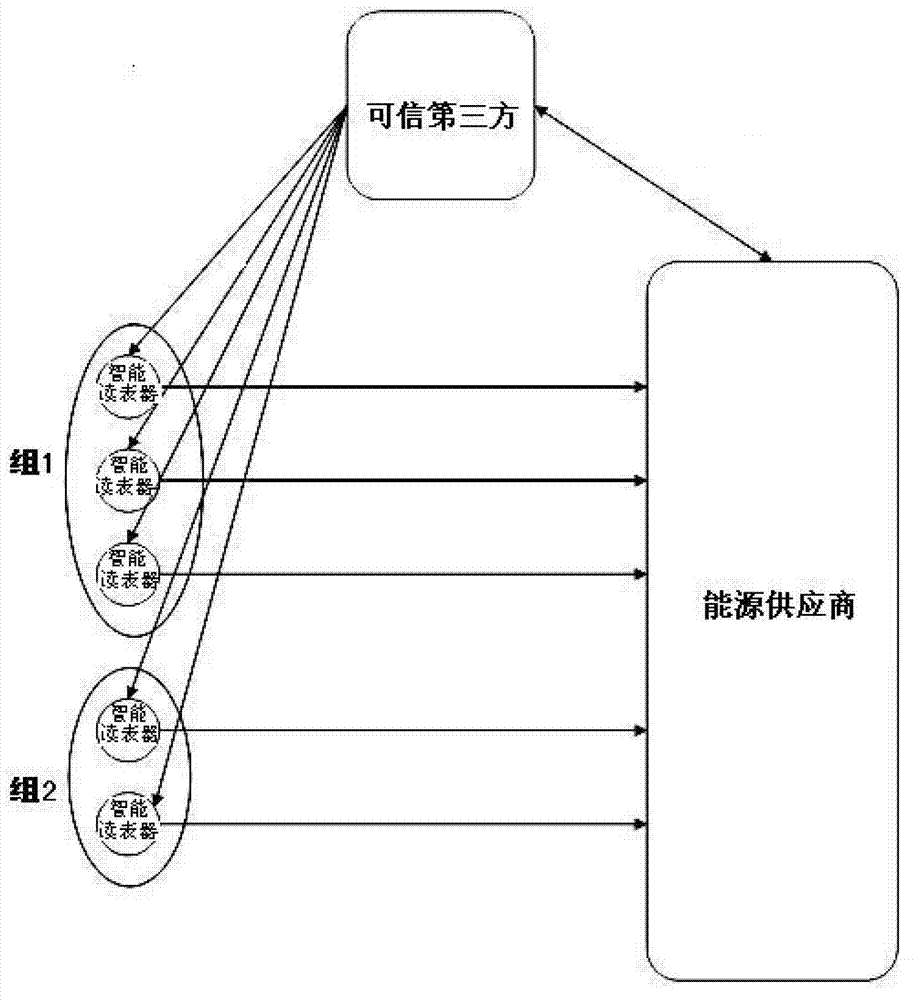
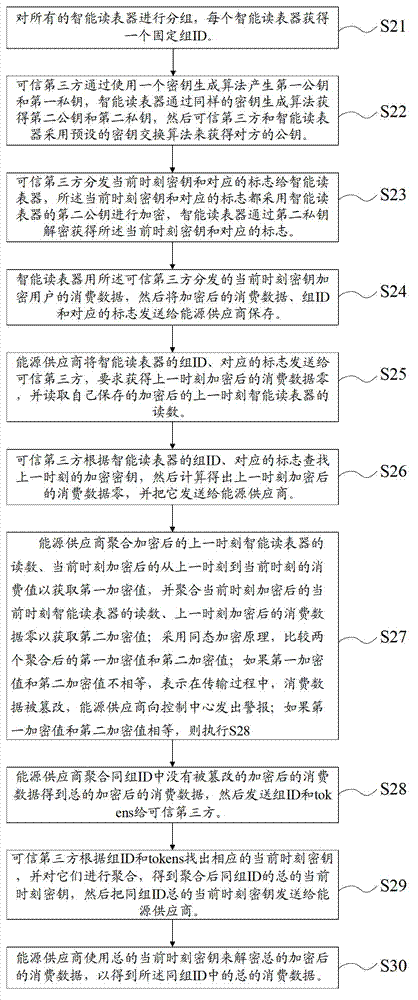
[0080] Please refer to Figure 4 , Figure 4 It is a schematic diagram of the principle of the homomorphic encryption-based data protection method and system of the present invention. based on Figure 4 The working principle shown can detect whether the user's consumption data in the first embodiment is tampered with by the adversary during the communication process.
[0081] S1, S2, and S3 represent three smart meter readers existing in group 1, respectively. At time n-1, the keys they use to encrypt consumption data are K1 n-1 、K2 n-1 、K3 n-1 , the readings of the smart meter reader are B1 n-1 、B2 n-1 、B3 n-1 ; At the nth moment, the keys they use to encrypt consumption data are K1 n 、K2 n 、K3 n , and the key for encrypting consumption data changes from time n-1 to time n, that is, K1 n-1 different from K1 n , the readings of the smart meter reader are B1 n 、B2 n 、B3 n . The consumption data recorded by the smart meter reader from time n-1 to time n are resp...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More