Method and device for detecting weak password in network
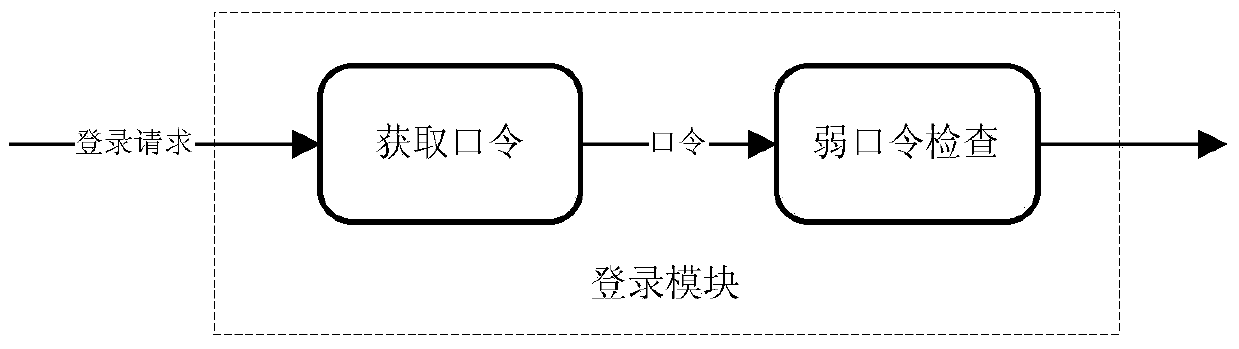
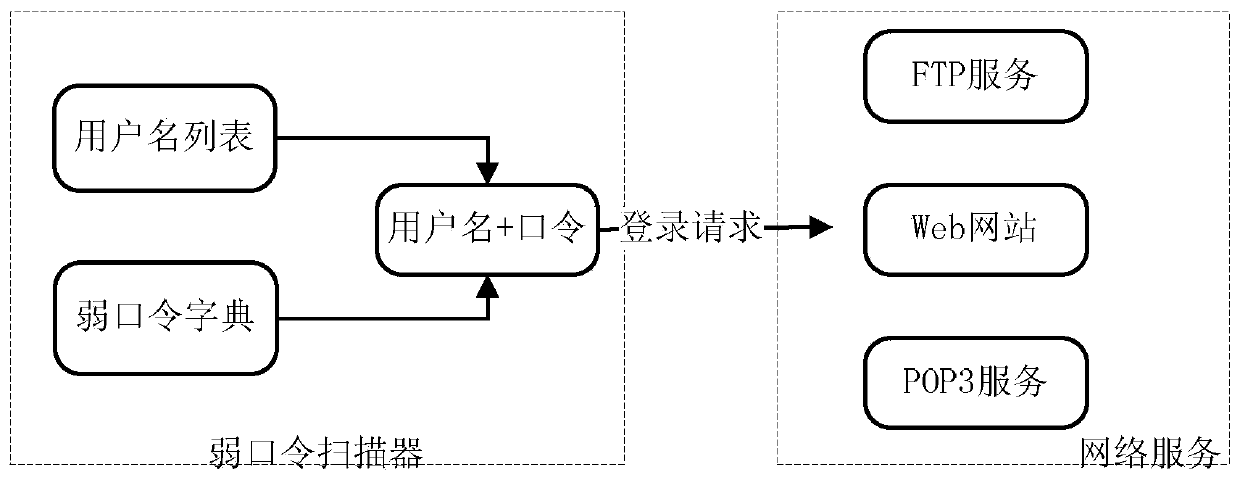
A weak password and password technology, applied in the Internet field, can solve the problem of high missed detection rate of weak passwords, and achieve the effects of convenient management, comprehensiveness, and flexible deployment.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
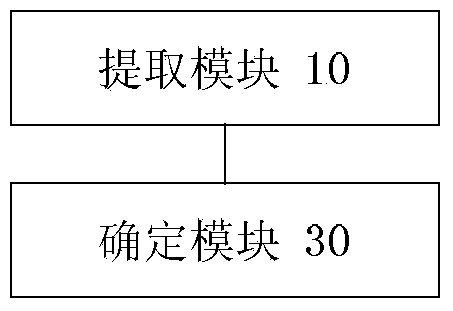
Method used
Image
Examples
Embodiment Construction
[0036] First of all, some nouns or terms appearing in the process of describing the embodiments of the present invention are applicable to the following explanations:
[0037] Password policy, passwords can protect files or data by encrypting files or data. The password protection level is based on the structure of the password. The higher the complexity of the password, the harder it is for people to guess the password, which can provide better security. The password policy reflects the construction of the password. Password policies can be applied to logins for SQL Server authentication and to contained database users with passwords.
[0038]For constructing VPN, network tunneling (Tunnelling) technology is a key technology. Network tunneling technology refers to the technology of using one network protocol to transmit another network protocol, and it mainly uses the network tunneling protocol to realize this function. The network tunnel technology involves three network p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More