Identity-based file encryption transmission method
A file encryption and transmission method technology, applied in the field of identity-based file encryption and transmission, can solve the problems of complicated user usage and cumbersome background management.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
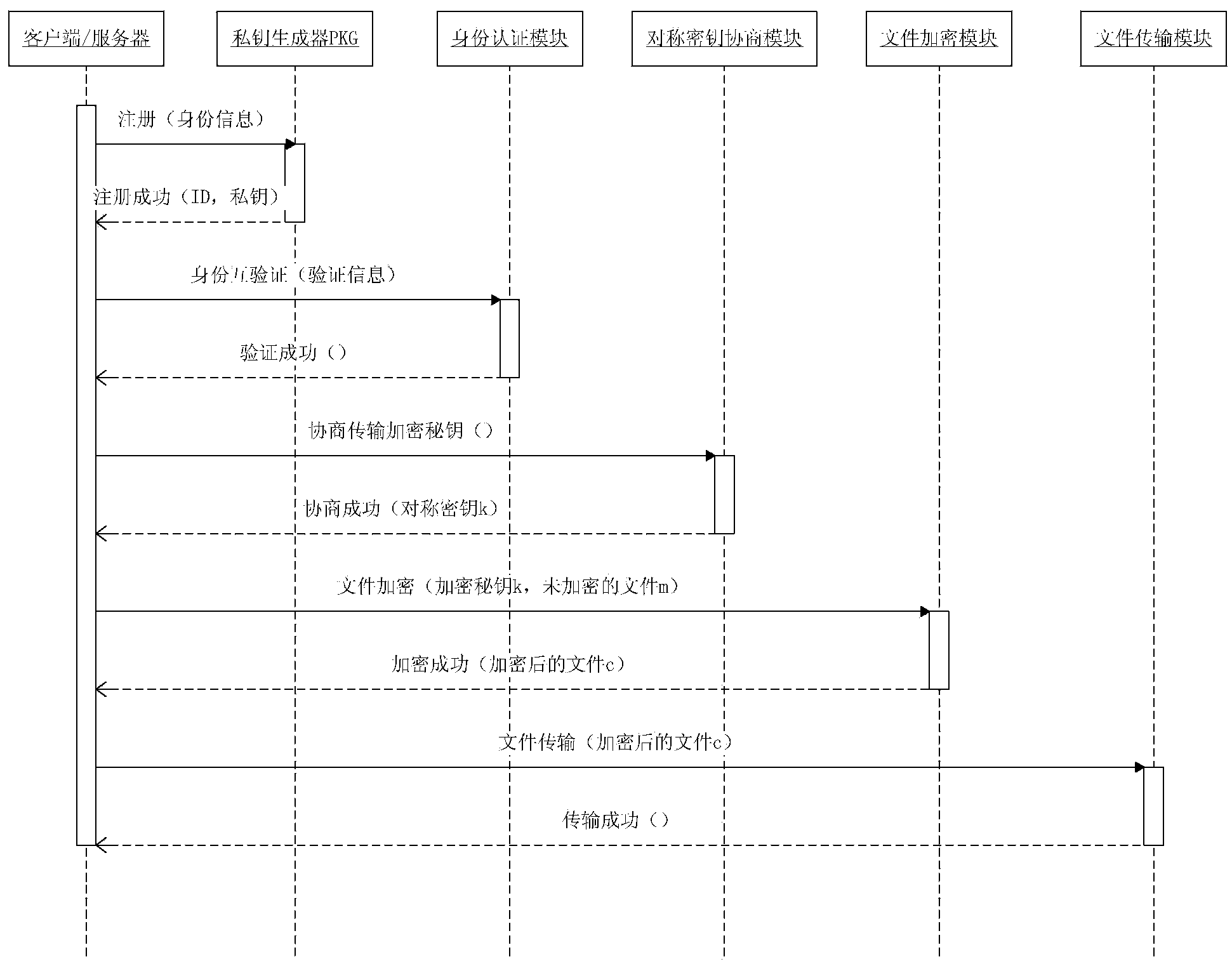
[0042] In order to facilitate a further understanding of the method of the present invention, preferred embodiments are described in detail below in conjunction with the accompanying drawings.
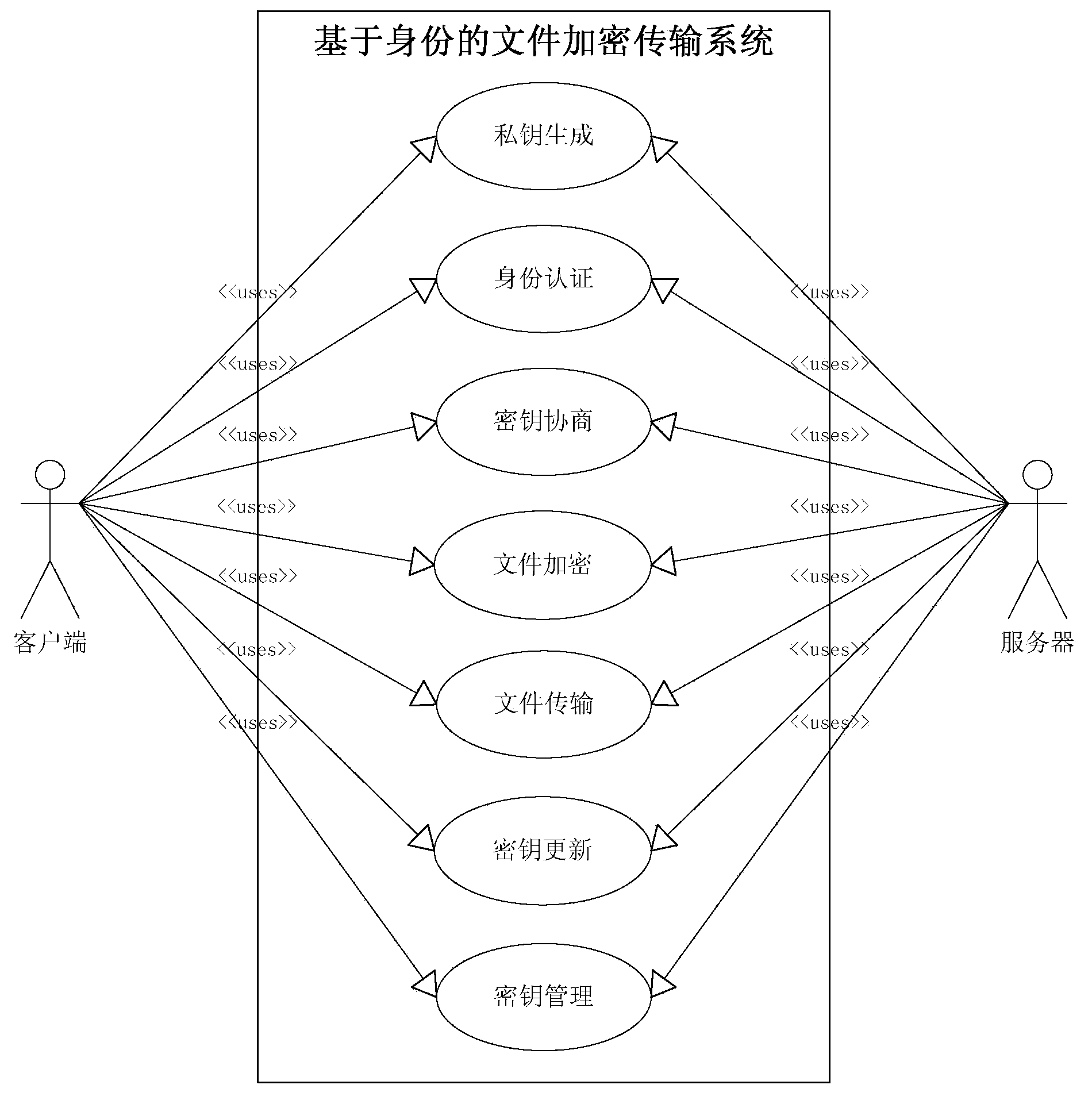
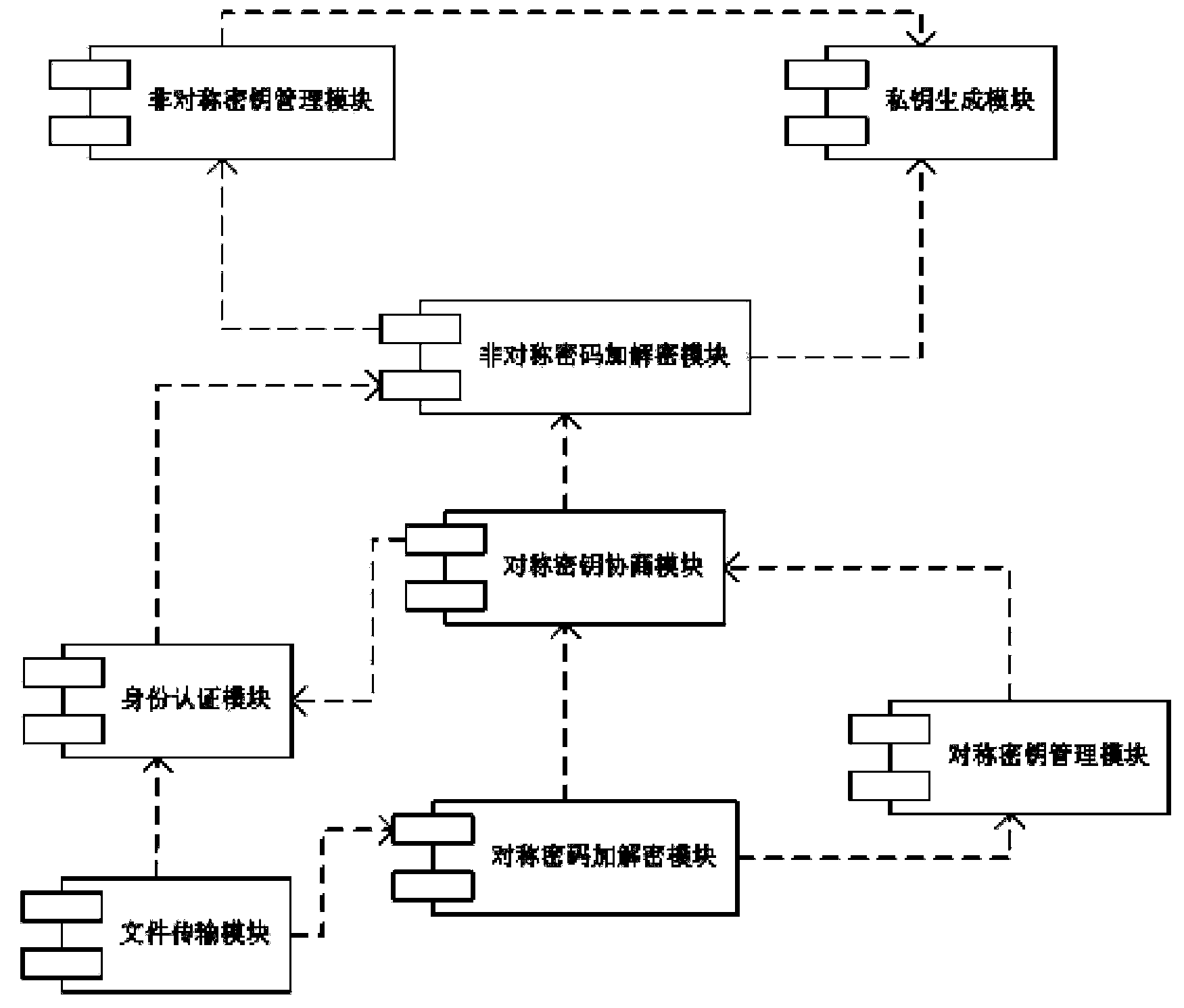
[0043] The identity-based file encryption transmission method of the present invention is applicable to a system based on the FTP (File Transfer Protocol, file transfer protocol) protocol client / server architecture, based on the identity encryption (IBE, Identity Based Encryption) algorithm, for the Internet A relatively complete implementation scheme is proposed for the safe transmission of files between communication parties in the environment. The methods include authentication methods, symmetric key negotiation methods, encrypted file transfer methods, key update methods, and key management methods (such as figure 1 shown).
[0044] The file security transmission method proposed by the present invention can be briefly described as:
[0045] In the identity-based encryption (IBE) ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More